Critical Zero-Day Alarm on iOS and iPadOS
Apple has released updates to 20 security vulnerabilities affecting iOS and iPadOS operating systems, including a 0-day vulnerability known to be actively exploited by threat actors.
The 0-day vulnerability, tracked as CVE-2022-42827, exists due to a boundary error affecting the “Kernel“ component of the operating system. Threat actors can execute with root privileges on the vulnerable system by triggering an out-of-bounds write error through a specially crafted application.
Apart from the vulnerability mentioned above, Apple has also fixed two high-severity vulnerabilities with the released iOS 16.1 and iPadOS 16 updates. In order not to be the target of attacks that can be carried out using vulnerabilities, Apple users using vulnerable versions are recommended to apply the published updates immediately.
Iran Atomic Energy Agency Suffered from a Breach
The Atomic Energy Agency of Iran was exposed to a security breach that resulted in the threat actors gaining unauthorized access to their e-mail servers, compromising their data security.
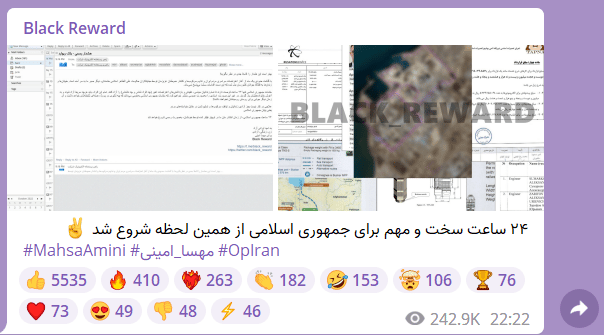
The security breach came to light when threat actors known as “Black Reward” claimed to have obtained sensitive data on their Telegram channel, including contract files, business plans, and information about other facilities. In addition to the sharing, the threat actors announced that the captured data would be shared publicly if the political prisoners arrested during the recent protests against the Iranian government on October 21 were not released within 24 hours.
The Iranian Atomic Energy Agency officials confirmed the security breach by targeting e-mail servers, but it was emphasized that the captured data was unimportant. Furthermore, it was stated that the intercepted e-mails contained technical and casual messages. In this context, it is recommended that institutions and organizations take into account the following security practices in order not to be the target of targeted attacks that can be carried out in a similar way to protest and attract attention.
- Internal inventories such as e-mail servers used within the institution/organization should be used in the most up-to-date versions where the vulnerabilities are fixed.
- Institution/organization personnel should not rely on spam e-mails, attachments, and links from unknown parties.
- Comprehensive security solutions should be deployed to the corporate/organizational network.
Magniber Ransomware Targets Windows Users with Fake Software Updates
HP Wolf Security researchers have detected that the operators of Magniber Ransomware are running a new malware distribution campaign targeting Windows home users with advanced features.
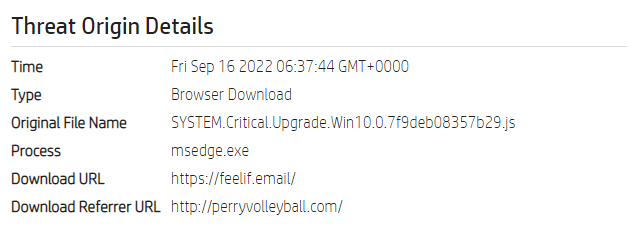
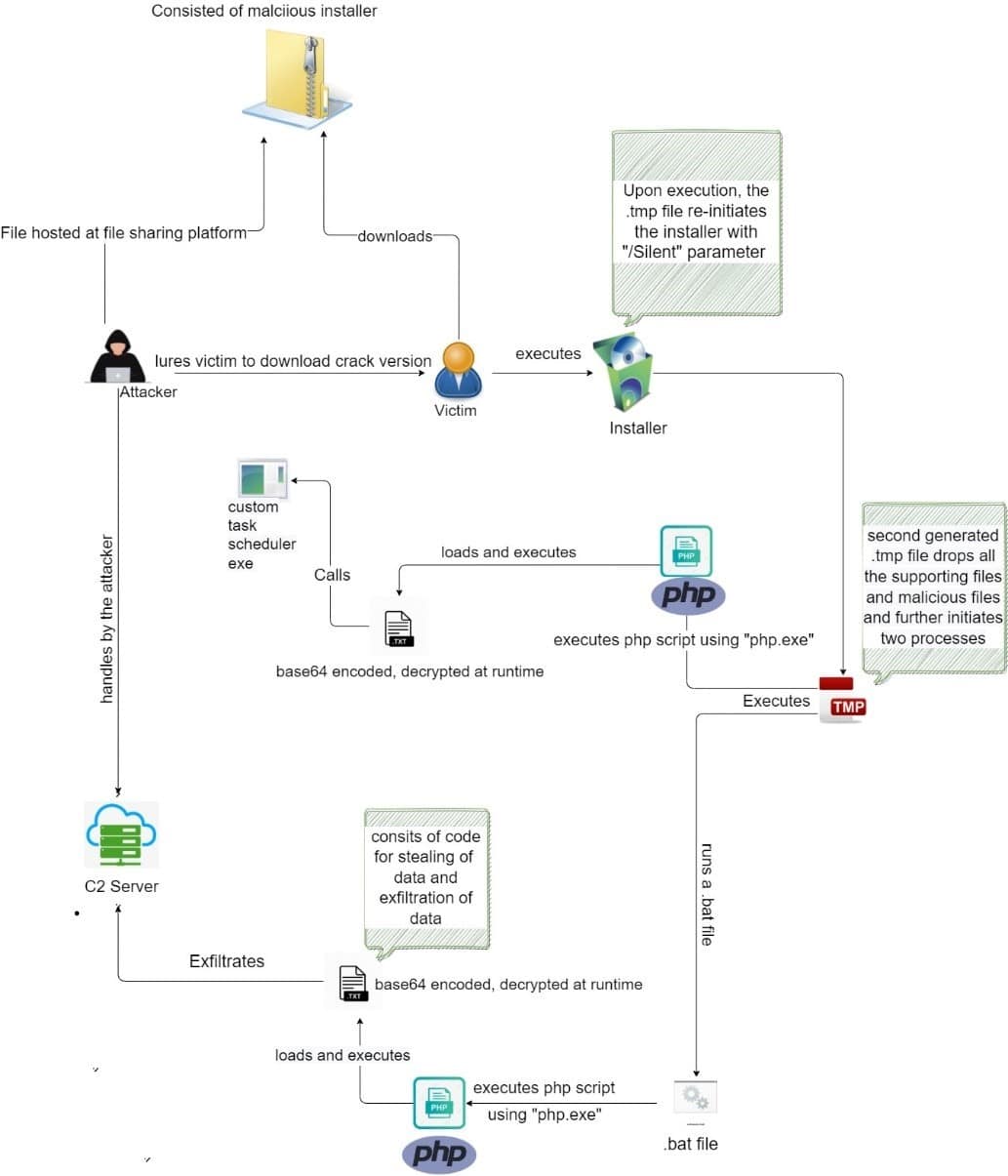
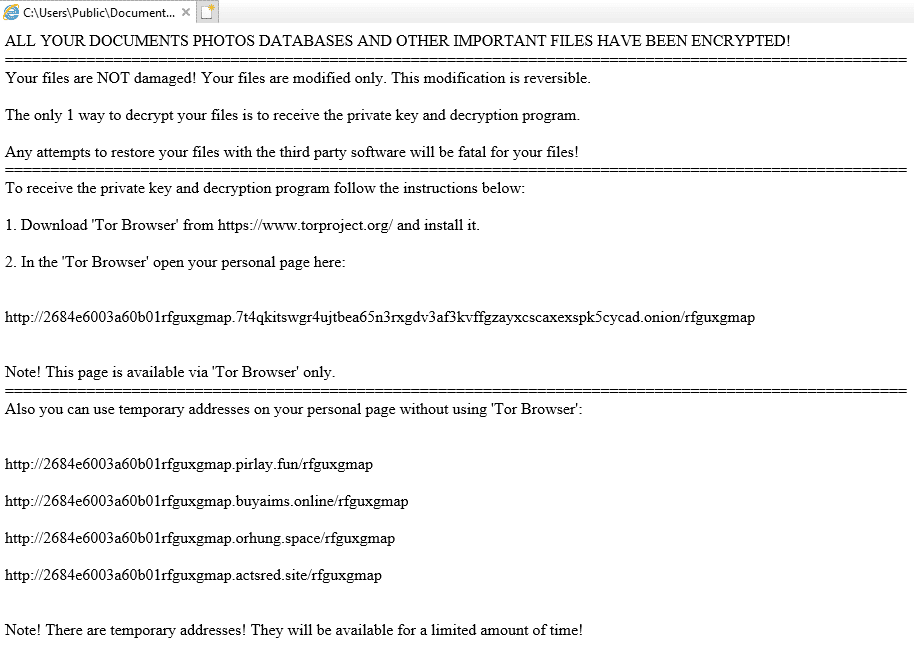
The threat actors behind the Magniber malware are known to demand a $2500 ransom payment from infected users. In this context, it is recommended to consider the following security steps in order not to be the target of this and similar ransomware campaigns.
- Administrator accounts used in line with the need should be created by considering the principle of least privilege,
- Software updates or programs should be obtained from reliable and official sources,
- The data stored in the systems should be backed up at regular intervals,
- Comprehensive Anti-Virus / Anti-Malware solutions should be used,
- IOC findings related to the campaign should be blocked from security solutions in use.






