Recent studies have found that over 8,000 unauthenticated VNC installations are accessible over the Internet. The number of VNC servers left open to the Internet is mostly concentrated in China, Sweden, and the United States.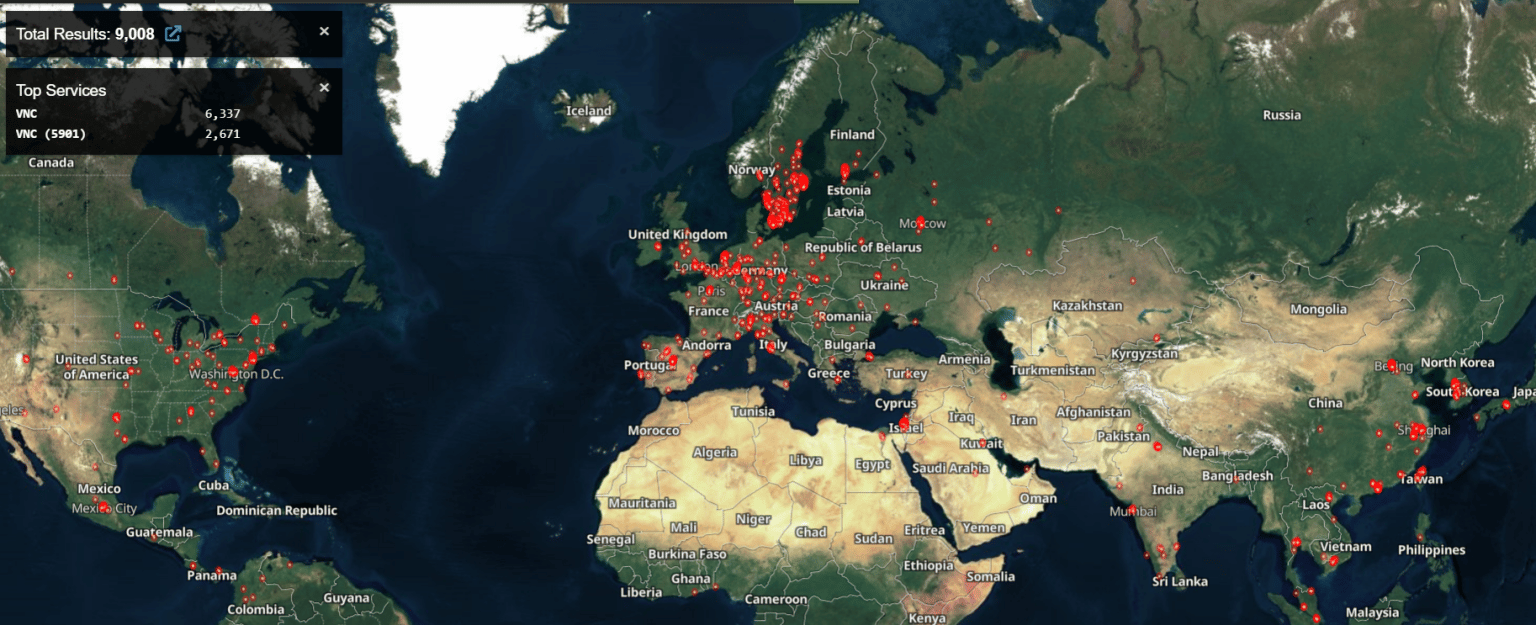
Most of these attacks are carried out in the Netherlands, Russia, and Ukraine. In addition, some VNC servers vulnerable to attacks are owned by organizations serving critical infrastructure industries, including water treatment plants, manufacturers, and research facilities. Therefore, this situation puts critical infrastructure systems such as HMI, SCADA/ICS, and workstations connected via VNC and accessible over the Internet at risk.
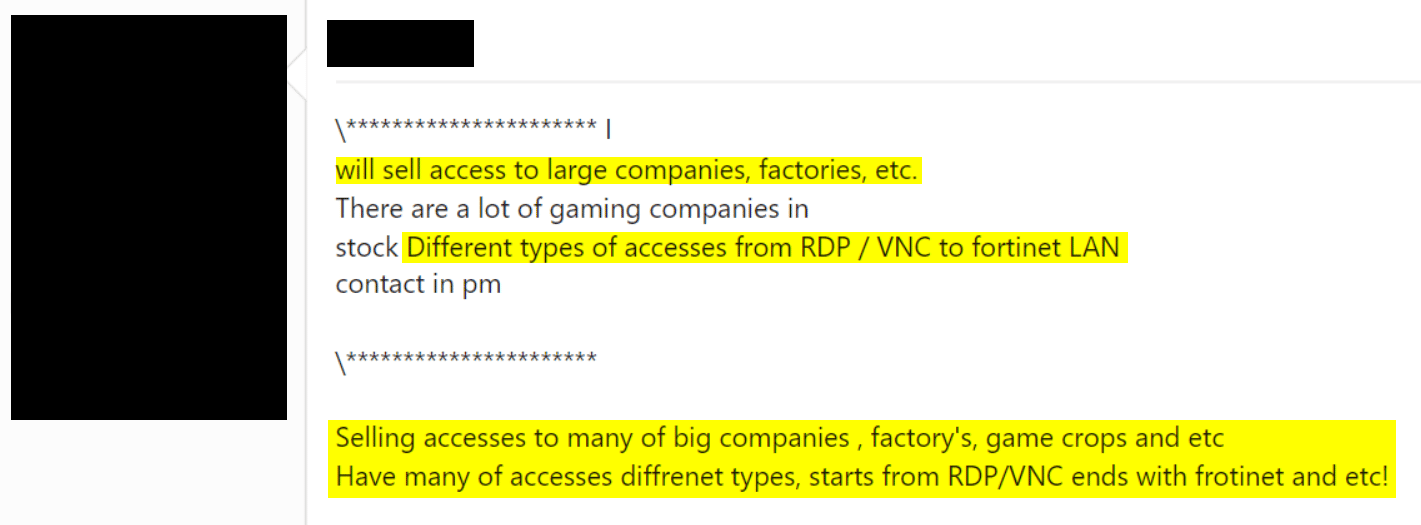
Threat actors targeting the security of such systems can interfere with predefined configurations, take industrial control systems (ICS) out of service, disrupt the supply chain and processes in the affected industries, or gain access to sensitive data that can be used to compromise ICS systems. In addition, it has been observed that threat actors use these VNC accesses in their trading activities on platforms on the Deep Web.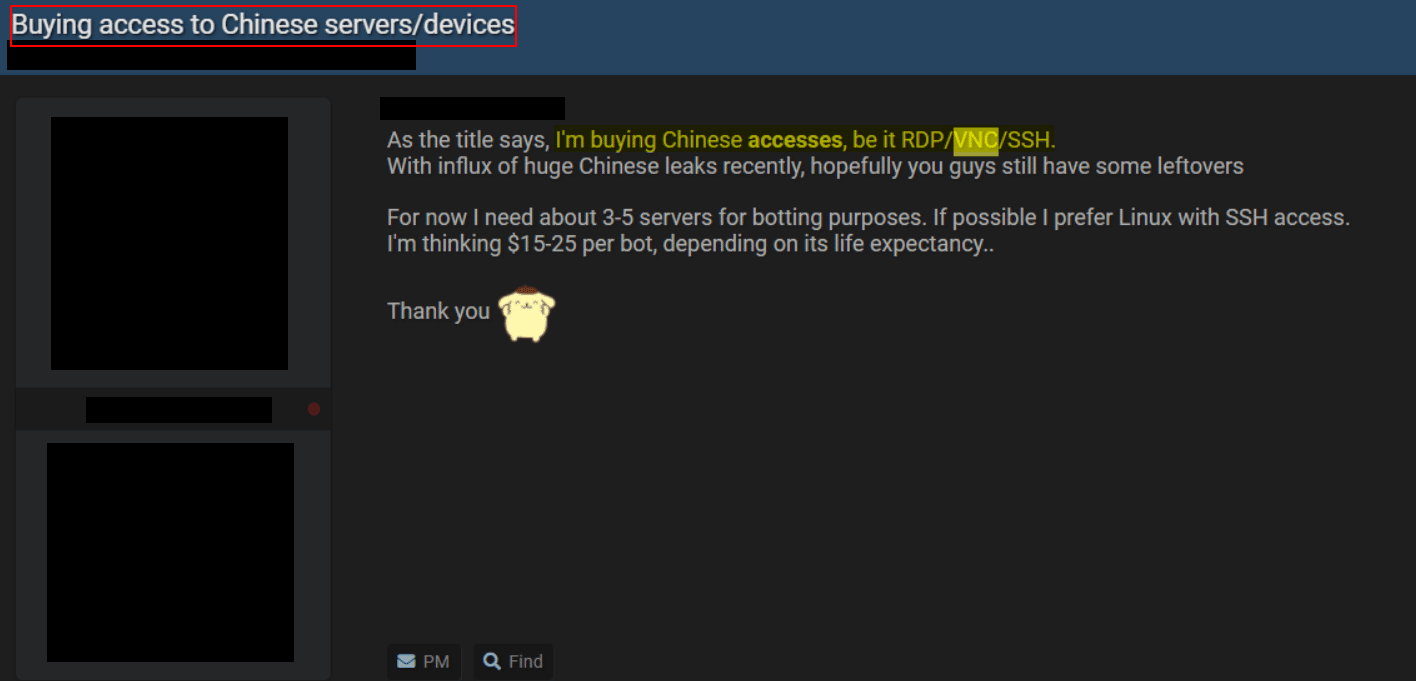
- Ensure that critical systems in the IT environment are behind firewalls,
- Internet exposure of VNCs should be minimized.
- SCADA/ICS systems should be used in the latest versions published by the official vendor,
- Strong password policies should be enforced within the organization,
- Access controls within the organization should be configured correctly,
- Network traffic should be constantly monitored for the security of the institution/organization inventory,
- All necessary security measures for VNC must be enabled,
- Cyber security awareness should be raised for those working in the SCADA/ICS environment.






