Which APT groups & ransomware gangs were effective this month? The new malware, cyber-attacks, and more are in this monthly analysis.
Sidewinder APT: Unleashing Polymorphic Attacks on the Cyber Battlefield
Sidewinder APT Group Targets The Government Authorities and Individuals in Pakistan and Turkey with the Recent Polymorphic Attack Campaign
Recent researches showed that the Sidewinder APT group has expanded their attack capabilities and launched a multiphase polymorphic attack campaign targeting victims in Pakistan and Turkey. The campaign employs advanced techniques to evade detection by traditional signature-based antivirus (AV) systems and deliver malicious payloads.
Sidewinder, also known as Rattlesnake, Razor Tiger, APT-C-17, or T-APT-04, is an APT (Advanced Persistent Threat) group believed to originate from India and sponsored by the state. This highly sophisticated group has been conducting cyber operations since at least 2012. Their targets predominantly include government, military, telecommunication, media organizations, law enforcement, financial institutions, and business entities across the Asia-Pacific region.
Since their activities were first detected in 2018, Sidewinder has garnered attention for their advanced techniques and cyber espionage campaigns. They focus on countries such as Pakistan, Afghanistan, Bhutan, China, Myanmar, Nepal, and Sri Lanka. The group’s operations demonstrate significant sophistication, making them a formidable threat to their targets.
Typical attack chains mounted by the threat group start with spear-phishing emails containing an attachment or a malicious URL that directs the victims to an intermediary payload to drop the final-stage malware. Additionally, the adversary has been known to utilize Telegram to exfiltrate sensitive data from compromised computers.
In the campaign’s first phase, which began in November 2022, Pakistani targets were subjected to server-side polymorphic attacks. This technique modifies the appearance of malicious code through encryption and obfuscation. The use of polymorphism and server-based variations further complicates detection and analysis. Each time the server responds, it provides a different version of the file, bypassing signature-based detection. As a result, victims in the Pakistani IP range receive an RTF payload, while those outside the range receive an 8-byte RTF file containing a single string.
The attackers leverage a remote template injection flaw to deliver malicious payloads masked as documents catered to the victims’ interests. One example document discovered by researchers during the campaign had the subject line “GUIDELINES FOR BEACON JOURNAL – 2023 PAKISTAN NAVY WAR COLLEGE (PNWC).” Another pretended to be a letter of offer and acceptance for defence-related purchases. Interestingly, instead of using malicious macros within documents, the APT group exploits the CVE-2017-0199 vulnerability to deliver the payloads. This vulnerability allows them to bypass antivirus scanners and execute malicious code.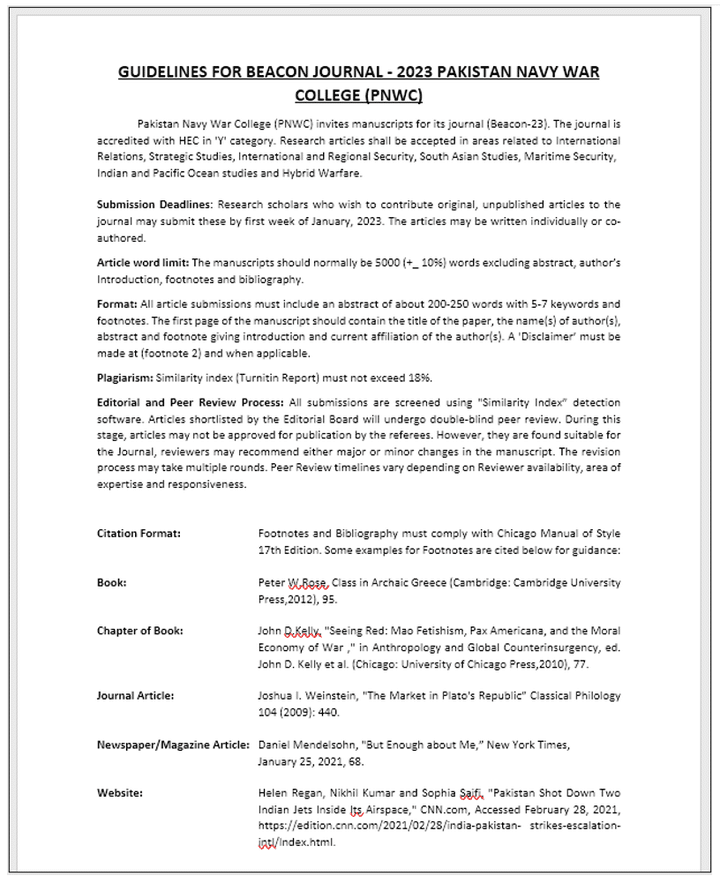
In the early March of 2023, it was discovered that the campaign had expanded to target victims in Turkey in its second phase. Researchers found a new malicious document connected to the previous attack, indicating that Turkey had become a new target country for Sidewinder. The establishment of servers delivering second-stage payloads specifically to victims in Turkey aligns with geopolitical factors, particularly the Turkish government’s support of Pakistan, which has sparked criticism from India. This suggests that regional dynamics and strategic interests influence the APT group’s choice of targets.
Take Proactive Protection With Brandefense
To protect against the ongoing threat of Sidewinder APT, regional organizations should prioritize cybersecurity and establish strong security measures. Since Sidewinder and other APT groups often use targeted spear-phishing as their initial attack method, organizations need reliable email protection solutions to isolate and examine malicious attachments safely. It’s also recommended for organizations continuously monitor their network activity and consider implementing DRPS (Digital Risk Protection Service) solutions and threat intelligence services to improve their defence against cyber attacks. By taking these proactive measures, organizations can better protect themselves against the sophisticated tactics of Sidewinder and other cyber threat actors.






