The Godfather trojan was developed using the source code of another banking trojan called Anubis. However, The Godfather differs from Anubis with its updated functionality, such as updated command and control (C&C) communication, traffic encryption algorithm, a new module for managing virtual network computing (VNC) connections, and Google Authenticator OTPs. The Godfather is distributed through fake apps hosted on Google Play. Fake pages are placed on Godfather-infected devices. These fake web pages are opened when users click on fake notifications or open legitimate apps targeted by the Godfather. All data entered on these pages (usernames and passwords) is sent to command and control (C&C) servers.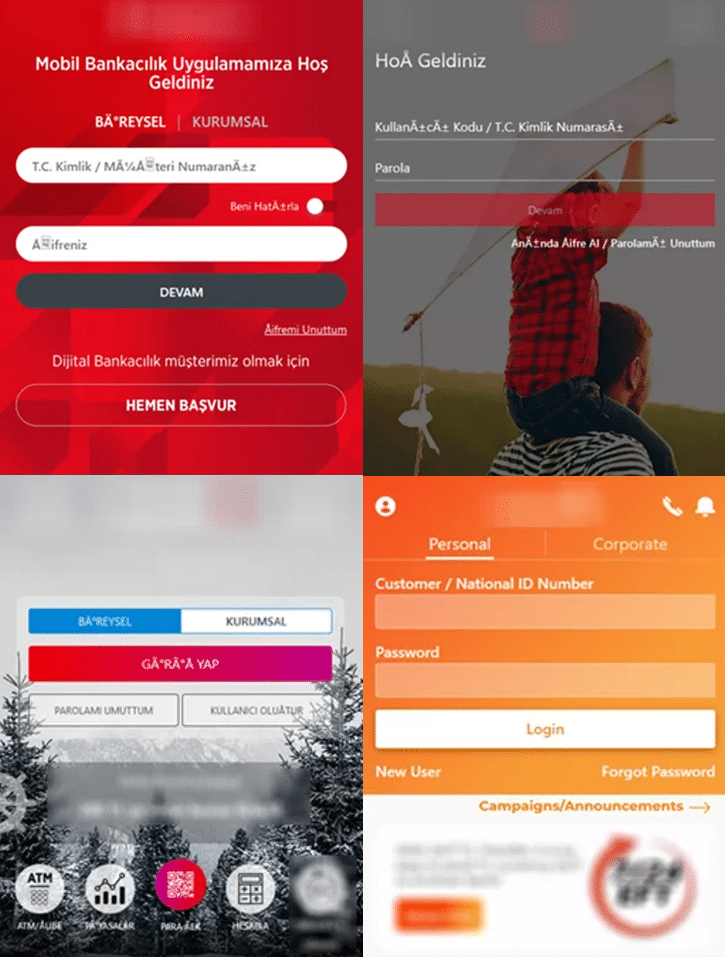
- Recording the device’s screen
- Creating VNC connections
- Capturing keystrokes (keylogging)
- Leaking push notifications and SMS messages (to bypass 2FA)
- Send SMS messages
- Forward calls
- Execute USSD requests
- Start proxy servers
- Enabling silent mode
- Establishing WebSocket connections
A Godfather sample analyzed in September 2022 was observed to mimic Google Protect. When a user launches a malicious application, the application imitates the legitimate Google application, but the Godfather activities are running in the background. Once the malware is launched, it persists on the infected device, creates a pinned notification, and hides its icon from the list of installed apps. Considering these details, it is recommended to consider the following security recommendations to avoid being a victim of targeted attacks that the Godfather malware may carry out.
- Emails, attachments, and links from unknown parties should not be respected.
- Downloaded applications should be downloaded from legitimate application stores, and by checking the evaluations made,
- Comprehensive security solutions should be used.






