The attack vector begins with MuddyWater threat actors gaining initial access to systems by exploiting security vulnerabilities in SysAid servers. Based on observations from past campaigns by these threat actors and vulnerabilities found in target environments, the Microsoft security team has observed that the exploits are related to Log4j 2. In other attack campaigns observed in 2022, MuddyWater threat actors took advantage of Log4Shell vulnerabilities detected on VMware servers to gain initial access to systems. However, this campaign targeted SysAid servers, which are attractive to threat actors due to their widespread use in the targeted country and provide IT management tools for users.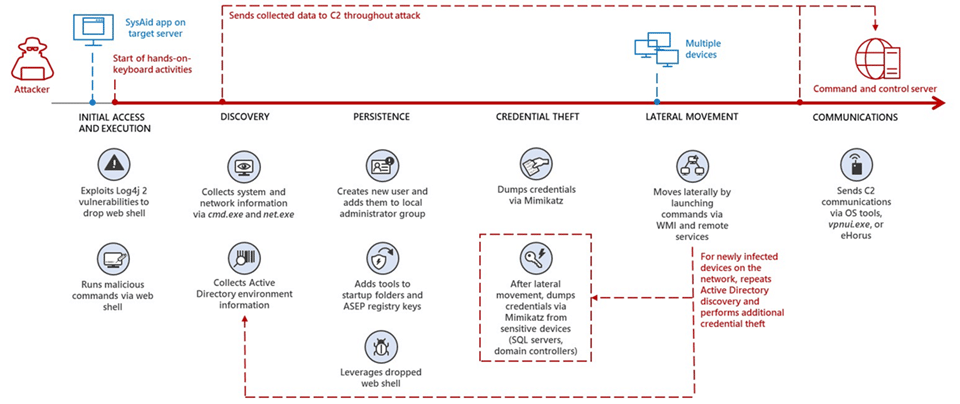
Since it was announced, the Log4Shell vulnerability has been used in critical attacks targeting institutions/organizations. In this context, it is recommended to consider the following security practices to avoid the target of critical attacks that can be carried out using the said vulnerability.
- It should be ensured that the software, applications, and programs used are used in the current versions where the vulnerability has been fixed.
- Comprehensive security solutions must be deployed.
- Critical systems or data should be backed up regularly.
- IOC findings related to the attack should be blocked from the security solutions in use.






