As part of the October security updates, Microsoft has released updates for 85 security vulnerabilities, including 0-day vulnerabilities known to be actively exploited by threat actors. The criticality ratings of the vulnerabilities are 15 critical, 69 high, and one medium. In addition, it is stated that the published updates do not cover the “ProxyNotShell” vulnerabilities (CVE-2022-41040, CVE-2022-41082) recently detected in Microsoft Exchange Server.
Some of the critical vulnerabilities fixed by the updates are as follows;
- The vulnerability, tracked as CVE-2022-41033, is caused by a buffer overflow affecting the Windows COM+ Event System Service. The vulnerability, which affects all versions of Windows starting with Windows 7 and Windows Server 2008, allows a local user to execute code with SYSTEM privileges on a vulnerable system.
- The security vulnerability, tracked as CVE-2022-37979, is caused by a Race Condition bug in Windows Hyper-V. A local user can exploit the vulnerability to gain unauthorized access to sensitive information and elevate their privileges in the system.
- The security vulnerability, tracked as CVE-2022-37976, is caused by improper enforcement of security restrictions in Active Directory Certificate Services.
- The vulnerability, tracked as CVE-2022-37978, exists because the security features in Active Directory Certificate Services are bypassed. As a result, a remote user can exploit the vulnerability to perform man-in-the-middle (MitM) attacks and gain access to network communications.
- The vulnerability, tracked as CVE-2022-41043, exists due to excessive data output by Microsoft Office applications. As a result, a local user can gain unauthorized access to sensitive information in the system by exploiting the vulnerability.
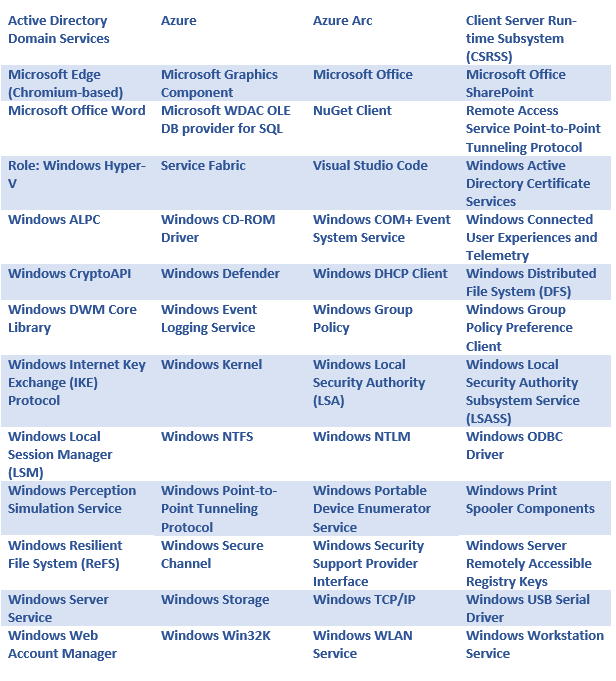
Updates that fix vulnerabilities affect the following Microsoft products and versions;