Frappo is a service that serves as a Phishing (PaaS) provider as a Service. The service, first known to emerge on the dark web around 22 March 2021, has been significantly improved, providing phishing pages for more than 20 financial institutions, online retailers, and popular services such as Netflix and Uber. In terms of appearance, Frappo is designed as a service that gives the impression of an anonymous crypto wallet. The original project with a similar name is currently available on GitHub, allowing developers to integrate payment methods that support Ethereum and Bitcoin. It was observed that Frappo, technically a browser extension, was added to Chrome’s online store by threat actors. Enabling the extension requires installing the browser plug-in on Firefox or Google Chrome and making payments.
It was observed that Frappo, technically a browser extension, was added to Chrome’s online store by threat actors. Enabling the extension requires installing the browser plug-in on Firefox or Google Chrome and making payments.
Frappo developers offer a variety of payment plans for threat actors based on the subscription period they choose. When Frappo is activated, the threat actors are provided with a navigation menu to create a new phishing page (phishlet). An interactive wizard is then provided that allows threat actors to configure settings, define server credentials, and select the brand to imitate.
Phishing pages categorized by brand and profiles are of high quality and contain interactive scenarios that fool targets into entering critical credentials. Threat actors successfully use PaaS platforms such as Frappo for malicious activities such as Account Import (ATO), Commercial Email reconciliation (BEC), Payment, and Identity Theft.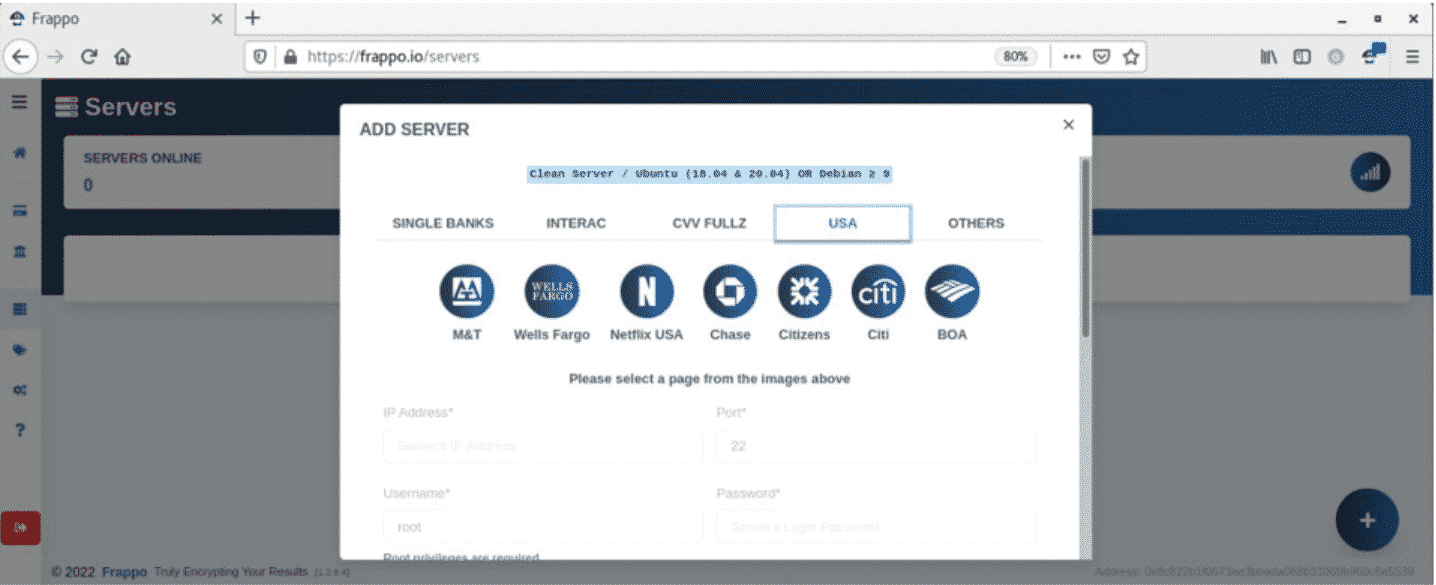 Threat actors use advanced tools and tactics to target global consumers, so protecting digital identity becomes one of the most critical priorities for online security. In this context, it is recommended that;
Threat actors use advanced tools and tactics to target global consumers, so protecting digital identity becomes one of the most critical priorities for online security. In this context, it is recommended that;
- users and organizers who are members of e-commerce platforms ensure the reliability of the platforms where they use critical account information,
- do not rely on email, attachments, and links from unknown parties,
- not keep the input information available in the account in the browser memory,
- enable the 2FA/MFA features on any platform available, and
- use comprehensive security solutions.






