A Critical Security Vulnerability Detected in Apple M1 Processor: “PACMAN”
A new security vulnerability targeting Apple’s popular M1 processor has been identified by researchers at MIT’s Computer Science and Artificial Intelligence Laboratory (CSAIL). Called PACMAN, the attack is intended to circumvent the Pointer Authentication (PAC) mechanism in M1 and other ARM-based processors. PAC is a security feature that helps protect against threat actors that have gained memory access to the CPU. Pointers store memory addresses, and the PAC checks for unexpected pointer changes caused by an attack.
PACMAN vulnerability is in a hardware mechanism, so it is estimated that it cannot be remedied with a software update. What makes PACMAN vulnerability dangerous is that it directly affects the core. The core is the most privileged part of the operating system. Endangering the core means a threat actor can do everything the user can in a vulnerable system.
PACMAN can be triggered if there is any software vulnerability in the system, but there is no risk of endangering systems on their own. For example, memory corruption is one of the vulnerabilities that can cause PACMAN to be triggered. In this context, Apple users must keep their operating systems and software up-to-date.
BlackCat Ransomware Is Targeted Vulnerable Microsoft Exchange Servers
Cyber threat actors have been found to launch attack campaigns by exploiting vulnerable Microsoft Exchange servers to spread BlackCat ransomware. After gaining access to vulnerable Microsoft Exchange servers, BlackCat ransomware was found to be distributed to target systems with the PsExec tool. In this way, threat actors infiltrate target systems, obtain critical identity data of users and carry out “double extortion” activities. Double Extortion is the name given to cases where threat actors threaten to leak data or publish some of it on the Internet, even if the ransom is paid in ransomware-infected organizations.
BlackCat ransomware was first observed in 2021 and developed with the Rust programming language. RaaS (Ransomware-as-a-Service) operators aim to ensure persistence by gaining unauthorized access to multiple systems on the target network before ransomware activities. How BlackCat ransomware infects victims differ according to the techniques and tactics of RaaS operators. For example, It is known that the FIN12 threat group, which organizes ransomware campaigns such as Ryuk, Hive, and Conti, has been one of the BlackCat operators since March 2022.
BlackCat ransomware is also distributed by the DEV-0504 threat group, which uses the Stealbit malware of the LockBit threat group. The DEV-0504 threat group is known to use BlackMatter, Conti, LockBit 2.0, Revil, and Ryuk ransomware.
The Microsoft Exchange Server vulnerabilities used in the said attack campaign are as follows;
- CVE-2021-26855
- CVE-2021-26858
- CVE-2021-26857
- CVE-2021-27065
Using ransomware with different versions in attack campaigns significantly increases the risk of institutions and organizations encountering BlackCat-like malware. In this context, in order not to be the target of similar ransomware attacks;
- Beware of untrusted e-mail content,
- Not opening additional files/links of suspicious sender mail addresses,
- Using reliable Anti-Malware solutions
- Using licensed and current technologies,
- It is recommended to block shared IoC findings related to the malware campaign by security solutions.
Misconfigured Elasticsearch Servers Targeted by Threat Actors
Secureworks security researchers have identified a new attack campaign targeting misconfigured Elasticsearch databases. Threat actors demand ransom payments from targets by altering the database content on vulnerable Elasticsearh servers with their ransom notes.
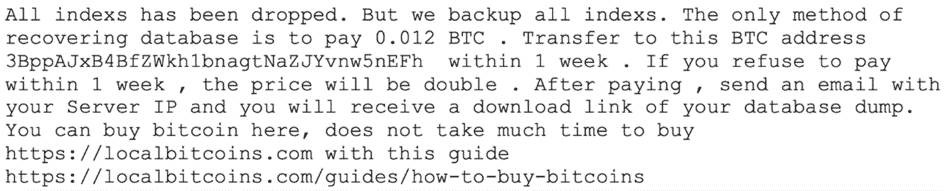
However, at this stage, promises made by threat actors should not be respected because it is impractical for threat actors to store large amounts of content. Most likely, the contents of the hacked databases are deleted, but ransom notes are left promising to restore the contents to the system. Therefore, database administrators need to take regular backups.
These and similar security breaches can lead to loss of reputation, data leakage, and possible service interruptions that may cost much more than the ransom amount of the affected institutions/organizations and organizations. In this context, it is recommended to use the current versions of the systems and programs, take regular backups of critical systems/files, perform attack surface analysis tests at regular intervals, and use comprehensive security solutions.






