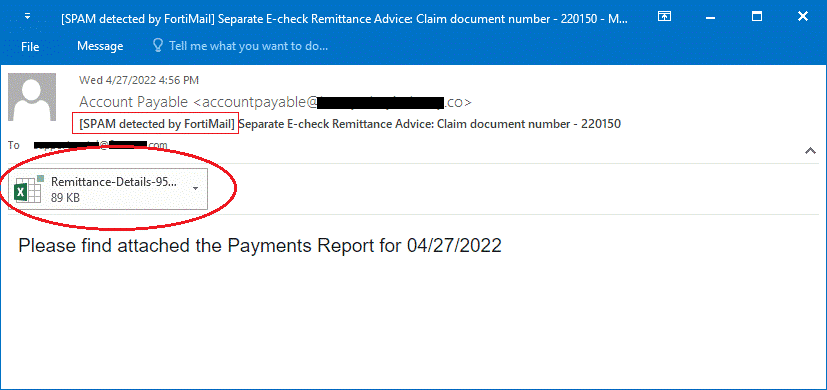
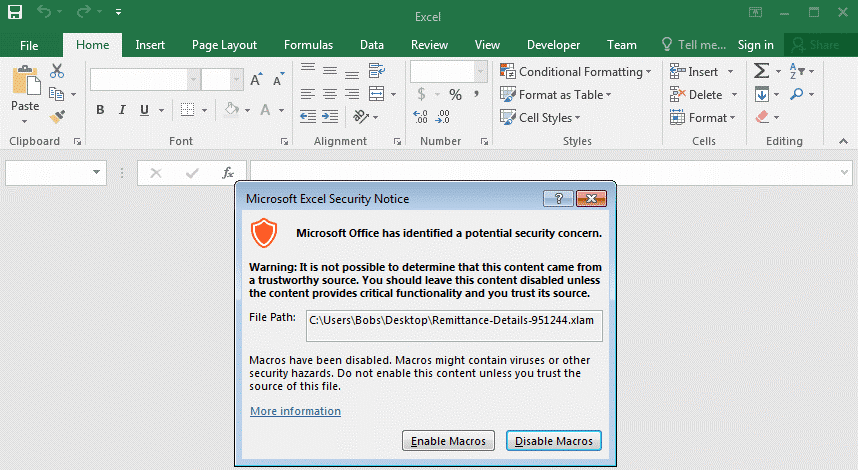
The chain of attacks begins with sending spear-phishing emails containing a malicious Excel document to the targets, which appears to be a payment report notification from a trusted source. Emails try to persuade recipients to open the attached Excel document for report detail. When the Excel file called “Remittance-Details-951244.xlam” is opened, and the macro is activated, a VBA (Visual Basic Application) script called “Auto_Open()” is executed, which is responsible for downloading the malware to be used in the campaign.
As a result of a series of steps performed through Powershell and the stated VBA scripts, malicious software called AveMariaRAT, BitRAT, and PandoraHVNC, which is responsible for capturing users’ sensitive information, including passwords and bank information, is downloaded to the target system. BitRAT can take full control of infected Windows systems, monitor webcam activity, listen to audio over the microphone, allow threat actors to perform undetected transactions on compromised cryptocurrency wallets, and download additional malicious files, which is why it was considered particularly dangerous.