WordPress reCAPTCHA Plugin has an XSS Vulnerability
A vulnerability has been identified in the WordPress reCAPTCHA plugin, which protects WordPress website forms from spam/robot logins, that could allow threat actors to perform XSS (Cross-Site Scripting) attacks on affected installations.
The security vulnerability with code CVE-2022-3831 affects the “unfiltered_html” component and is caused by insufficient cleaning of user-supplied data. Exploiting the vulnerability requires administrative privileges.
The vulnerability, assessed as medium critical, affects all versions of WordPress reCAPTCHA 1.6 and earlier. The plugin has been removed from the WordPress market since November 2, 2022, and no current version fixes the vulnerability. In this context, it is recommended that users using the plugin in WordPress installations immediately disable or remove it to avoid being affected by the vulnerability.
Medibank Confirms Security Breach Affecting 9.7 Million Customers’ Data
Australian-based insurance firm Medibank has confirmed that they were exposed to a security breach by BlogXX threat actors, resulting in unauthorized access to 9.7 Million customer data. BlogXX is a structure of the Revil Ransomware group that was shut down by law enforcement in 2021.
9.7 million customer data captured by threat actors in this Ransomware attack includes personal information such as name, surname, date of birth, full address, phone number, and email address. In addition, the captured data also includes the Medicare numbers of customers, passport numbers, and visa details of international student customers. After the data breach, the Medibank security team announced that they detected Ransomware on their systems on October 12, 2022, and the affected systems were isolated. It is known that BlogXX threat actors threatened Medibank with leaking the captured data if the ransom payment was not made, but Medibank refused to pay the ransom.
With more than 3.9 million customers and 4,000 employees, Medibank is among Australia’s largest private health insurance providers. Every day, many institutions and organizations, regardless of large or small scale, are targeted by Ransomware attacks. In this context, it is recommended to consider the following suggestions in order not to be the target of similar attacks;
- Emails, Attachments, Files/Links From Suspicious/Unknown Parties Should Not Be Relied on.
- File, Software, and Program Downloads Must Be Performed From Legitimate And Official Sources.
- Current and Comprehensive Security Solutions should be used.
- System And Applications Should Be Keep At The Latest Version.
Dynamics 365 Customer Voice Service Detected To Be Manipulated In Phishing Attacks
Avanan security researchers have determined that the Dynamics 365 Customer Voice service, a Microsoft product that institutions/organizations use to get customer feedback, is manipulated in phishing attacks by threat actors. Threat actors behind this phishing campaign are planning to seize the Microsoft account information of customers by sending phishing links that appear legitimate to customers via Dynamics 365 Customer Voice.
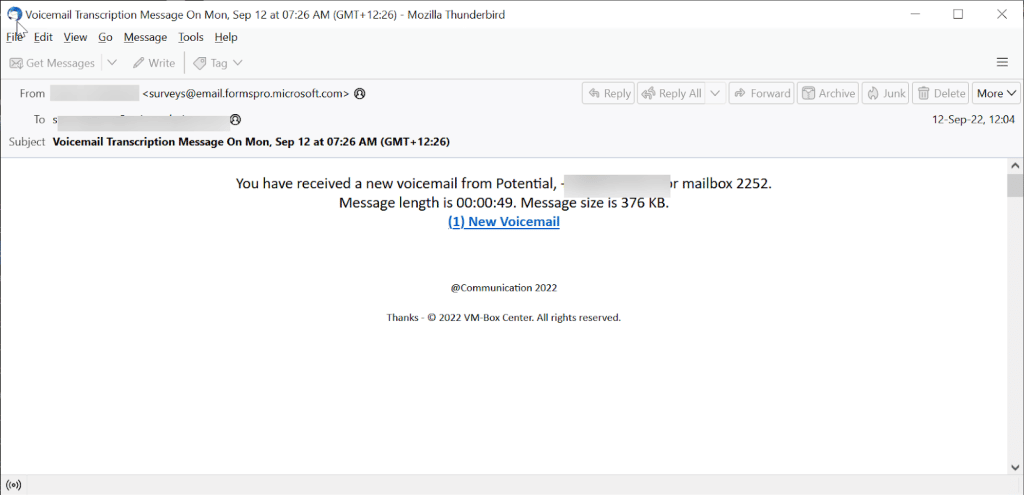
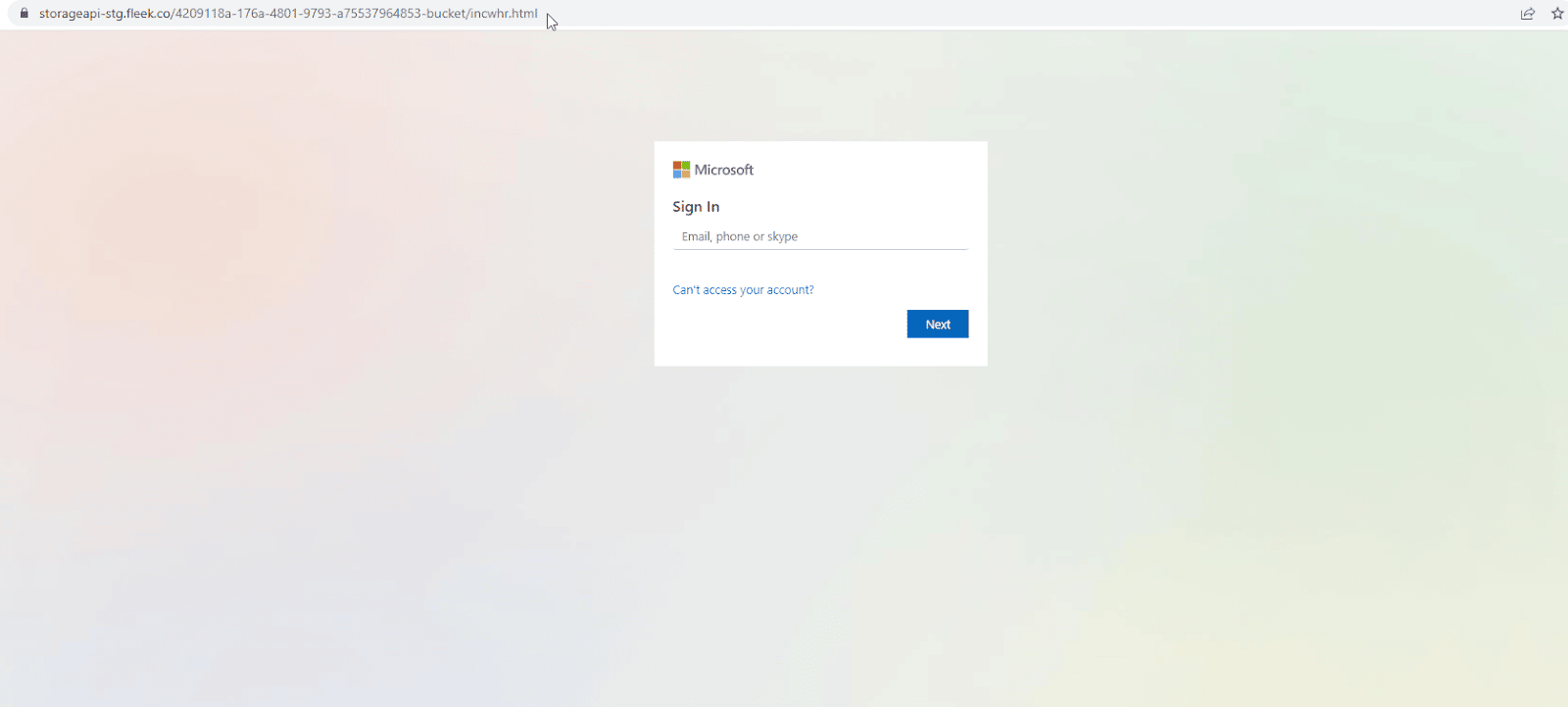
The campaign is an attack that requires careful detection by targets, as the phishing link is not visible until the last step. Additionally, destinations are redirected from the e-mail body to a legitimate page first, so hovering over the URL in the e-mail body does not provide protection. In this context, in order not to be the target of phishing attacks that can be carried out using similar methods, attention is paid to the following security recommendations;
- Users should check all URL addresses, including links in the e-mail body,
- E-mails, attachments, and links from unknown parties should not be trusted,
- Login credentials thought to have been compromised should be promptly replaced by enforcing strong password policies.






