Cryptocurrency Scammers Targeted Elon Musk with Deepfake Technology
Cryptocurrency scammers have been found to use the Deepfake video content of Elon Musk and other leading cryptocurrency advocates to promote a fake BitVex trading platform. The fake BitVex platform, allegedly owned by Elon Musk by threat actors, is known to hijack the currency deposited by visitors.
The scam campaign started when threat actors created fake YouTube accounts to host Deepfake-generated videos of Elon Musk, Cathie Wood, Brad Garlinghouse, Michael Saylor, and Charles Hoskinson in early May 2022. Deepfake is a technology in which a person in an existing image or video can be replaced with another person’s image using artificial neural networks.
In these videos, it is stated that Elon Musk introduced the fake BitVex platform created by fraudulent activities and invested $ 50 million in the platform. When the interviews conducted in the videos are examined, it is understood that Elon Musk’s voice was changed by simulating to promote the BitVex trading platform, but many different findings reveal that this is a fraudulent activity.
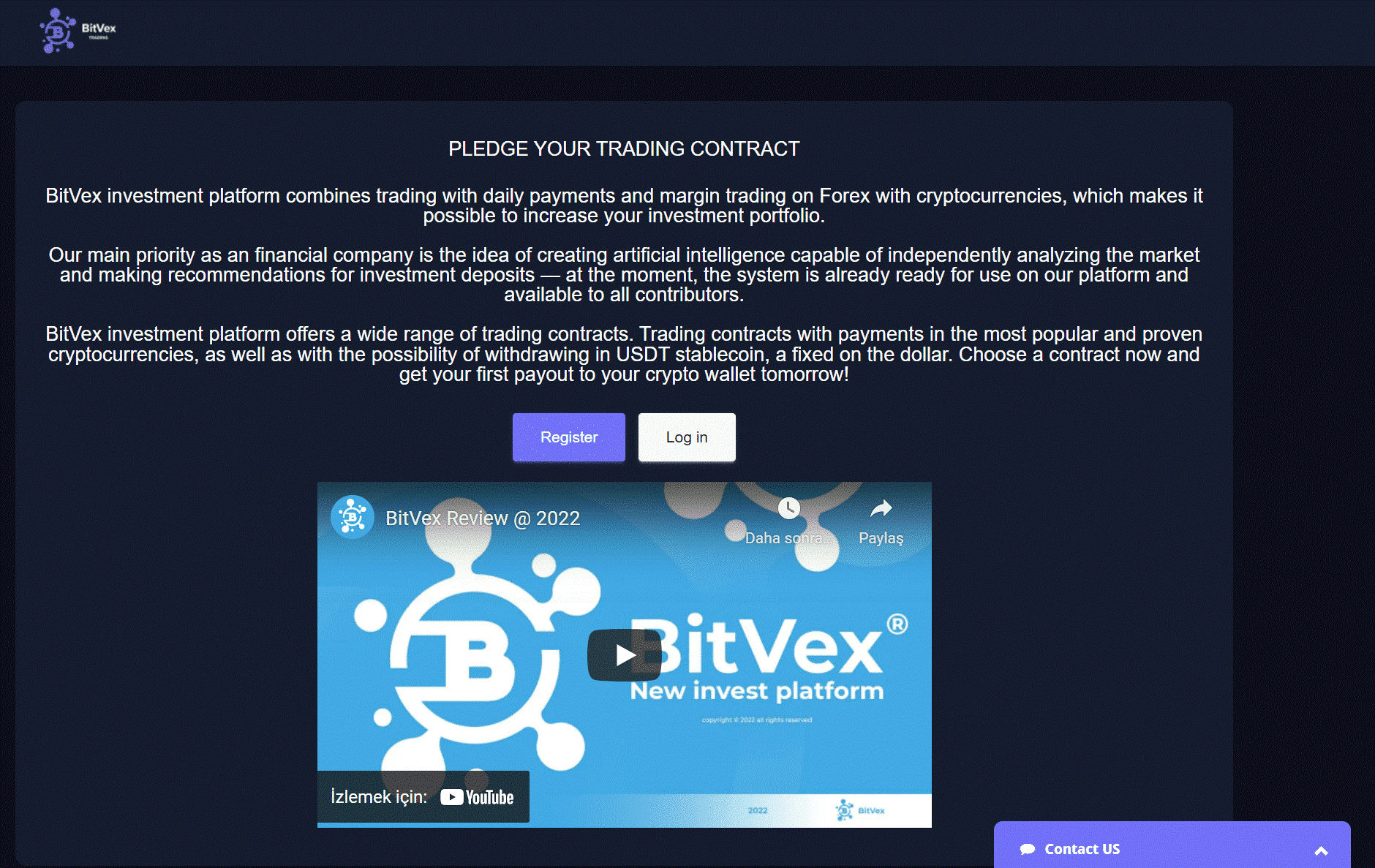 The fake BitVex platform allegedly contains and references endorsements by Elon Musk and Cathie Wood, CEO of investment firm Ark Invest, and Changpeng Zhao, CEO of Binance. Users who want to use the BitVex platform must open an account at bitvex[.]org or bitvex[.]net to access the investment platform. After logging into the platforms, a relatively legitimate-looking dashboard is displayed where users can deposit various cryptocurrencies, choose an investment plan or withdraw their earnings.
The fake BitVex platform allegedly contains and references endorsements by Elon Musk and Cathie Wood, CEO of investment firm Ark Invest, and Changpeng Zhao, CEO of Binance. Users who want to use the BitVex platform must open an account at bitvex[.]org or bitvex[.]net to access the investment platform. After logging into the platforms, a relatively legitimate-looking dashboard is displayed where users can deposit various cryptocurrencies, choose an investment plan or withdraw their earnings.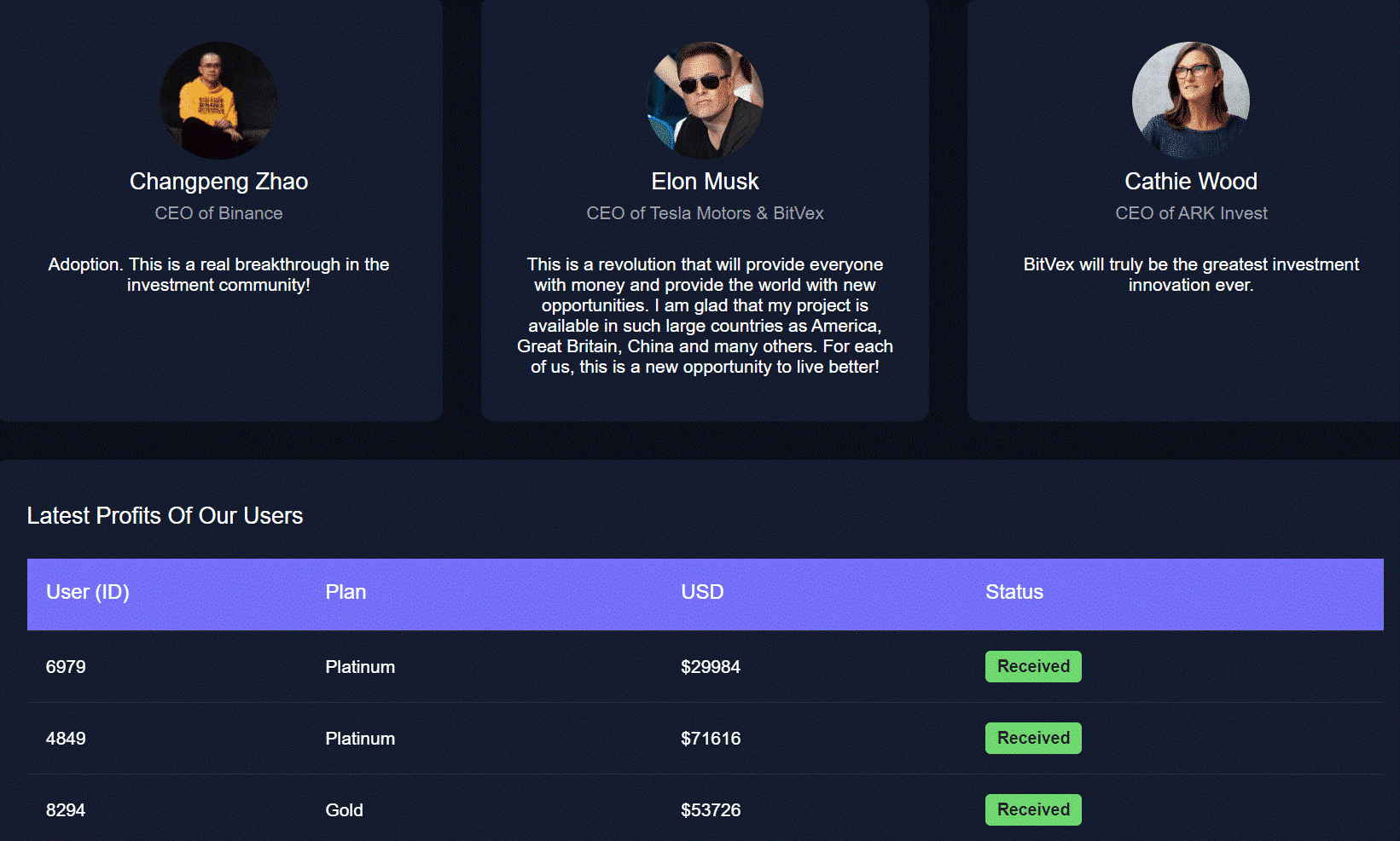
The perpetuation of such fraudulent activities by threat actors has become quite common and profitable. The FTC (Federal Trade Commission) has issued a warning that since October 2020, $80 Million worth of financial losses has been incurred due to cryptocurrency investment scams.
In this context, to not be the target of similar campaigns, crypto money users need to verify the validity of the crypto wallet application to be used before investment transactions. The simplest method for the verification process is to perform transactions with only a small amount in practice. Crypto scammers often use social media to promote their fraudulent schemes, as in the case under consideration. For this reason, it is recommended not to be trusted when faced with crypto opportunities promoted on social media.
New Goal of Fraud and Phishing Activities: LinkedIn Users
During the intelligence studies, it was determined that LinkedIn, a business network and social sharing platform, is frequently used by threat actors in phishing activities carried out through various methods.
Linkedln, which provides reliability for users due to being a professional platform, creates a suitable ground for fraudulent activities carried out by threat actors. Some examples of campaigns where the LinkedIn platform has been manipulated using phishing or social engineering activities are detailed below;
Fake Notifications
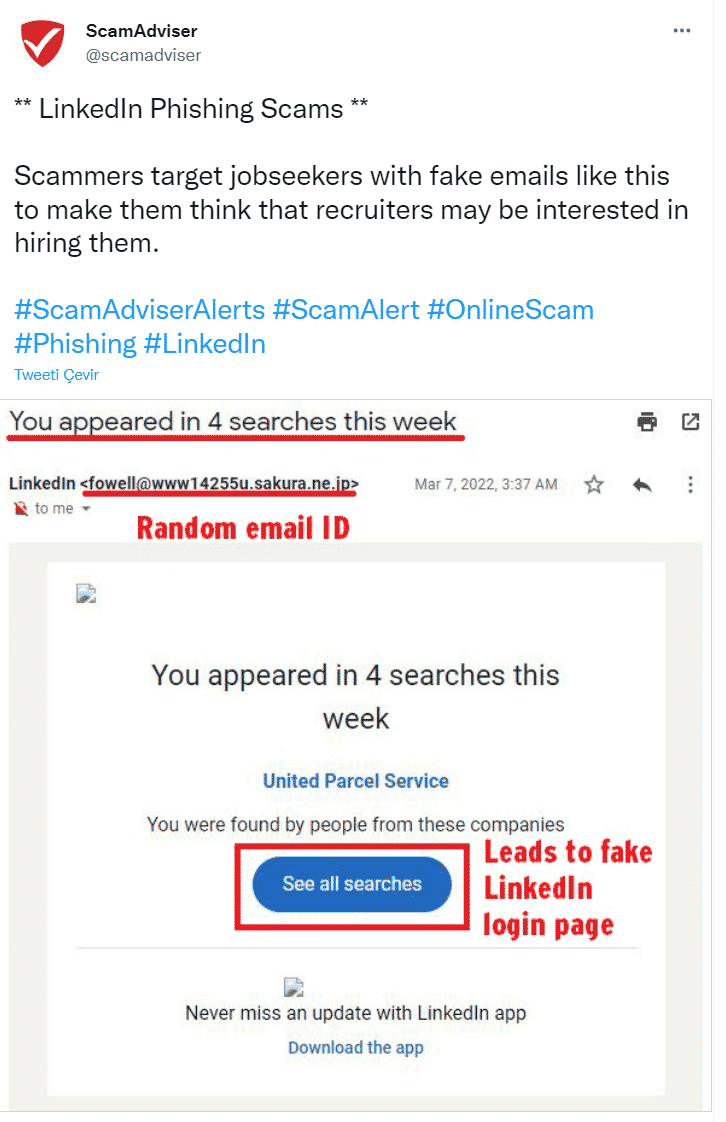
By taking advantage of the notifications that LinkedIn users frequently encounter, threat actors can send phishing e-mails designed to infect users’ systems with malware or capture login credentials. These e-mails attract users’ attention by containing phrases such as “1 person viewed your profile”, “You’ve been viewed in 3 searches this week,” or “Congratulations on your connection’s new position,” which LinkedIn users are pretty familiar with.
When users click on the link in the e-mail, they are directed to a LinkedIn login page that requests login credentials. At the last stage, all other services where users logging in with LinkedIn username and password information use the same authentication are compromised by threat actors.
Fake Job Offers
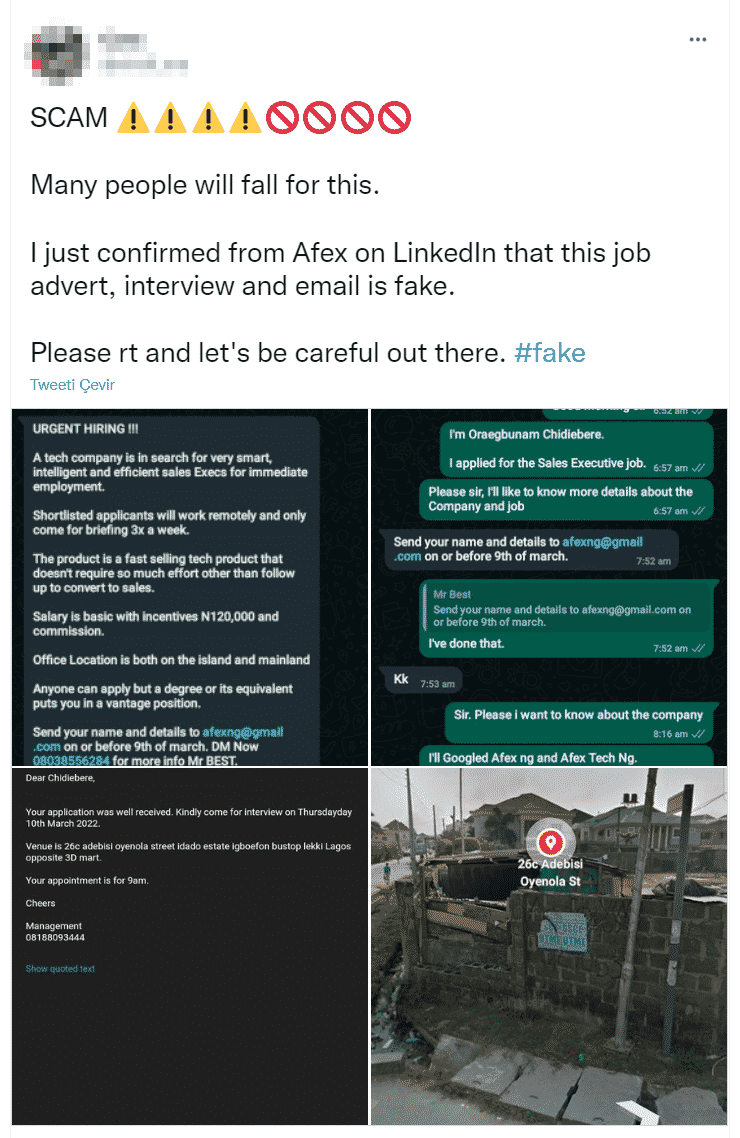
To obtain LinkedIn users’ login and personal information, threat actors can communicate via direct message with the promise of high-paying job offers, causing users to open a malicious link if caught off guard. Scenarios are also observed in which threat actors, motivated to obtain more information about users, charge a certain fee to fill in personal information via Google Forms and obtain users’ bank information.
Fake Financial Advisory Offers
It is a frequently observed situation that LinkedIn users are also targeted in Forex and cryptocurrency fraud activities carried out by threat actors. A well-trained and legal financial advisor reaches out to users with a “great investment” offer and convinces users to make the requested investment through a series of social engineering methods. In this process, professionally created web pages and content are used to ensure reliability. At the last stage, the convinced users are provided to transfer money or crypto money for the promised investment, and their bank/wallet and personal information are captured.
In order not to be the target of phishing/social engineering activities that can be carried out using the aforementioned methods, it is recommended to disregard suspicious-looking e-mails, attachments, and links that appear to come from LinkedIn, instead checking LinkedIn notifications directly. In addition, it is important to be careful about connection and message requests from unknown people, to control the privacy settings in case the personal information used on LinkedIn is public, and to create the login information used in the accounts using strong policies.
The New Phishing Attack Using Multiple Malware Types
A phishing campaign targeting Microsoft Windows users used three different types of malware designed to snatch sensitive information from targets.
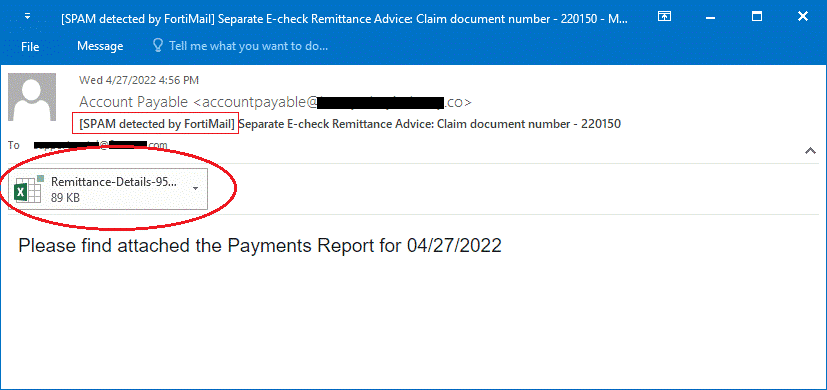
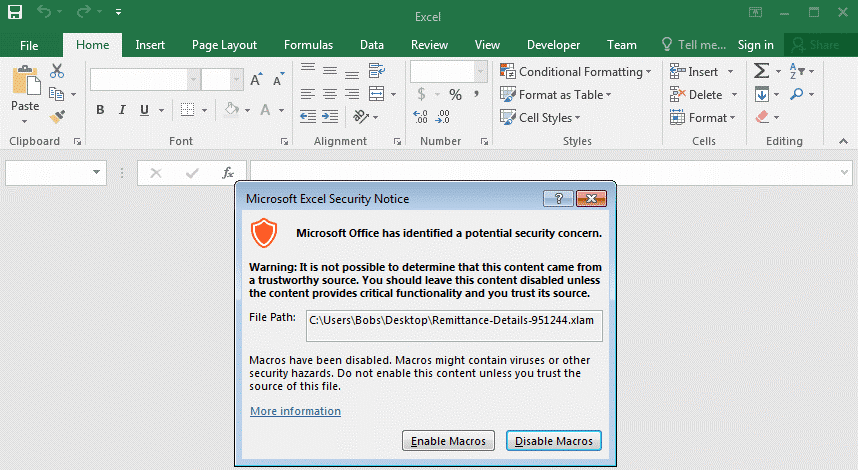
The chain of attacks begins with sending spear-phishing emails containing a malicious Excel document to the targets, which appears to be a payment report notification from a trusted source. Emails try to persuade recipients to open the attached Excel document for report detail. When the Excel file called “Remittance-Details-951244.xlam” is opened, and the macro is activated, a VBA (Visual Basic Application) script called “Auto_Open()” is executed, which is responsible for downloading the malware to be used in the campaign.
As a result of a series of steps performed through Powershell and the stated VBA scripts, malicious software called AveMariaRAT, BitRAT, and PandoraHVNC, which is responsible for capturing users’ sensitive information, including passwords and bank information, is downloaded to the target system. BitRAT can take full control of infected Windows systems, monitor webcam activity, listen to audio over the microphone, allow threat actors to perform undetected transactions on compromised cryptocurrency wallets, and download additional malicious files, which is why it was considered particularly dangerous.