The vulnerability tracked code CVE-2022-22274 exists due to a stack-based buffer overflow error in SonicOS’s web management interface that could cause remote code execution or a denial of service via a specially crafted HTTP request.
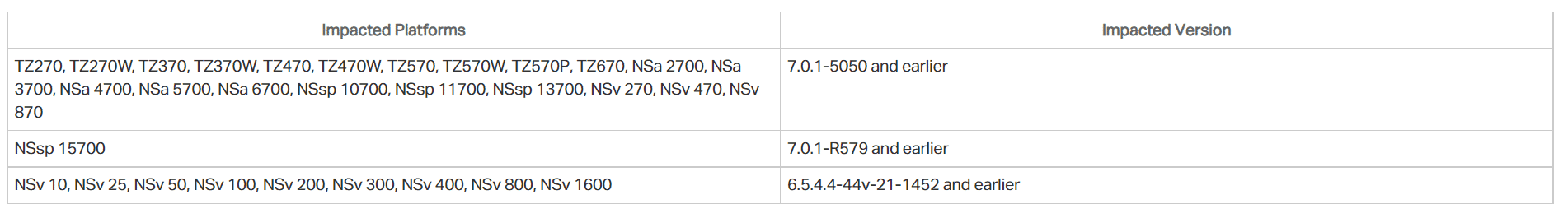
The critical vulnerability affects 31 different SonicWall Firewall solutions running the versions listed in the table below.
SonicWall stated that no evidence has yet been found for active exploitation of the vulnerability. To not be the target of attacks that can be carried out using the vulnerability, it is recommended that users who use vulnerable versions immediately apply updates that fix the vulnerability. Additionally, until updates are implemented, SonicWall advises customers to limit SonicOS management access to trusted source IP addresses.






