We’ve gathered dark web insights, cyber security news, vulnerabilities, and CVEs, ransomware for you. Enjoy!
A Short-Look at The Dark Web
Here are the insights & security news from the dark web. Learn and protect yourself before threats reach you. If you want to get more insight, follow us on Twitter and Subscribe to our Ransomware Newsletter!
No need to cut credit cards; just monitor for suspicious activities! We recently discovered a threat actor claiming to have ~1M sensitive data records from @WellsFargo. Stay alert folks! And report any incidents to your bank! 🔐💳 #DataBreach #Financial #Cybersecurity pic.twitter.com/llb3bKnH1U
— BRANDEFENSE | Digital Risk Protection Service (@Brandefense) April 12, 2023
- In a Russian dark web forum, threat actors are targeting the China-based EPC company, Sinoma, which provides R&D, and engineering services. The hackers are demanding $10,000 for the RAT they used in the attack.
- A new MacOS secure-Websocket HVNC malicious tool was discovered on the dark web, using port 443 for authentication, which is concerning, ’cause this port is typically open by default!
Important Security News
What happened in cyberspace in the last two weeks? Here is a quick shot of security news from the world.
Attacks Using Realtek and Cacti Vulnerabilities Increase
Security professionals must be aware of the recent surge in attacks targeting vulnerabilities in Cacti and Realtek devices on Windows and Linux servers. These vulnerabilities are being exploited by threat actors deploying ShellBot and Moobot botnet malware to gain control of vulnerable systems.
Moobot exploits an arbitrary command injection vulnerability in Realtek Jungle SDK (CVE-2022-46169) and a command injection vulnerability in Cacti (CVE-2021-35394). It communicates with a command and control (C2) server using heartbeat messages and scans for other known bots, killing their processes to launch distributed denial of service (DDoS) attacks.
On the other hand, ShellBot primarily targets the Cacti flaw to deploy new malware variants.
The second variant is particularly dangerous due to its extensive set of commands and multiple types of flooding attacks.
It’s worth noting that several other attackers have also leveraged these same vulnerabilities to deploy other botnet malware, such as Fodcha, Gafgyt, Mirai, Mozi, and RedGoBot.
While software updates have been released to address these vulnerabilities, many organizations still use vulnerable devices, exposing them to these attacks.
Therefore, security professionals should advise organizations to;
- Update their Cacti and Realtek devices to the patched versions as soon as possible
- Continue to monitor their systems for any signs of IoCs, and
- Implement best practices for securing their networks, such as applying patches promptly, using strong passwords, and limiting access to sensitive data.
New Windows CLFS 0-Day Vulnerability Used in Ransomware Attacks
The critical Windows CLFS 0-day vulnerability that Microsoft addressed in the April 2023 security patches was found to be used in Ransomware attacks by threat actors.
The vulnerability, code CVE-2023-28252, affects the CLFS (Common Log File System) driver and allows local threat actors to elevate their privileges to SYSTEM privileges. The US CISA has identified findings regarding the use of the vulnerability in attacks where the distribution of Nokoyawa Ransomware software is provided.
All federal agencies are expected to fix the vulnerability upon detection by May 2, 2023. At the same time, Kaspersky Lab security researchers have identified evidence of active exploitation of the vulnerability in Nokoyawa attacks. Attacks using the vulnerability target small and medium-sized businesses in the Middle East, North America, and Asia regions.
In order to prevent active exploitation of the vulnerability, no detailed explanation will be made yet.
In this context, it is recommended to take the following precautions into consideration to avoid being the target of ransomware or other attack campaigns that can be carried out using the vulnerability.
- Security updates that fix vulnerabilities should be applied to vulnerable systems immediately,
- E-mails, attachments, and links from unknown parties should not be trusted, opened,
- Comprehensive security solutions should be used,
- Care should be taken against social engineering/phishing attacks that may be carried out during the distribution phase of the malware.
A New Stealer Targeting Cryptocurrency Users Through Phishing Sites Detected: “Creal”
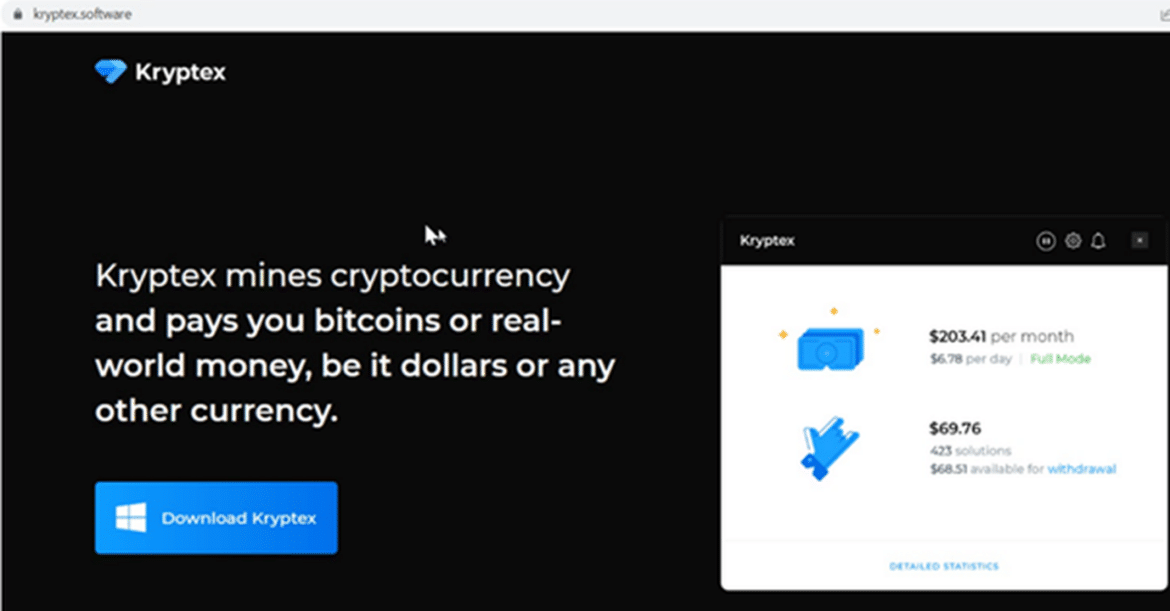
The phishing site is impersonating a legitimate Cryptocurrency mining platform. When users click the “Download Kryptex” button to download the crypto money application to their computers, they are directed to the Dropbox page, where a ZIP file containing the Creal Stelar malware is hosted.
THE STEALER SOFTWARE IS CODED IN PYTHON, AND THE SOURCE CODE IS AVAILABLE IN A PUBLIC GITHUB REPOSITORY, ALLOWING OTHER THREAT ACTORS TO MODIFY THE CODE TO SUIT THEIR NEEDS. Therefore, it is a foreseeable scenario for various stealer malware to emerge from the source code of Creal Stealer and pose a significant threat to users. In addition, about 50 examples of the use of the malware in question have been observed in the wild. This shows that threat actors are actively using Open Source code.
Creal provides permanence by copying itself on the infected system. In the data collection process defines global variables by including keywords such as cookieWords, passwWords, CookieCount, P4sswCount, WalletsZip, GamingZip, and OtherZip.
The module that handles Stelar malware’s data collection targets Chromium-based browsers, chat and gaming apps, cold crypto wallets, and browser extensions.
The phishing site looks like the image below.
Security News Headings
- Microsoft April 2023 Patch Tuesday Fixes 1 Zero-Day, 97 Flaws
- SAP Releases Security Updates for Two Critical-Severity Flaws
- Multiple Vulnerabilities in Fortinet Products Could Allow for Arbitrary Code Execution
-
North Korean Hackers Uncovered as Mastermind in 3CX Supply Chain Attack
- HP LaserJet printers have a critical security bug – and there’s nothing you can do for now






