The campaign begins with the web apps of cleaning services Grabmaid, Maria’s Cleaning, Maid4u, YourMaid, Maideasy, MaidACall, and a pet store PetsMore imitated by threat actors and delivered to their targets via Facebook ads. However, these fake web apps do not offer targets the option to make direct online purchases. Instead, targets are requested to download the relevant apps from the Google Play app store. However, the “Download” buttons provided for users to download the application via Google Play do not direct users to Google Play but to servers under the control of threat actors.
Successful execution of the campaign requires Android users to enable the “Install Unknown Apps” option on their devices. Additionally, it has been observed that some of the fake web applications in question do not have an Android application on Google Play, contrary to what is claimed.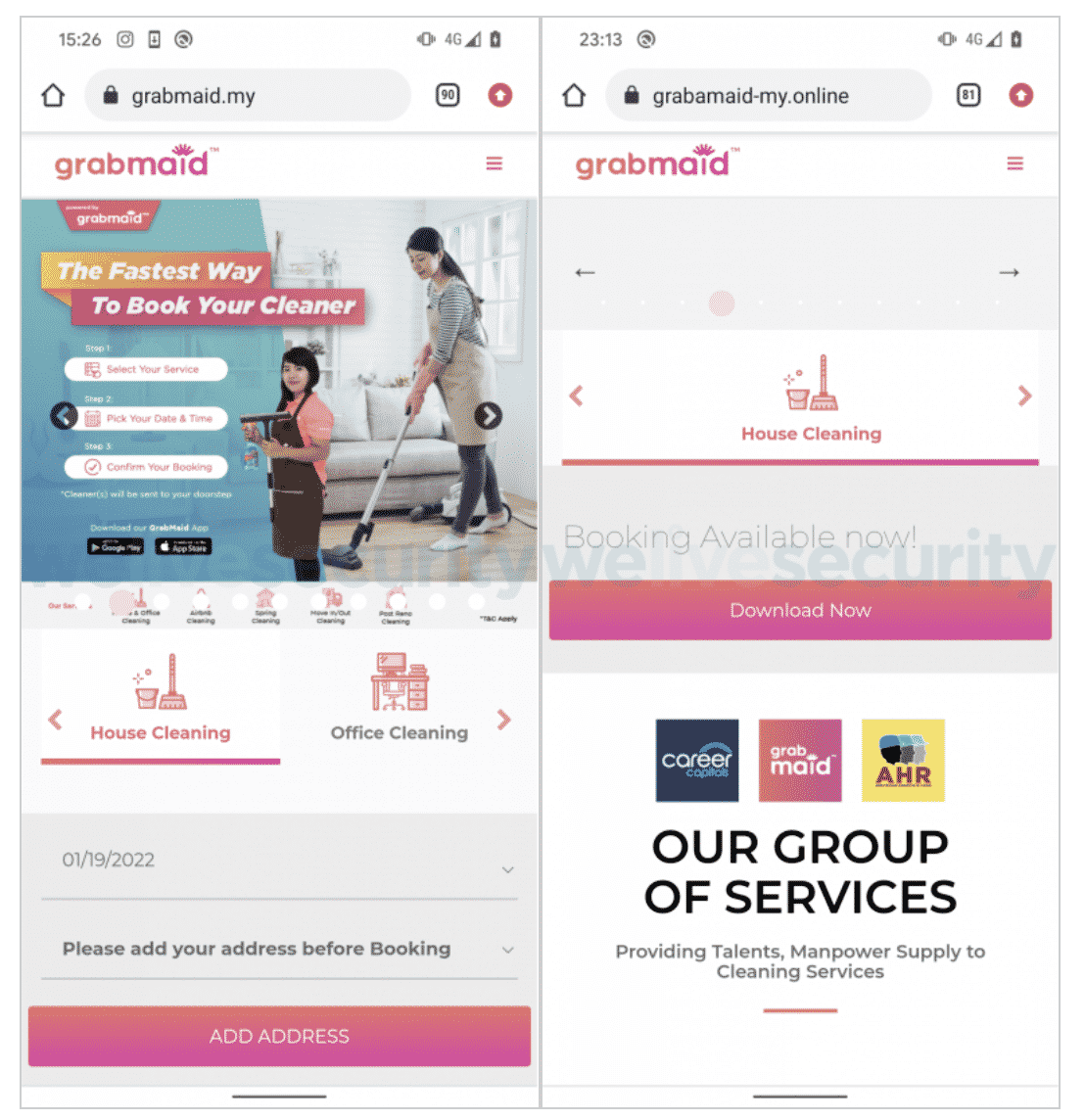 Applications require users to login to appear legitimate after they are downloaded and launched; however, there is no account verification mechanism on the server-side. Apps with the appearance of a real e-store imitate the interface of the original stores, offering the option to order and pay for the goods and services purchased. The targets can pay by credit card or by transferring the required amount from their bank accounts at the next stage. Users who choose the direct transfer option are presented with a fake FPX checkout page and are asked to select their bank from among the eight Malaysian banks provided and then enter their credentials.
Applications require users to login to appear legitimate after they are downloaded and launched; however, there is no account verification mechanism on the server-side. Apps with the appearance of a real e-store imitate the interface of the original stores, offering the option to order and pay for the goods and services purchased. The targets can pay by credit card or by transferring the required amount from their bank accounts at the next stage. Users who choose the direct transfer option are presented with a fake FPX checkout page and are asked to select their bank from among the eight Malaysian banks provided and then enter their credentials.
It has been observed that the targeted banks are Maybank, Affin Bank, Public Bank Berhad, CIMB Bank, BSN, RHB, Bank Islam Malaysia, and Hong Leong Bank operating in Malaysia. At the last stage, an error message is sent to the end-users that provide their banking information as input, stating that the username and password are invalid. As a result, the bank information entered by the user is captured by threat actors.
In order not to be the target of similar campaigns, should not respect advertisements observed on social media platforms, application downloads should be made through reliable application stores, the reliability of platforms where critical information is requested should be checked, 2FA / MFA features should be enabled on every possible platform.






