Critical Zero-Day Alarm on Trend Micro Apex One
Security solutions provider Trend Micro has released security updates regarding a zero-day vulnerability identified in Apex One and Apex One SaaS endpoint security solutions that is known to be actively exploited by threat actors.
The security vulnerability with code CVE-2022-40139 is caused by incorrect input validation in the application’s Rollback function. An authenticated remote user with access to the Admin console could exploit the security vulnerability to force Agents to download unverified malicious Rollback components.
In addition to the CVE-2022-40139 vulnerability, Trend Micro has also fixed several medium-risk security issues (CVE-2022-40141, CVE-2022-40144). The first vulnerability (CVE-2022-40141) allows threat actors to access sensitive data. The second (CVE-2022-40144) allows remote threat actors to bypass authentication checks and gain unauthorized access to the application.
Users using Trend Micro Apex One and Apex One SaaS 2019 versions are recommended to immediately apply the published updates in order not to be the target of attacks that can be carried out using these vulnerabilities.
RedLine Stealer Malware Was Distributed Through the Corporate Social Media Accounts
Avast security researchers have identified multiple business accounts on social media that distribute the Redline Stealer malware, which is responsible for capturing users’ login credentials from infected systems.
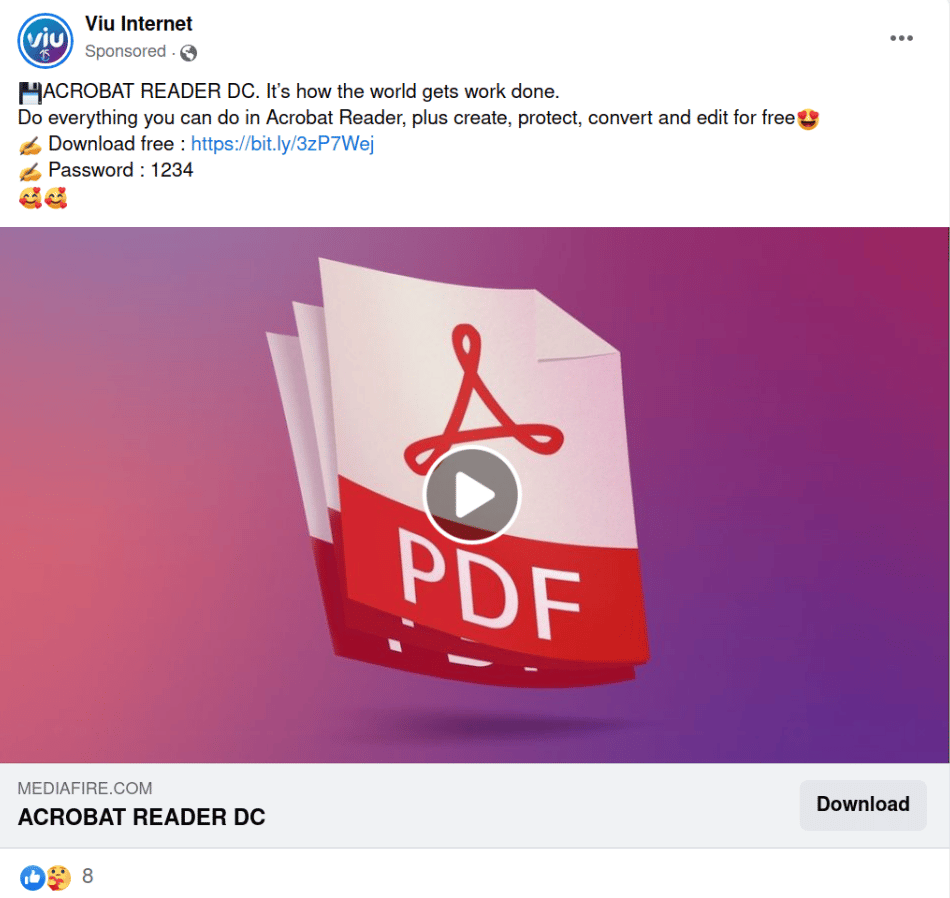
The malware distribution campaign was identified through a sponsored post on Facebook promoting free Adobe Acrobat Reader software. The post in question was shared via the Facebook business account of Viu Internet, an internet service provider in Brazil. The post contains a link redirecting destinations to the “Mediafire.com” platform instead of “Adobe.com.” By clicking the link in the post, the files on the storage and sharing platforms are requested to be downloaded to the systems. Readline Stealer injection requires visitors to download the file, extract the content from the archive, and run it.
Viu Internet warns users who visit their homepage that their Facebook account has been hacked. In addition to Viu Internet’s Facebook account, several hacked Facebook business accounts have been found to post the same malicious content.
In this context, it is recommended to consider the following security warnings to avoid being the target of malware campaigns that can be carried out with similar methods.
- Emails, attachments, and links from unknown parties should not be respected.
- Advertisements and links in social media content should not be opened.
- Downloads of files, programs, or applications should be done from trusted, legitimate sources.
- Comprehensive security solutions (Anti-Virus/Anti-Malware) should be used.
Mirai Variant MooBot Botnet Targets Vulnerable D-Link Devices
Security researchers at Palo Alto Networks Unit42 have detected that vulnerable D-Link devices are targeted in MooBot Botnet campaigns, which are known to be the Mirai Botnet variant.
In observed exploit attempts, threat actors exploit the following security vulnerabilities to propagate MooBot to network devices running Linux and with internet exposure;
- CVE-2015-2051: D-Link HNAP SOAPAction Header Command Execution Vulnerability (Version 2.0)
- CVE-2018-6530: D-Link SOAP Interface Remote Code Execution Vulnerability (Version 3.0)
- CVE-2022-26258: D-Link Remote Command Execution Vulnerability (Version 3.0)
- CVE-2022-28958: D-Link Remote Command Execution Vulnerability (Version 3.0)
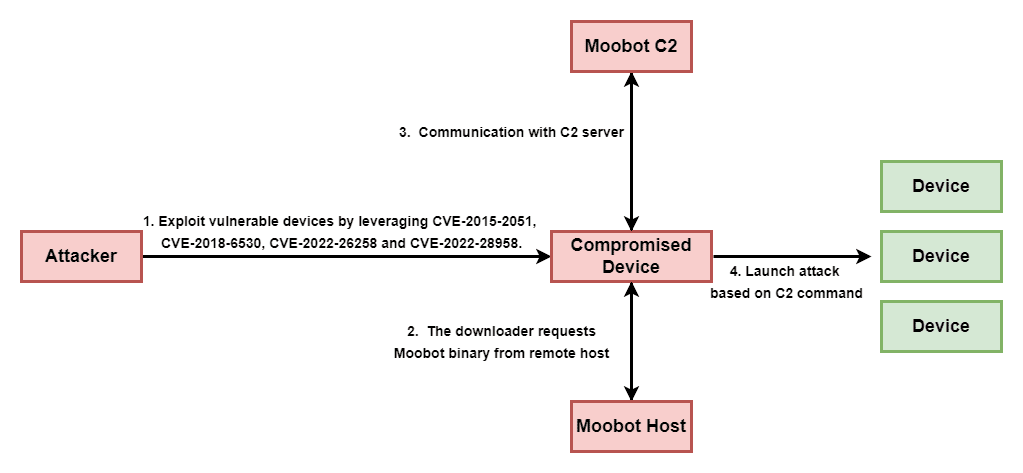
Threat actors exploit these vulnerabilities to breach the security of devices and then use these devices as bots in various attacks, such as distributed denial of service (DDoS) targeting different systems.
D-Link has released security updates regarding the specified security vulnerabilities, but still, many users are known to be running un-updated older versions or vulnerable devices. Therefore, in order not to be the target of similar malware attacks that may be carried out, users using vulnerable D-Link versions are recommended to apply updates that fix the vulnerabilities immediately. In addition, it is important to prevent the IOC findings related to the campaign in question from the security solutions in use.






