A new attack campaign targeting defense industry organizations and public institutions in various countries have been detected by Kaspersky ICS CERT researchers. Due to the overlap of techniques, tactics, and procedures (TTPs) used, the attack attributed to the TA428 APT group targets industrial facilities, design bureaus, research institutes, government agencies, and ministries in various Eastern European countries (Belarus, Russia, and Ukraine) as well as Afghanistan.
The attack starts with the distribution of phishing emails created by threat actors using internal data of the targeted organization to the targets. Microsoft Word documents attached to phishing emails contain malicious code that exploits the CVE-2017-11882 vulnerability.
Threat actors, who first gain access to the targeted system, try to distribute malware to other computers in the corporate network in later stages. For this purpose, Ladon malware, which Chinese-origin threat actors frequently use, helps TA428 threat actors to carry out Lateral Movement activities in the target network. The final stage of the attack includes capturing the target organization’s domain controller by threat actors and acquiring critical documents and files from all workstations and servers of the organization.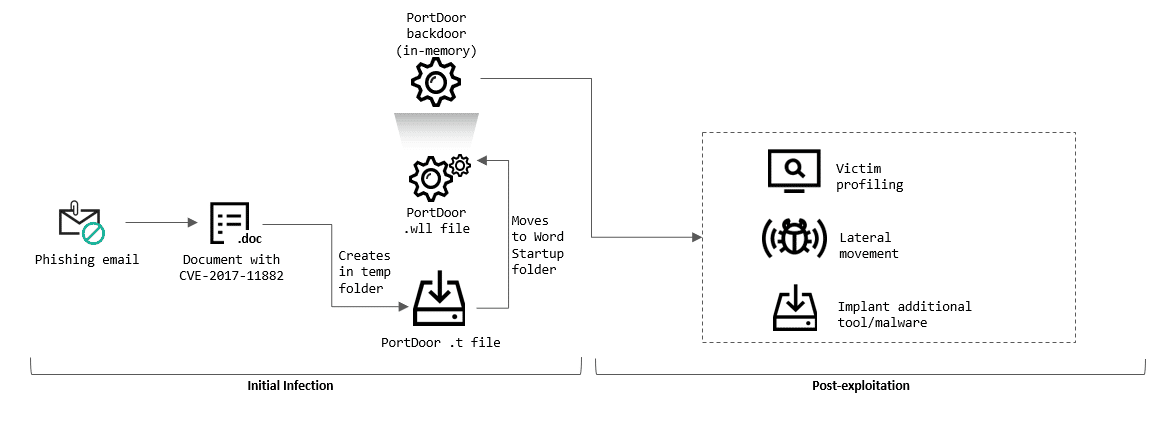
- Emails, attachments, and links from unknown, suspicious parties should not be respected.
- File/program or application downloads should be from legitimate and reliable sources.
- The installed system, program, or applications should be used in the current versions where the vulnerabilities are fixed.
- Comprehensive Anti-Virus/Anti-Malware security solutions should be used.
- Institution/organization personnel should be aware of potential phishing/social engineering attacks.
- IOC findings related to the campaign should be blocked from security solutions.






