The second vulnerability allows an attacker who has already obtained this hash through other means (such as phishing) or via another exploit like EternalBlue, DoublePulsar, or EternalSynergy (which were all fixed by Microsoft in February) to gain access to any user’s mailbox on an Exchange server running Outlook Web Access (OWA).
CVE-2023-23397
Microsoft has patched a critical elevation of privilege vulnerability in Windows that was exploited by Russian hackers and ransomware actors.
The CVE-2023-23397 vulnerability allows attackers to execute code with elevated privileges on targeted systems. It was used by Strontium (aka APT28), Sednit, Sofacy and Fancy Bear in attacks against government, transportation, and energy sectors in Europe.
Microsoft did not reveal any further details about this flaw but said it was aware of limited, targeted attacks exploiting the bug before releasing its patches last week.
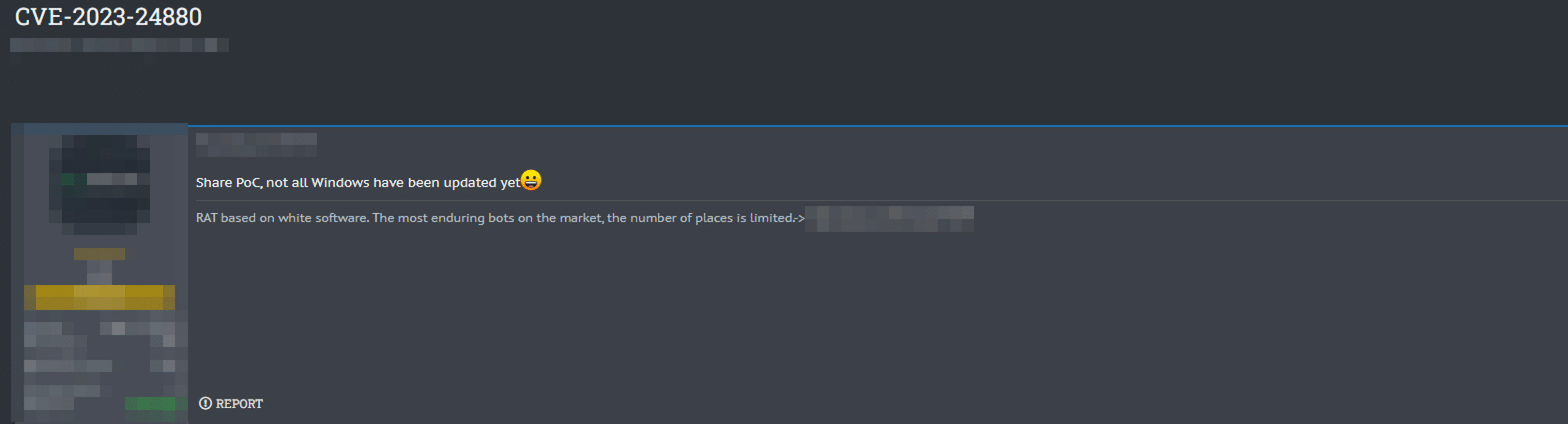
CVE-2023-24880
Microsoft has released a patch for a zero-day vulnerability that was exploited by the Magniber ransomware operation. CVE-2023-24880 is a SmartScreen security feature bypass, and it was used in the Magniber attacks to trick users into downloading malicious MSI files. The vulnerability affected all versions of Windows 10, 8, 7, and Vista operating systems from January 2023 to the present day.
Microsoft said that over 100 000 downloads of malicious MSI files had been detected since January 2023. The company also noted that there’s no evidence these exploits were used in any other attack campaigns apart from Magniber’s operations so far (aside from some reports about an unnamed actor abusing this same vulnerability).
The products and versions affected by the said vulnerabilities;
- Microsoft ICMP (MS18-11)
- Microsoft Excel (MS18-10)
- Microsoft IIS (MS18-09)
- Windows Cryptographic Services (MS18-08)
Exploitation Details
Microsoft has released a patch to fix the vulnerabilities. The company says that it has not seen any attacks in the wild, but security researchers have been able to exploit these flaws in lab environments.
The attack scenario involves an attacker sending a phishing email to users which contains a malicious attachment or link. When the victim clicks on that attachment or link, it downloads malicious code from an attacker-controlled server and executes it locally on their computer. This code can then use one of two methods to obtain NTLMv2 hashes: either through the Net-NTLMv2 hash of the Windows account or through an NTLM Relay attack against another service (such as RDP). Once obtained, these hashes can be used by attackers for authentication purposes when accessing other services such as SharePoint Server 2016 or Exchange Server 2016 running on Microsoft Windows Server 2012 R2 or earlier versions without having access credentials themselves
Prevention
- Keep Your Software Up-To-Date.
- Use Robust Authentication Methods.
- Use Secure Email Practices, Like S/MIME Encryption And Two-Factor Authentication (2FA).
Update
According to BRANDEFENSE Analysts’ investigation, threat actors posted about CVE-2023-24880 on a dark web forum. In the forum post, threat actors said that not all Windows systems had been updated yet, so they could continue to share the PoC.