Critical UEFI Firmware Vulnerabilities Detected in Specific Lenovo Notebook Models
Lenovo has released updates regarding vulnerabilities detected in the UEFI Firmware component affecting Yoga, IdeaPad, and ThinkBook devices. UEFI refers to software that acts as an interface between the operating system and the firmware embedded in the device’s hardware and is responsible for starting the operating system when a device is powered on. Therefore, UEFI offers a highly attractive attack surface for threat actors who want to release hard-to-detect and remove malware.
Here are the details of the vulnerabilities that could be used by threat actors to disable Secure Boot, a security mechanism designed to prevent malicious programs from loading during the boot process;
- The vulnerability, tracked as CVE-2022-3430, affects the WMI Setup driver on certain Lenovo Notebook PC devices and allows a threat actor with elevated privileges to modify Secure Boot settings by modifying an NVRAM variable.
- The vulnerability, tracked as CVE-2022-3431, affects a driver used in certain Lenovo Notebook PC devices that is not accidentally disabled during the manufacturing process and could allow a threat actor with elevated privileges to change the Secure Boot setting by changing an NVRAM variable.
- The vulnerability, tracked as CVE-2022-3432, affects a driver used during the manufacturing process on the IdeaPad Y700-14ISK that was not accidentally disabled and could allow a threat actor with elevated privileges to alter the Secure Boot setting by changing an NVRAM variable.
After the vulnerabilities were detected by the Eset security researcher, Lenovo announced that they took action to fix the vulnerabilities. However, Lenovo has stated that they do not plan to release fixes for CVE-2022-3432 as the affected model has reached the end of life (EoL). In this context, it is recommended that users of other affected devices update their firmware to the latest version in order not to be the target of attacks that can be carried out using vulnerabilities.
Threat Group Named Worok Performs Espionage Activities With Backdoors Hidden Inside Image Files
A recently discovered cyber spy group called Worok has been found to hide malware in image files. PNG files’ purpose is to hide a malicious payload used to facilitate information theft.
Avast discovered that Worok used a C++-based Payload called CLRLoad to pave the way for a PowerShell script embedded in PNG images, using a cloaking technique known as steganography. The findings show that the threat actor applied DLL Injection after gaining initial access to execute the CLRLoad malware.
Used in the attack chain, Malware called DropboxControl uses a Dropbox account for command and control (C&C) and captures data by allowing the threat actor to download/upload/run files to specific folders. Private companies and government agencies operating in locations such as Cambodia, Vietnam, and Mexico are among the countries affected by DropboxControl.
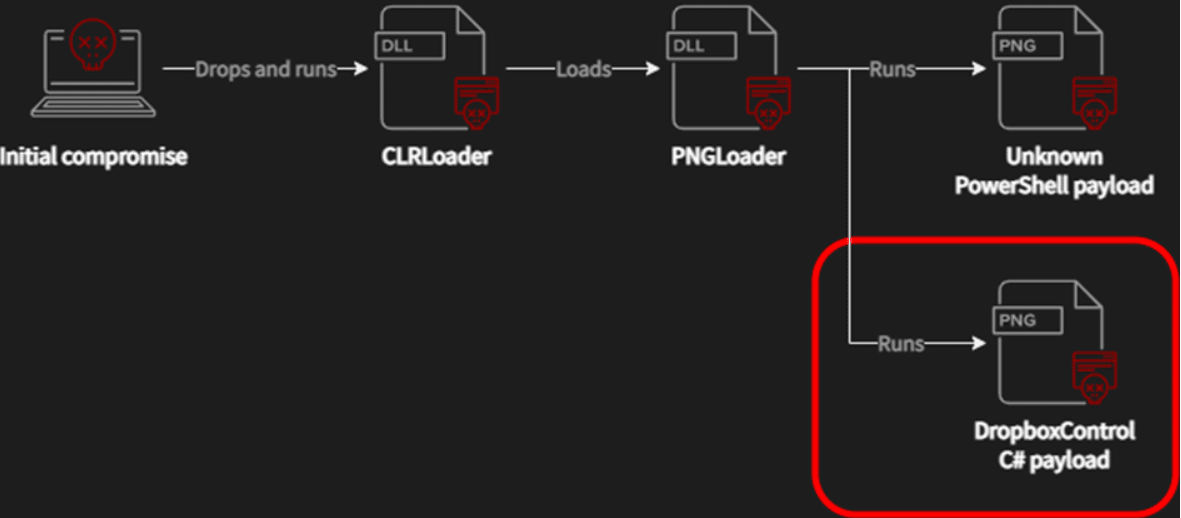
Avast confirmed the Worok findings of ESET researchers and contributed to the expansion of the attack chain.
The tools used by Worok, which capture data through Dropbox accounts registered in active Google e-mails, are not very common; It is considered to be an APT project focused on high-profile organizations in the private and public sectors in Asia, Africa and North America.
As a precaution against targeted cyber attacks;
- E-Mails, attachments, and links from suspicious parties should not be respected,
- Files or programs should be downloaded from reliable sources,
- The most up-to-date versions of existing systems/programs should be used,
- It is recommended to block IoC findings related to the attack campaign by security solutions.
New KmsdBot Malware Detected for Crypto Mining Activities and DDoS Attacks
Cyber security researchers have detected malware called KmsdBot, which carries out DDoS attacks and cryptocurrency mining activities by accessing targeted systems using the SSH cryptographic network protocol.
KmsdBot malware is distributed on systems with weak SSH credentials by downloading the “kmsd.exe” file from a server (C2) controlled by threat actors.
KmsdBot malware has the ability to perform scanning activities on targeted systems, spread to different systems through username and password combinations, control cryptocurrency mining processes and update itself. In addition, the malware has been found to organize DDoS attacks in which Layer 4 TCP/UDP or Layer 7 HTTP/GET requests are sent to strain the targeted server resources and hinder the server’s ability to process and respond.
It is known that the number of malware that carries out cryptocurrency mining activities is increasing day by day. In the recently detected cryptocurrency mining malware campaign called KmsdBot, threat actors target gaming, automobile, and security companies. In this context, in order not to be targeted by the related malware campaign;
- Use public key authentication for SSH connections,
- Not using weak or default credentials for servers or deployed applications,
- Do not open attachments/links from suspicious-looking sender e-mail addresses,
- Beware of unreliable content,
- Use of up-to-date and comprehensive security solutions,
- Keeping systems and applications up to date,
It is strongly recommended that IoC findings related to the attack campaign are blocked by security solutions.






