The vulnerability, AttachMe, compromises the security of cloud isolation by allowing threat actors to access other users’ OCI storage volumes without permission, capture and modify sensitive data stored on the volume, and execute code on affected systems. Successfully exploiting the vulnerability requires threat actors to capture the Oracle Cloud Identifier provided to an Oracle Cloud Infrastructure user and insert it into their Oracle Cloud virtual machine. Oracle Cloud infrastructure does not have a security mechanism that checks who owns this identifier. Therefore, threat actors can easily add the identifier to their virtual machines and gain access to the storage units of the Cloud customer that owns the identifier.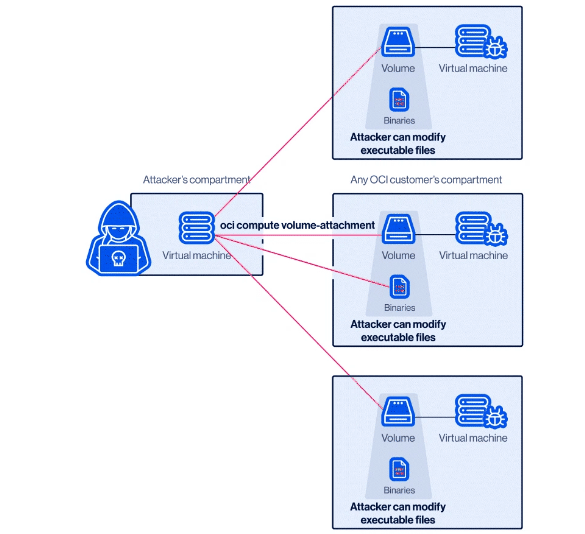
AttachMe: The Critical Vulnerability in Oracle Cloud Infrastructure
- Categories
- Latest News
-
 What Is Credential Stuffing? Attackers Don't Crack Passwords, They Buy Them
What Is Credential Stuffing? Attackers Don't Crack Passwords, They Buy Them -
 What Is Triple Extortion? The Anatomy of the Encryption + Leakage + DDoS Trio
What Is Triple Extortion? The Anatomy of the Encryption + Leakage + DDoS Trio -
 MFA Doesn't Protect You — Cookies Give You Away: The Rise of Session Hijacking
MFA Doesn't Protect You — Cookies Give You Away: The Rise of Session Hijacking -
 Fake Mobile App: How Is Your Clone on the App Store Stealing Your Users?
Fake Mobile App: How Is Your Clone on the App Store Stealing Your Users? -
 UAC-0102: Inside a Covert Espionage Operation Targeting Ukraine and Beyond
UAC-0102: Inside a Covert Espionage Operation Targeting Ukraine and Beyond
- Follow Us on Social Media!