What is Hybrid Warfare?

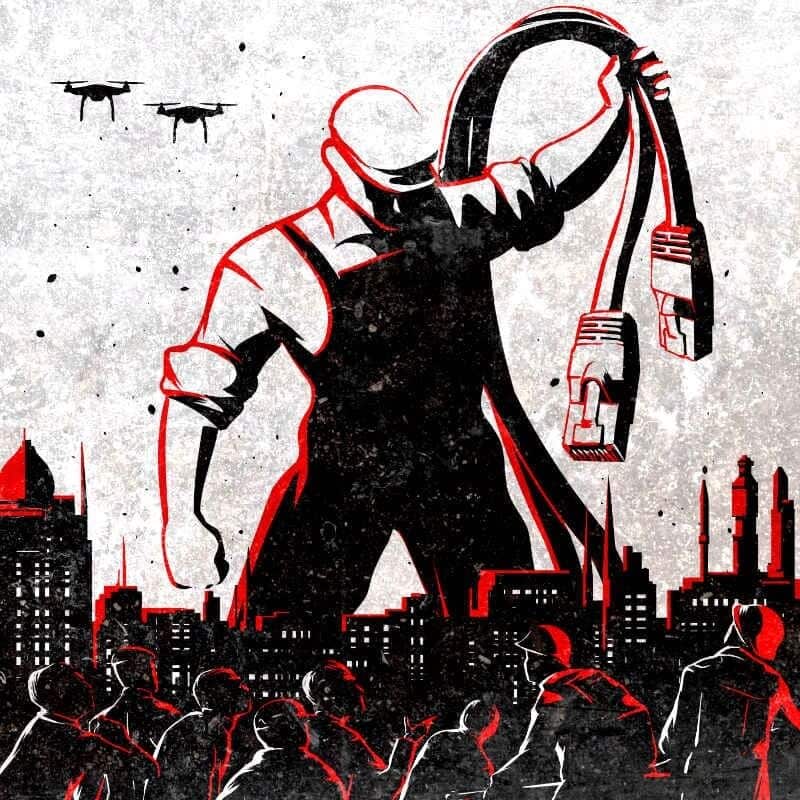
The deployment of new technology that allows changeable intensity and strategies in combat has resulted in a reformulation of both the philosophy and art of war, according to analyses of geopolitical and geostrategic contexts. When these new approaches are integrated with classic conflict and security understandings, they are referred to as “hybrid warfare”.
The notion of hybrid warfare, which combines conventional and unconventional/irregular warfare and extends beyond the battlefield to include economic, diplomatic, cyber, and political warfare, is not new.
Role of Cyber Attacks in Hybrid Warfare

These increasingly sophisticated cyber-attacks represent a new type of warfare aimed at disorganizing and even destroying a nation’s economy. This has been called “hybrid warfare.” These attacks Are a mixture of conventional and unconventional methods used against a much stronger adversary that aims to achieve political objectives that would not be possible with traditional warfare.
The problem is often identifying the culprits. In hybrid warfare, the state responsible for the actions will often use non-state actors, which allows it to deny responsibility. But over the past two decades, many cyber-attacks targeting Western state institutions and businesses have been far more sophisticated than a couple of tech-savvy individuals operating as “lone wolves” and bear the hallmarks of actions taken with the support or approval of a hostile government.
The scale of cyber-attacks is conducted at a military level signals the involvement of state actors behind the scenes to organize or encourage these attacks. Russia has emerged as one of the international actors that have developed a sophisticated cyber warfare strategy.
Cyber Attacks Against Turkey After Shooting Down Russian SU-24 Aircraft
On the morning of 24 November 2015, the news that the Turkish F16s had dropped a Russian Su-24 airplane that violated the airspace had a shocking effect worldwide. This event deepened quickly and reached serious proportions between Turkey and the beginning of the RF, which has created political tensions. This political tension moved into a new phase with the Distributed Denial of Service (DDoS) attacks against Turkey on 14 December 2015, at 12:00. The attacks have caused deepening political tension in relations between the two countries.
On 23 December 2016, a video was broadcast by the Anonymous Hacker Group about the attack. Posted Videos claimed that Turkey supports the Islamic State of Iraq and Syria (DAESH), Turkey gets oil illegally from DAESH, and terrorists from DAESH are being treated in Turkey. It is also claimed that this disclosure is part of the false flag operation1 planned by the Russian Service Services (RIS).
It is still quite difficult to make a clear assessment of the damage caused by the attacks. For example, it is common for Western countries to make public statements about the agencies involved in dealing with the cost of the damage resulting from such attacks or virus outbreaks. However, there is not yet an institution to carry out such a study in our country. After the attacks, it should be noted that in December 2015, when attacks continued, 10% of visitor losses were reported on sites with high visitor traffic “com.tr”
The fact that the attack has a capacity of 276,000 different addresses and 30-40 GB size from time to time, considering this huge capacity, it can be easily evaluated that this DDoS attack can be planned with just support from a state organization.
Also, at least 400,000 websites were affected by these attacks, and these sites just belonged to the e-government system, public universities, and financial institutions. At that time, there was ongoing high tension between RF and Turkey because of the shooting down Russian SU-24. Also, This cyber-attack did not target the entire internet system in Turkey; only official internet sites were targeted by these attacks.
The Role of Cyber War in the Russia-Ukraine Hybrid War
The Russian-Ukrainian cyberwar is an offshoot of the conflict between Russia and Ukraine since the collapse of the Soviet Union in 1991. The first attacks on Ukraine were seen during the mass protests in 2013. The series of attacks, called Operation Armageddon, is thought to have been made to aid Russia on the battlefield. Between 2013 and 2014, some information systems of Ukrainian government agencies were affected by a computer virus known as Snake or Turla. In February-March 2014, when Russian troops entered Crimea, communication centers were raided, and Ukraine’s fiber optic cables were destroyed, cutting off the connection between the peninsula and Ukraine. In addition, Ukrainian Government websites, news, and social media were shut down or targeted in DDoS attacks, mobile phones of many Ukrainian parliamentarians were hacked. Experts stated that after this incident, the Russia-Ukraine cyberwar started. The targets of Russian cyberattacks were Ukrainian state institutions, the EU, the USA, defense institutions, international and regional defense and political organizations, think tanks, media, and Russian dissidents. Researchers have identified two Russian hacker groups active in the Russian-Ukrainian cyberwar after 2015: APT29 (also known as Cozy Bear, Cozy Duke) and APT28 (Sofacy Group, also known as Tsar Team, Pawn Storm, Fancy Bear). More than a dozen Ukrainian government websites were hijacked or crashed in attacks thought to have originated from Russia during the 2021–2022 Russo-Ukrainian crisis. According to Ukrainian officials, about 70 government websites were hacked, including the Ministry of Foreign Affairs, the Cabinet, and the Security and Defense Council.
Just before Russia began invading Ukraine on 24 February, it targeted Ukrainian government websites with distributed denial-of-service (DDoS) attacks. Cyber security firms announced that they had detected the distribution of malware called HermeticWiper, which targets devices in Ukraine.
This series of attacks followed shortly after the DDOS and WhisperGate attacks on Ukrainian government websites distributed as phishing software.
Russia’s most effective attacks on Ukraine
- Operation “Armageddon”, 2013
- Operation “Snake”, February 2014
- Attacks on the automated system “Elections” June 2014
- Ukraine power grid hack, December 2015. Attacks using the Trojan virus BlackEnergy on energy companies in Ukraine which provide energy to Kyiv, Ivano-Frankivsk, and Chernivtsi regions This was the first successful cyberattack on a power grid.
- Second Ukraine power grid hack, December 2016.
- Paralysis of the State Treasury of Ukraine, December 2016
- 2022 Ukraine cyberattack, attacks on Ukrainian government websites, January
- 2022, one day after US-Russian negotiations on Ukraine’s future in NATO failed.
- Attacks in February 2022, after Russian troops invaded eastern regions of Ukraine, took down several major Ukrainian governmental and banking websites. US intelligence attributed the attacks to Russian attackers, although the Russian government denied involvement.
Ukraine’s Most Effective Attacks on Russia
- Operation “Prikormka (Groundbait)”, May 2016
- Operation “9 May”, 2016 (9 successful hacks of the sites of the separatist group “Donetsk People’s Republic” as well as Russian sites of anti-Ukrainian propaganda and resources of Russian private military companies.)
- “Channel One” break, June 2016 (hacking of the corporate server of the Russian “Channel One” by the Ukrainian Cyber Alliance of hackers FalconsFlame, Trinity, and Rukh8)
- The Surkov Leaks is October 2016 — a leak of 2,337 e-mails and hundreds of attachments, which reveal plans for seizing Crimea from Ukraine and fomenting separatist unrest in Donbas (documents dated between September 2013 and December 2014).
- The IT Army of Ukraine was established by Mykhailo Fedorov, the First Vice Prime Minister and Minister of Digital Transformation, on 25 February 2022. The effort was initiated during the 2022 Russian invasion of Ukraine. The primary aim is cyber warfare against Russia. Fedorov requested the assistance of a cyber specialist and tweeted a Telegram with a list of 31 websites of Russian business and state organizations.
Possible Effects of the Russia-Ukraine Cyber War on the Future of Cyber Warfare
Considering that the US and EU have come together to support Ukraine, it is thought that the scope of cyberwar may expand. Large-scale cyber conflicts can become global due to spillover effects. Officials in both the US and UK have warned businesses to be alert to suspicious activity on their networks from Russia.
Nations Have Begun Cyber Preparations
As the Russia-Ukraine crisis escalates, countries around the world have taken notice and begun preparations. Proactive measures and warnings have come from the highest levels of government, indicating that the threat of cyberwarfare is imminent.
United States
- The FBI, Cybersecurity and Infrastructure Security Agency (CISA), and the National Security Agency put out a joint advisory in January entitled, “Understanding and Mitigating Russian State-Sponsored Cyber Threats to US Critical Infrastructure.” CISA also warned US companies to protect their IT systems against destructive wiper malware, which has been used against targets in Ukraine.
- The New York Department of Financial Services issued an alert to financial institutions in late January, warning of retaliatory cyberattacks should Russia invade Ukraine and trigger US sanctions.
United Kingdom
- Britain’s National Cyber Security Centre warned large organizations to bolster their cybersecurity resilience amid the deepening tensions over Ukraine by patching systems, enabling multifactor authentication, and backing up data, among other steps.
Germany
- Mark Branson, head of the German Federal Financial Supervisory Authority (BaFin) told an online conference that cyberwarfare was interconnected with geopolitics and security.
Poland
- Poland recently raised its nationwide cybersecurity terror threat in the wake of a cyberattack on Ukraine last week, adding that the new alert level was preventative.
European Union
- The European Central Bank is preparing banks for a possible state-sponsored cyber attack as tensions with Ukraine mount.
Conclusion
As we can see through the example of Russia-Ukraine, cyber-attacks are seen as gradual attrition. It was observed that the planned attacks on the countries’ critical infrastructures, especially before the attack, left the countries in a difficult situation. Considering all these, it is seen that the need for institutions for cyber intelligence data will increase.
References
- Danyk, Y., Maliarchuk, T., & Briggs, C. (2017). Hybrid War: High-tech, Information, and Cyber Conflicts. Connections, 16(2), 5–24.
- http://www.jstor.org/stable/26326478
- https://www.securityweek.com/russia-vs-ukraine-war-cyberspace
- https://www.securityweek.com/cyberattacks-ukraine-new-worm-spreading-data-wiperransomware-smokescreen
- https://www.securityweek.com/destructive-hermeticwiper-malware-targets-computersukraine
- https://www.securityweek.com/microsoft-uncovers-destructive-malware-used-ukrainecyberattacks
- https://en.wikipedia.org/wiki/2022_Ukraine_cyberattacks
Authors:
Uğur Ateş
Mehmet Fatih Okuyan
Cemal Tiryaki






