Critical Vulnerabilities on Lenovo ThinkPad X13s BIOS
Security vulnerabilities have been identified that affect the BIOS software of Lenovo ThinkPad X13s model devices and may cause threat actors to execute code remotely on the affected system and access sensitive data of the local user. (Reference Link)
The details of the identified vulnerabilities are as follows;
The vulnerabilities tracked as CVE-2022-40516, CVE-2022-40517, and CVE-2022-40520, are stack-based buffer overflow security vulnerabilities that could allow a local threat actor with elevated privileges to cause memory corruption in the Qualcomm BIOS.
The vulnerabilities, tracked as CVE-2022-40518 and CVE-2022-40519 in the Qualcomm BIOS, allow a local threat actor with elevated privileges to access memory contents.
The vulnerabilities tracked as CVE-2022-4432, CVE-2022-4433, CVE-2022-4434, and CVE-2022-4435, which are in the ThinkPad X13s BIOS, allow a local threat actor with elevated privileges to access memory contents.
These vulnerabilities affect versions before ThinkPad X13s BIOS 1.47. To avoid being the target of attacks that can be carried out using vulnerabilities, it is recommended to upgrade to current versions that fix the vulnerability.
Godfather Trojan Activity Targeting Financial Sector Detected
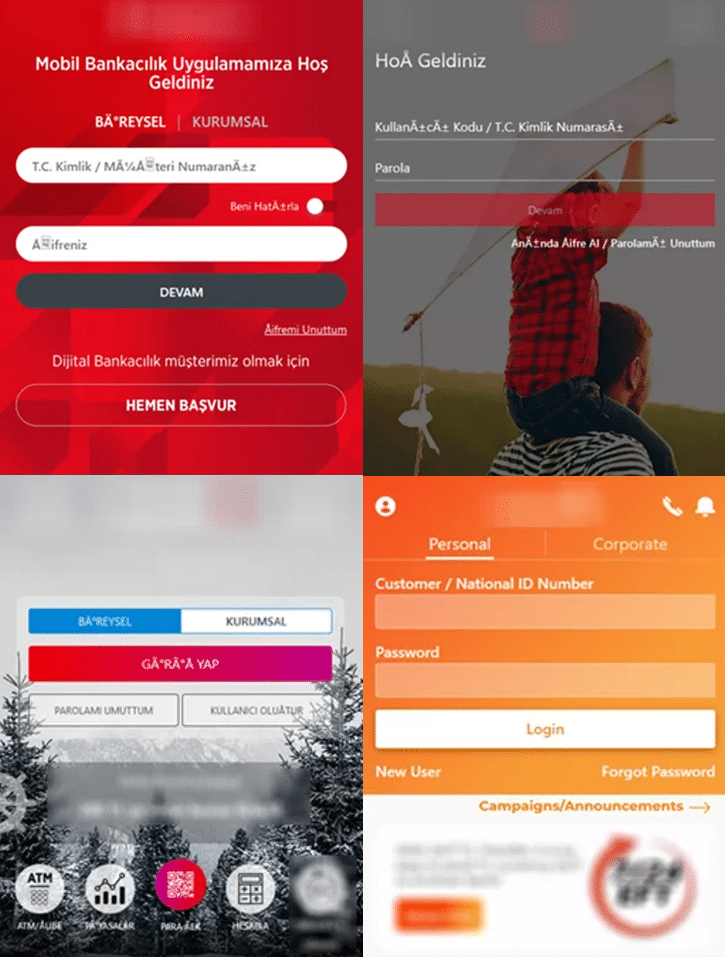
The Group-IB Threat Intelligence team detected that the Godfather Android banking trojan targeted more than 400 international financial companies between June 2021 and October 2022. Half of the targeted financial companies are banks, and the other half are cryptocurrency wallets and exchanges. The Godfather’s targets include 49 US-based companies, 31 Turkish-based companies, and 30 Spanish-based companies. Financial service providers in Canada, France, Germany, England, Italy, and Poland are among the hardest-hit companies.
The Godfather trojan was developed using the source code of another banking trojan called Anubis. However, The Godfather differs from Anubis with its updated functionality, such as updated command and control (C&C) communication, traffic encryption algorithm, a new module for managing virtual network computing (VNC) connections, and Google Authenticator OTPs. The Godfather is distributed through fake apps hosted on Google Play. Fake pages are placed on Godfather-infected devices. These fake web pages are opened when users click on fake notifications or open legitimate apps targeted by the Godfather. All data entered on these pages (usernames and passwords) is sent to command and control (C&C) servers.
Some activities that Godfather trojan software performs on infected systems;
- Recording the device’s screen
- Creating VNC connections
- Capturing keystrokes (keylogging)
- Leaking push notifications and SMS messages (to bypass 2FA)
- Send SMS messages
- Forward calls
- Execute USSD requests
- Start proxy servers
- Enabling silent mode
- Establishing WebSocket connections
A Godfather sample analyzed in September 2022 was observed to mimic Google Protect. When a user launches a malicious application, the application imitates the legitimate Google application, but the Godfather activities are running in the background. Once the malware is launched, it persists on the infected device, creates a pinned notification, and hides its icon from the list of installed apps. Considering these details, it is recommended to consider the following security recommendations to avoid being a victim of targeted attacks that the Godfather malware may carry out.
- Emails, attachments, and links from unknown parties should not be respected.
- Downloaded applications should be downloaded from legitimate application stores, and by checking the evaluations made,
- Comprehensive security solutions should be used.
Deezer User Data Detected Shared on Underground Forums
Deezer was exposed to a security breach in September 2019 that resulted in a user data vulnerability. Deezer stated that the breach was carried out by compromising the security of 3rd party partners and that users’ sensitive data, such as payment information or passwords, were not affected by the breach. However, during the intelligence studies, it was detected that threat actors in underground forums leaked the user data obtained in the September 2019 breach.
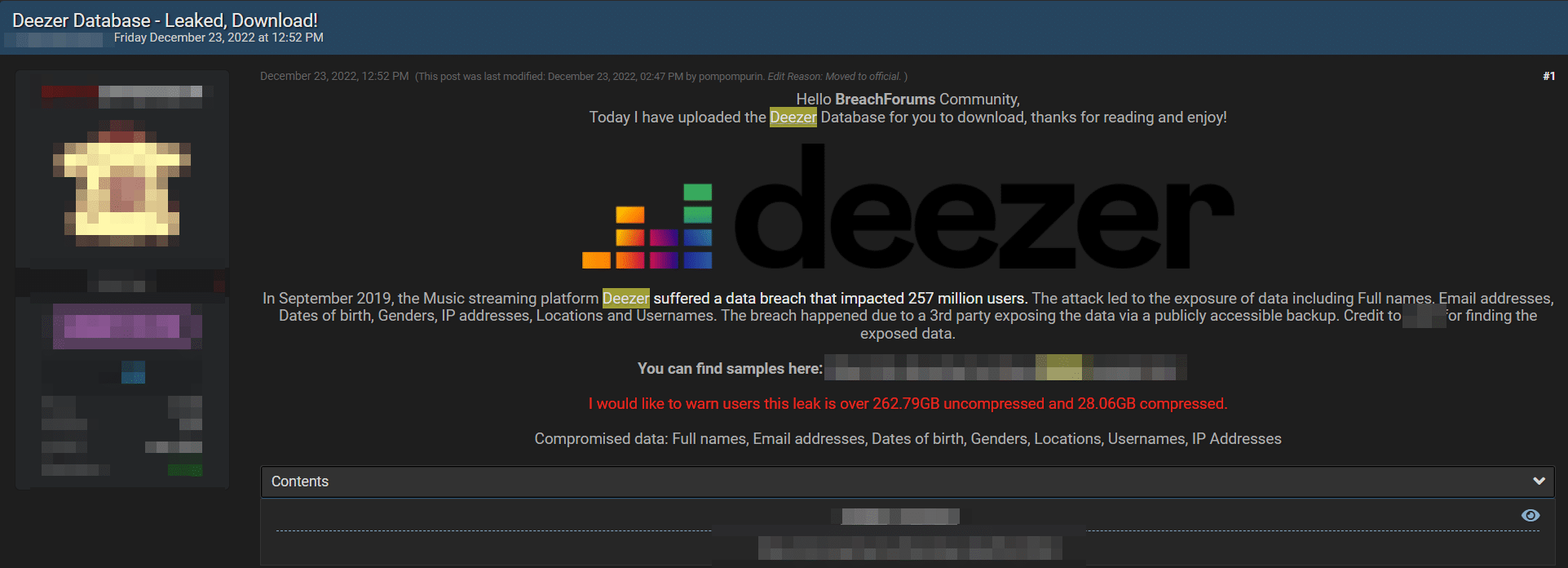
The leaked data includes various personal data of Deezer users, such as name, surname, gender, date of birth, e-mail address, location information, IP address, and username. Threat actors who shared the post stated that the breach occurred because a third party made a publicly accessible backup of the data.
Deezer users are advised to be aware of the leaked data, not to trust e-mails, attachments, and links from unknown parties, and to change the password information used on the platform by applying strong password policies. In addition, it is recommended that institutions/organizations and companies store and back up their data in a secure and inaccessible way, keep their systems up-to-date, and benefit from comprehensive security solutions in order not to be the target of data breaches.






