During the intelligence studies, it was determined that LinkedIn, a business network and social sharing platform, is frequently used by threat actors in phishing activities carried out through various methods.
Linkedln, which provides reliability for users due to being a professional platform, creates a suitable ground for fraudulent activities carried out by threat actors. Some examples of campaigns where the LinkedIn platform has been manipulated using phishing or social engineering activities are detailed below;
Fake Notifications
By taking advantage of the notifications that LinkedIn users frequently encounter, threat actors can send phishing e-mails designed to infect users’ systems with malware or capture login credentials. These e-mails attract users’ attention by containing phrases such as “1 person viewed your profile”, “You’ve been viewed in 3 searches this week,” or “Congratulations on your connection’s new position,” which LinkedIn users are pretty familiar with.
When users click on the link in the e-mail, they are directed to a LinkedIn login page that requests login credentials. At the last stage, all other services where users logging in with LinkedIn username and password information use the same authentication are compromised by threat actors.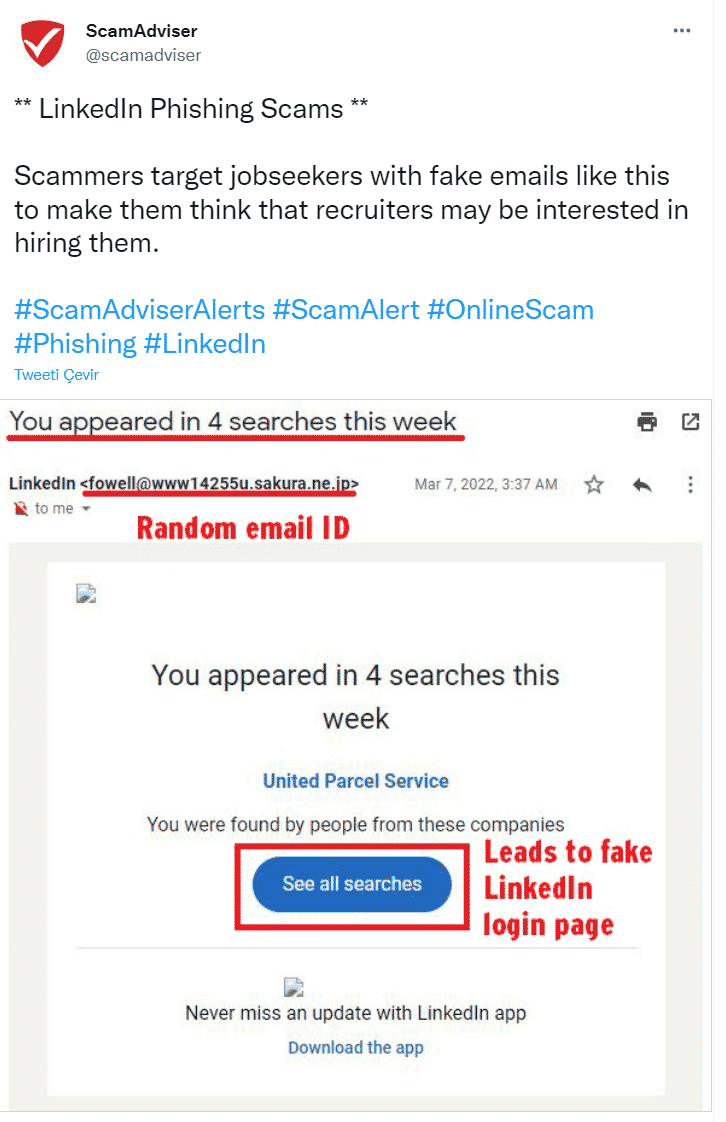
Fake Job Offers
To obtain LinkedIn users’ login and personal information, threat actors can communicate via direct message with the promise of high-paying job offers, causing users to open a malicious link if caught off guard. Scenarios are also observed in which threat actors, motivated to obtain more information about users, charge a certain fee to fill in personal information via Google Forms and obtain users’ bank information.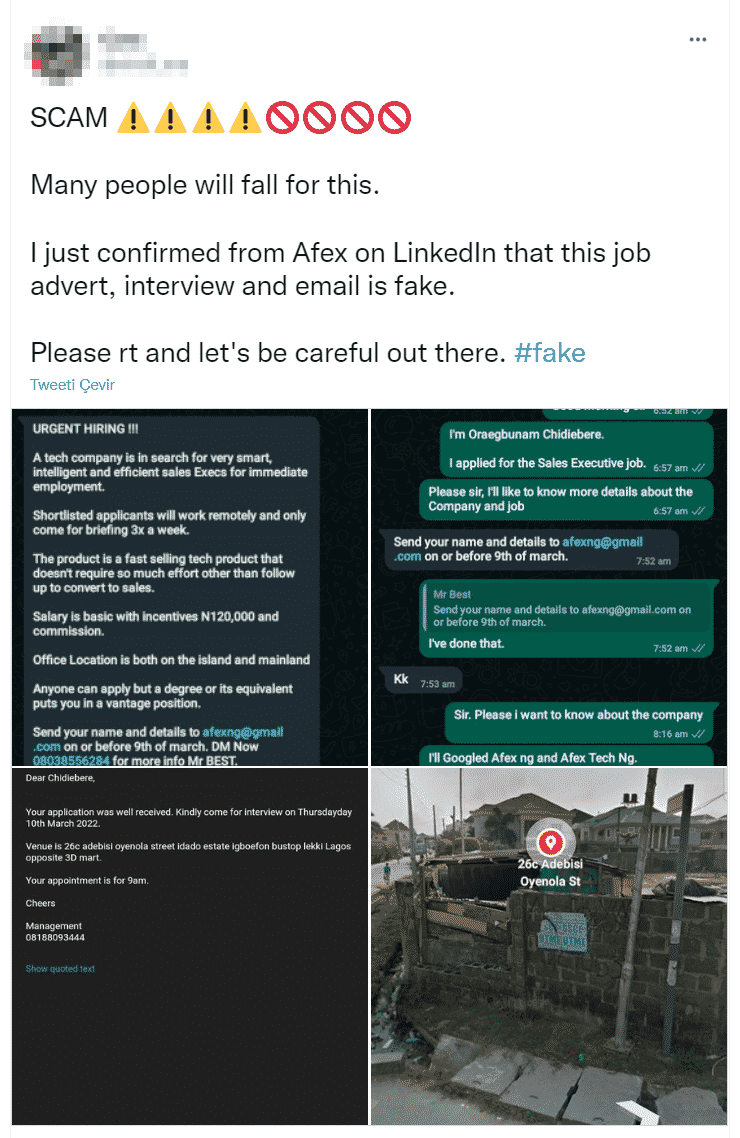
Fake Financial Advisory Offers
It is a frequently observed situation that LinkedIn users are also targeted in Forex and cryptocurrency fraud activities carried out by threat actors. A well-trained and legal financial advisor reaches out to users with a “great investment” offer and convinces users to make the requested investment through a series of social engineering methods. In this process, professionally created web pages and content are used to ensure reliability. At the last stage, the convinced users are provided to transfer money or crypto money for the promised investment, and their bank/wallet and personal information are captured.
In order not to be the target of phishing/social engineering activities that can be carried out using the aforementioned methods, it is recommended to disregard suspicious-looking e-mails, attachments, and links that appear to come from LinkedIn, instead checking LinkedIn notifications directly. In addition, it is important to be careful about connection and message requests from unknown people, to control the privacy settings in case the personal information used on LinkedIn is public, and to create the login information used in the accounts using strong policies.






