Introduction
Deep web marketplaces are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity of the dark web. The goods and services on offer range from leaked credit card details, exploit kits, and hackers for hire to advertisements for hitmen services.
Because of the range of goods and services found for sale and the conversations that occur around these sales, dark web marketplaces can be precious sources of data on criminal activity. As such, they are normally under intense scrutiny from law enforcement and security professionals alike.
First Deep Web Black Markets
People have been organizing illicit trades via the Internet since the 1970s. Those early examples, though, were through closed networks, and the actual exchanges of money and goods generally had to take place in person. With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail but easy. As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created.
The very first of these marketplaces to pair the darknet with Bitcoin was the Silk Road. Silk Road was created by Ross Ulbricht in February 2011. Over the next two years, the Silk Road set the standard for darknet marketplaces. By the time it was shut down in October 2013 and Ross Ulbricht arrested, the site had traded an estimated $183 million worth of goods and services.
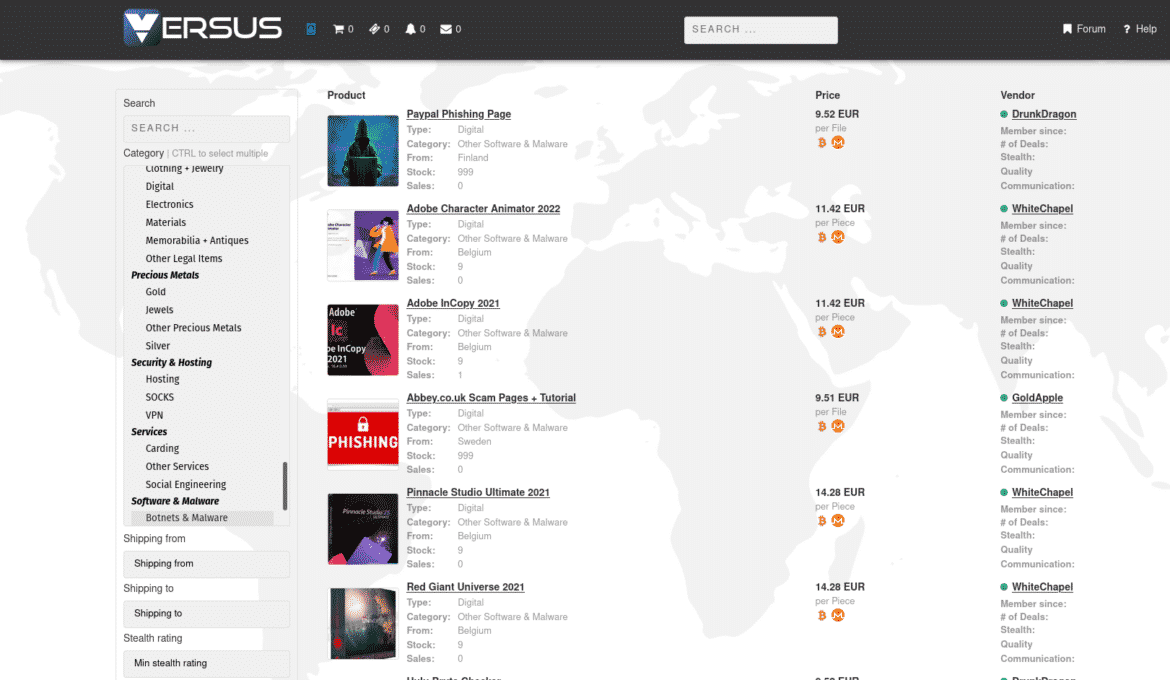
Versus
Established in 2019, Versus quickly gained a reputation for a user-friendly UI and intuitive search options. It has gained a lot of users and has become a popular marketplace due to its focus on security. Buyers can purchase a range of digital goods and services, which include illicit drugs, software and malware, and services related to fraud. The marketplace has over 8,400 listings and 500 vendors who communicate in English and accept Bitcoin for transactions.
TORREZ
ToRReZ Market is a wallet-less market, which means you only send funds when making an order. Currently, the market supports four cryptocurrencies: Bitcoin, Monero, Litecoin, and Zcash. Both physical goods, such as drugs, and digital goods, such as software and credit cards, are sold on the ToRReZ Market.
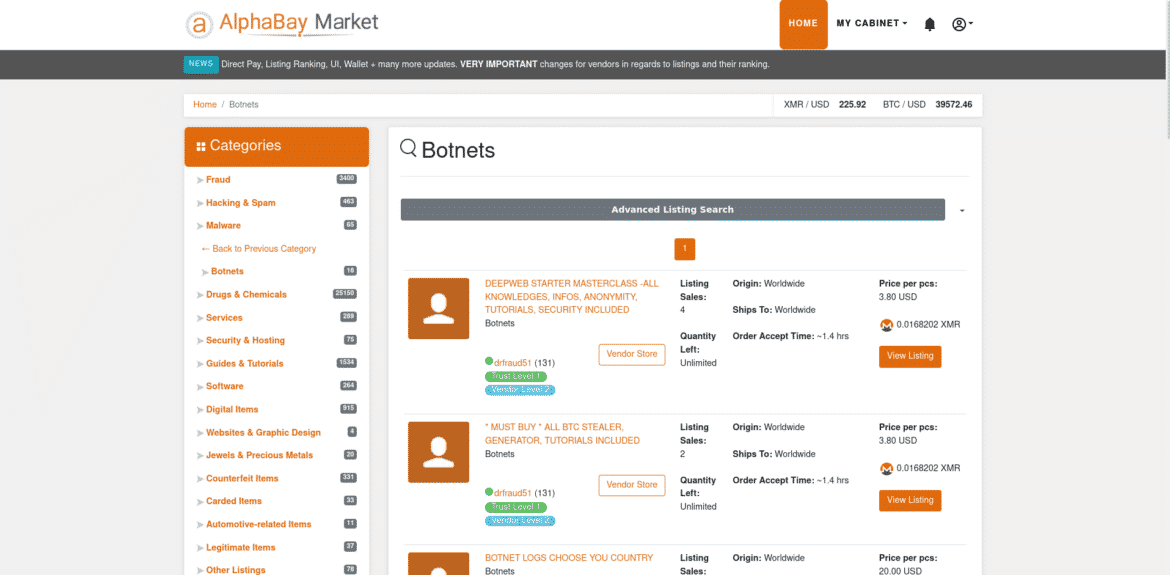
AlphaBay Market
Alphabay Market was originally operating from 2014 to 2017 with alpha02 and DeSnake as admins and was the biggest darknet market in history. However, in July 2017, AlphaBay suddenly went offline. It was suspected as an exit scam; however, a few days after it had gone offline, it was revealed that AlphaBay had been seized and alpha02, aka Alexander Cazes, was caught.
AlphaBay was relaunched by DeSnake in August 2021 with a new design but with the same admin as before and is once again planning to become the biggest darknet market in history.
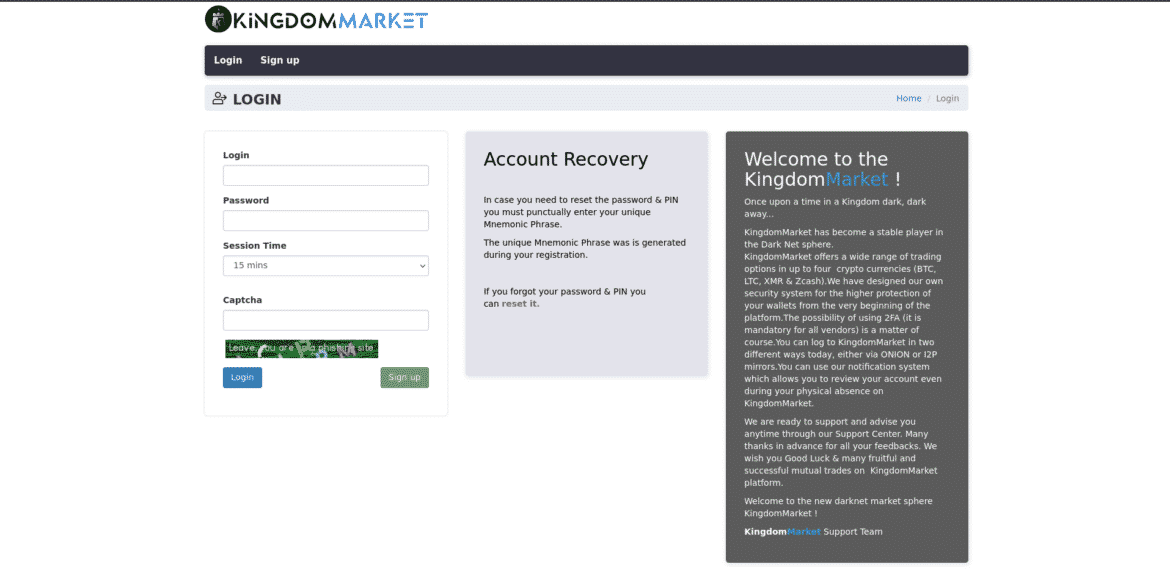
Kingdom Market
Kingdom Market is a newer darknet market that has been around since April 2021 but was only recently vetted for listing on Dread, the pre-eminent forum for markets on the dark web. It features a unique site design unlike any other market yet is still intuitive and easy to use. Conspicuously absent are some preferred features, such as the lack of pre-order (direct pay) purchases, a multi-sig option for BTC payments, and forced PGP encryption for communications. It makes up for this with enhanced security and user safety features, helping users to ensure they are not getting phished.
TOR2DOOR
Tor2door is a darknet marketplace that launched in June 2020. The market is built from scratch and has a unique design. Tor2door claims that security and usability are its main priorities. This market is one of the easiest to use and is very simple for inexperienced dark-net users.
Real-World Examples: Data Breaches Feeding Dark Web Black Markets
Dark web black markets thrive on the sale of stolen data, often sourced from large-scale data breaches. Below are some recent examples that highlight the scale of this issue:
1. National Public Data Breach (2024)
In April 2024, a data broker company, National Public Data, suffered a catastrophic breach, exposing 2.9 billion records.
This trove of stolen data included names, addresses, Social Security numbers, and phone numbers, leaving millions of individuals vulnerable to identity theft. Shortly after the breach, a hacker group known as USDoD listed this data on dark web marketplaces, pricing it at a staggering $3.5 million.
2. Dell Customer Data Breach (2024)
In early 2024, Dell reported a breach compromising approximately 49 million customer records collected over seven years.
The exposed data included customer names, addresses, and purchase details. Shortly after the breach, these records appeared on dark web forums, where they were sold to malicious actors aiming to exploit customers through targeted scams and phishing attacks.
3. Ticketmaster Data Breach (2024)
In May 2024, Ticketmaster faced a significant data breach affecting millions of customers. The stolen data included names, contact information, and order histories. Dark web listings surfaced almost immediately after the breach, advertising this information for sale to cybercriminals.
How Brandefense Helps Mitigate These Threats
Data breaches like the ones mentioned above highlight the significant threats posed by dark web black markets. Stolen data can quickly transition from legitimate systems to underground forums, where it becomes a valuable commodity for cybercriminals. To counter these risks, organizations need robust, proactive solutions that go beyond traditional cybersecurity measures. This is where Brandefense’s Dark Web Monitoring Solution plays a critical role.
What is Dark Web Monitoring?
Brandefense’s Dark Web Monitoring is a comprehensive solution designed to continuously track and analyze activity across hidden layers of the internet, including the dark web, deep web, and hacker forums. This solution focuses on identifying stolen data, brand misuse, and potential threats before they can cause significant harm. With Brandefense, businesses gain early visibility into risks that may otherwise remain undetected until it’s too late.
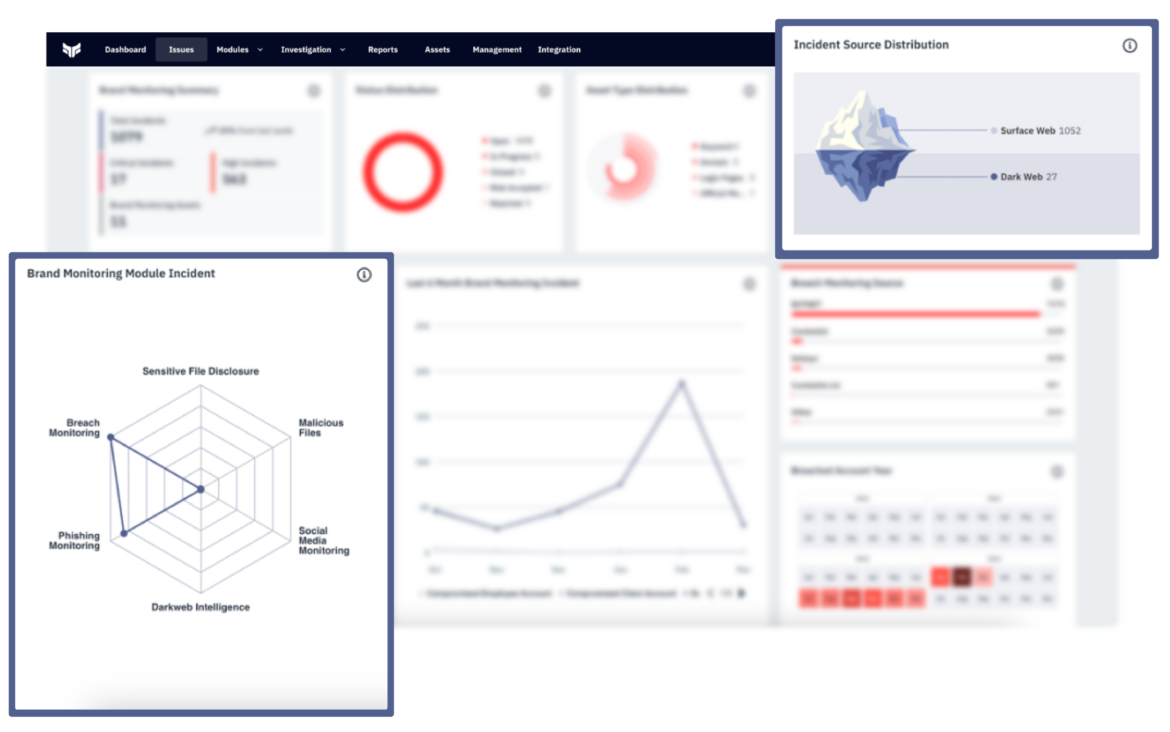
Key Features of Brandefense’s Dark Web Monitoring Solution
- Proactive Threat Detection: Brandefense continuously scans dark web forums, marketplaces, and encrypted communication channels for mentions of your organization, brand, or sensitive data.
- Comprehensive Coverage: Extensive monitoring across the entire dark web ecosystem, including TOR-based websites and private forums.
- Customizable Alerts: Tailored monitoring with specific keywords or parameters to suit unique business needs.
- Advanced Analytics and Reporting: Actionable insights with detailed analytics for informed risk mitigation.
- Integration with Incident Response: Seamless integration with existing cybersecurity infrastructure for rapid action.
- Protection for Customers and Brand Reputation: Safeguards sensitive customer data and protects brand reputation.
Why Choose Brandefense?
- Early Detection: Stop threats before they escalate into significant breaches.
- Real-Time Alerts: Act on risks as they emerge.
- Customizable Solutions: Tailored to your industry and specific needs.
- Trusted Expertise: Backed by a team of cybersecurity professionals with years of experience in dark web intelligence.

Conclusion: Safeguard Your Brand Against Dark Web Threats
The dark web remains a mysterious yet highly dangerous part of the internet, where illicit activities and black markets thrive. While it offers anonymity for legitimate purposes, it is also a haven for cybercriminals. As explored in this article, the top dark web black markets demonstrate the growing sophistication and scale of these underground networks.
For businesses and individuals alike, understanding these threats is the first step in securing their digital assets. However, combating dark web risks requires more than just awareness—it demands proactive and comprehensive protection.
Brandefense is your trusted partner in this journey. With advanced dark web monitoring, threat intelligence, and brand protection services, we help you uncover hidden dangers, prevent data breaches, and safeguard your reputation. Our platform ensures that your brand stays one step ahead of cybercriminals, giving you peace of mind in an increasingly complex digital landscape.
Take control of your cybersecurity today. Explore how Brandefense can empower your brand to thrive securely, even in the shadow of the dark web.






