0-Day Vulnerabilities in PrestaShop Makes E-Commerce Sites Vulnerable
Multiple critical 0-day security vulnerabilities which threat actors use to inject malicious code into e-commerce sites have been detected in the PrestaShop E-Commerce platform. The combined use of security vulnerabilities causes threat actors to remote code execution (RCE) on affected web servers and capture their customers’ payment information.
The attack requires the platform to be vulnerable to SQL injection exploits. In the analysis performed, the attack starts with the threat actors sending malicious GET and POST requests to the endpoint open to SQL injection. Then, threat actors gain full control via the PHP file created at the platform’s root directory and inject a fake payment form on the prepayment page. In this way, the credit card information entered in the fake form by the store customers is captured. Additionally, PrestaShop officials stated that threat actors might be using MySQL Smarty cache storage features as part of the attack vector. Therefore, it is recommended to disable this feature as a mitigation measure.
SQL injection vulnerabilities affect PrestaShop versions 1.6.0.10 or higher. 1.7.8.2 and higher versions are not affected by the security vulnerability in default configurations. PrestaShop 1.7.8.7 was released to harden MySQL Smarty cache storage against code injection attacks. Web application administrators using vulnerable PrestaShop versions must immediately apply the updates that fix the vulnerabilities.
“Sality”: The Malware Distributed to Industrial Systems via Password Recovery Tools
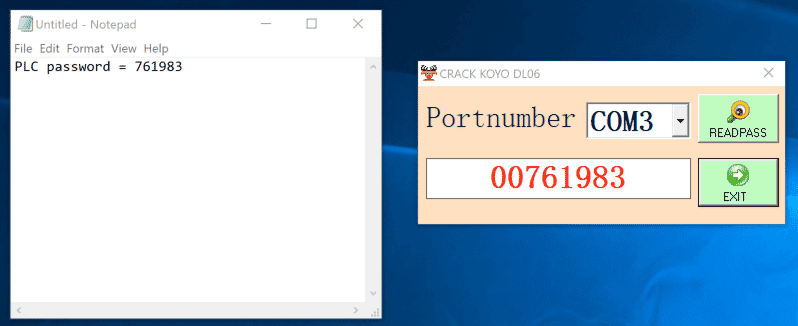
Dragos security researchers identified a malware distribution campaign to industrial control systems (ICS) through password recovery tools developed for programmable logic controllers (PLC). Password recovery tools that are advertised on various social media platforms promise to recover passwords of systems used in industrial control environments such as Automation Direct, Omron, Siemens, Fuji Electric, Mitsubishi, LG, Vigor, Pro-Face, Allen Bradley, Weintek, PLC, ABB, Panasonic, and HMI.
These password recovery tools use known security vulnerabilities in devices to reveal system passwords. However, these tools inject a trojan software called Sality into vulnerable systems in the background. Sality has advanced features such as terminating trojan-injected system processes, connecting to remote servers, downloading additional payloads, or leaking data from the host.
Also, thanks to the Sality trojan’s ability to communicate over a peer-to-peer (P2P) network, infected systems can become part of a botnet network controlled by threat actors. The Sality sample analyzed by Dragos researchers has been observed to be infected to carry out activities focused on cryptocurrency hijacking from vulnerable systems.
In this context, it is important to apply the following security measures in order not to be the target of similar malware campaigns targeting critical/sensitive systems;
- It should be ensured that the systems, software, and hardware used are always used in the current versions where the vulnerabilities are fixed,
- Comprehensive and reliable Anti-Virus / Anti-Malware and Firewall solutions should be used,
- User privileges on systems should be limited,
- E-mails, attachments, and links from unknown parties should not be respected,
- Application, program/software downloads must be made through legitimate and reliable sources,
- Avoid downloading cracked software,
- Institution/organization personnel should be made aware of potential phishing/social engineering attacks,
- Passwords used in systems should be created using unique and strong policies,
- Detected IOC findings regarding the malware should be blocked from the security solutions in use.
Multiple Critical Vulnerabilities Detected in Drupal CMS
Multiple security vulnerabilities, including critical ones, detected in the Drupal open source content management system (CMS) have been fixed with updates released by Drupal officials.
The “critical” security vulnerability as tracked CVE-2022-25277 affects Drupal CMS 9.3 and 9.4. The vulnerability found in Drupal Core can cause arbitrary PHP code execution on Apache web servers by loading specially crafted files. However, Drupal officials stated that this vulnerability only affects Apache web servers in specific configurations. Three other security vulnerabilities, considered less critical, allow performed cross-site scripting (XSS) attacks, disclosure of information, or bypassing access restrictions.
These security vulnerabilities were fixed with Drupal CMS versions 9.4.3, 9.3.19, and 7.91. In order not to be the target of attacks using vulnerabilities, Drupal CMS users are advised to consider the recommendations published by CISA and immediately apply the published updates to the vulnerable versions.






