A phishing campaign begins with the delivery of e-mails containing a malicious link to targets. Threat actors create newly registered phishing domains to target users of Microsoft mail services. An HTML page is opened in the user’s browser when users open the malicious phishing URL in the phishing e-mail, which allegedly contains details about an incoming invoice. The HTML page uses the window.location.replace() function to redirect visitors to phishing pages controlled by threat actors. Using multiple URL redirection methods helps avoid the campaign’s detection by corporate e-mail URL analysis solutions.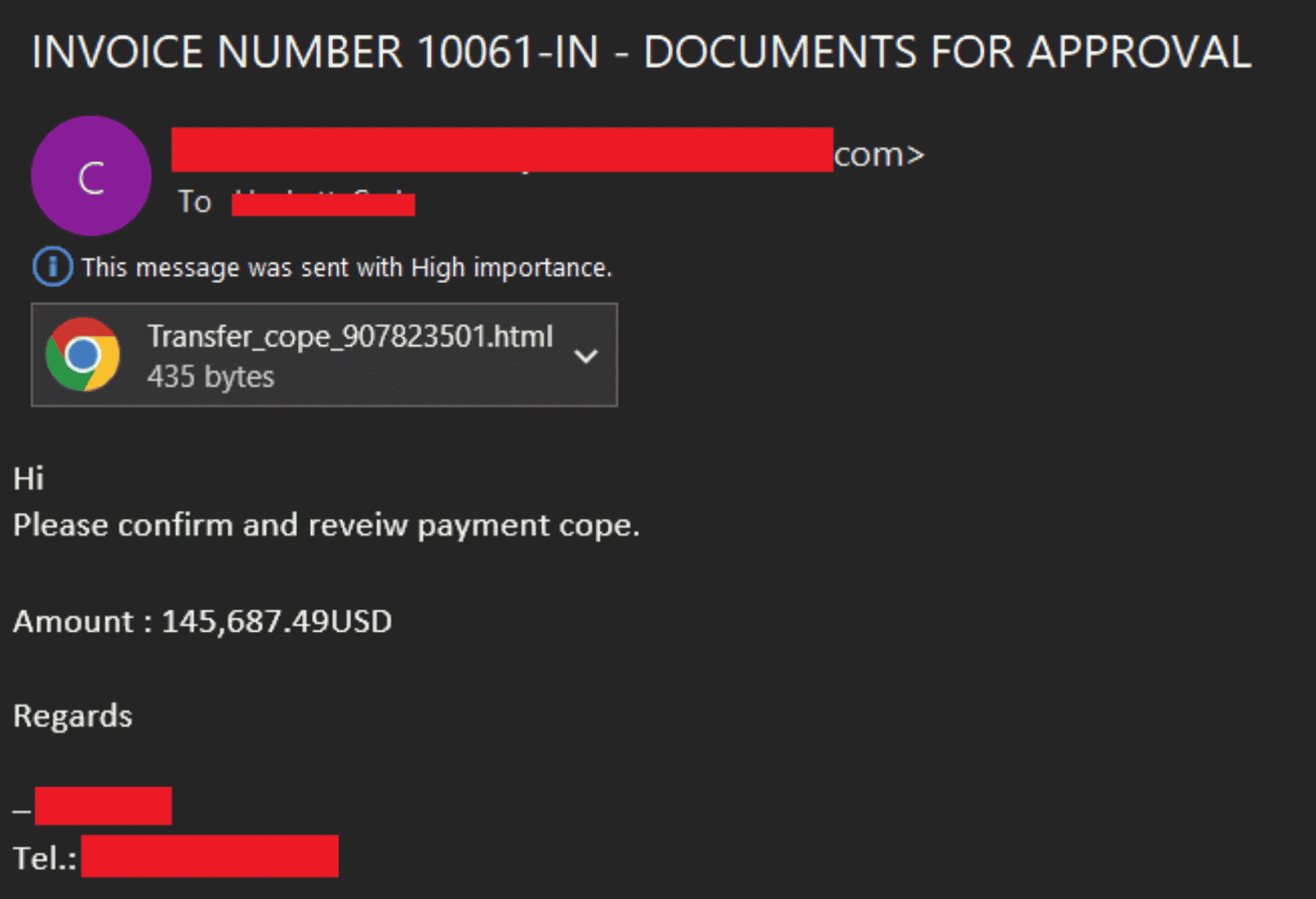
- Evilginx2
- Muraena
- Modlishka
In addition, abuse of legitimate online code editing services such as CodeSandbox and Glitch has also been observed to ensure the longevity of the campaign process. The campaign targets the FinTech, Finance, Insurance, Accounting, and Energy sectors, which generally provide services in the USA, England, New Zealand, and Australia. In addition, it has been observed that threat actors register domain names impersonating Federal Credit Unions outside of Microsoft.
Business e-mail security (BEC) remains an ever-present threat to organizations. The campaign underlines the importance of the need to protect against similar attacks, which are increasing day by day. In order not to be the target of similar advanced phishing attacks that may be carried out in this context, it is recommended to implement the following security measures.
- E-mails, attachments, and links from unknown and suspicious parties should not be respected,
- Sensitive information should not be used on platforms that are not sure of its reliability,
- Comprehensive Anti-Virus / Anti-Malware security solutions should be used,
- Institution/organization personnel should be made aware of potential phishing/social engineering attacks,
- Detected IOC findings related to the campaign should be blocked from security solutions.






