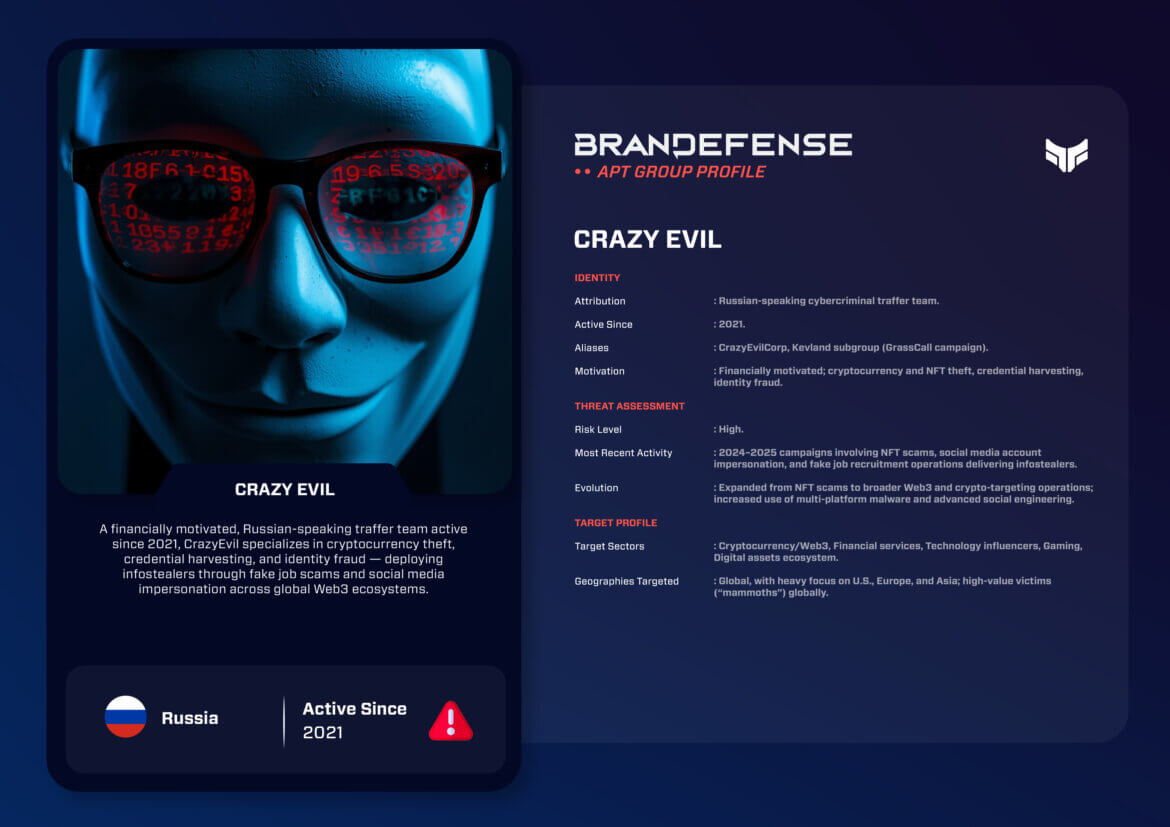
The evolution of cyber crime in the cryptocurrency and Web3 era has given rise to increasingly sophisticated threat actors that blend scalable malware distribution with advanced social engineering. Crazy Evil is among the most prolific Russian-speaking traffer teams known to be active today. Utilizing Telegram, dark web forums, and an expanding phishing infrastructure in service of their operations, the group has become a key facilitator of global digital asset theft. This blog provides a framework intelligence overview of Crazy Evil – who they are, the tactics they use, what operations they conduct, and the traits that keep them a persistent threat into 2025.
Introduction: A New Breed of Cybercriminal Actor
Crazy Evil represents a new type of organized crime in the digital world – blending traditional phishing methods with high-volume social engineering, specialized breaking and entering subteams (aka “traffers”), and multi-platform infostealer malware. While Far Away is not a state-sponsored APT, the group shows operational discipline and scale similar to many established threat clusters. Crazy Evil particularly jeopardizes individuals and organizations associated with NFT markets, cryptocurrency platforms, Web3 startups, developers, and digital influencers.
Threat intelligence providers and cybersecurity vendors make repeated mention of the rise in frequency and scale of financially motivated operations that target credential theft, wallet draining, and identity fraud. Crazy Evil fits in this category easily. As Crazy Evil has won monetization opportunities following the collapse or related disruption of rival cybercrime groups, they have absorbed traffers and expanded their operation into a global network.
Identity and Motivation
Crazy Evil is a Russian-speaking cybercriminal organization that has operated since 2021. While many ransomware gangs and botnet operators may be similar, they function as a traffer team (a decentralized team of social engineering professionals) moving legitimate web traffic towards a malicious payload.
The group has public and semi-public Telegram channels with thousands of members. Subteams like Kevland (that promote the GrassCall campaign) post dedicated lure postings, including the recent variant of fake job recruitment targeting Web3 professionals.
What Drives Crazy Evil?
The group’s motivations are strictly financial based on:
– Theft of cryptocurrency and NFTs
– Breaches of high-value influencer and developer accounts
– Large-scale distribution of infostealer malware
– Credential harvesting for resell/reuse in future theft
As Web3 and DeFi ecosystems expand, so do potential attacks by groups like Crazy Evil, against wallets, applications, and identities, utilizing increasingly sophisticated techniques.
TTPs: How Crazy Evil Operates
The organization’s cookbook covers the attack lifecycle across many levels, combining human deception with high automation of its malware.
1. Initial Access
Crazy Evil hinges predominantly on social engineering to gain access to victims, including:
– Fake NFT airdrops to promise early access
– The impersonation of influencers or founders of projects
– Phishing links sent via Telegram, Discord, X, Instagram
– Malvertising campaigns aimed at crypto-related search terms
– GrassCall job recruitment scams that fooled candidates into downloading malware disguised as entry tools
These strategies tapped into trust and excitement in a Web3 opportunity.
2. Persistence
After malware deployed, the group established footholds by:
– Modifications of the auto-start registry (for windows)
– Launch agents (for macOS)
– Browser-based extensions for session theft
– Cloud-based theft of authentication tokens
Persistence shifts the odds in favor of prolonged access, even when the victim was aware of a compromise.
3. Command & Control
Crazy Evil prefers:
– Telegram bots to coordinate in real-time.
– An encrypted web-based dashboard to manage and facilitate the stolen data.
– Domain infrastructure frequently rotating while using fast-flux.
This decentralized approach provides increased resiliency and diminishes the risk of attribution.
4. Malware & Tooling
This group has deployed a diverse malware toolkit that is in line with modern infostealer trends:
– RedLine, Lumma, Rhadamanthys, MetaStealer (core infostealers)
– Multi-vector payloads targeting Windows and macOS
– Browser-drainer extensions
– NFT and Cryptocurrency wallet phishing kits
The group avoids a lot of detection mechanisms that are built on enterprise threats because they spend their resources and time on credential theft and wallet theft rather than relying on ransomware.

Notable Operations: A Timeline of Growth
2021 – Early NFT Drainer Operations
Crazy Evil starts distributing simple wallet drainer pages associated with smaller NFT projects.
2022–2023 – Expansion Through Dark Web Recruitment
The group stabilizes an organized traffer network, accumulating over 3,000 followers on Telegram.
2024 – Mass Infection Campaigns
Multi-OS infostealers are spread through influencer-targeted scams, in thousands of cases infecting tens of thousands of users globally.
2025 – The GrassCall Job Recruitment Campaign
The new Crazy Evil subgroup calls itself Kevland, targeting job interview scams at Web3 candidates that also drain their wallets.
The scale and sophistication established through 2025 places Crazy Evil among the most active financial motivated threat groups around the globe.
Recent Developments and Evolution
The recent activity of Crazy Evil demonstrates a strategic pivot:
– Expanding beyond NFTs into fintech, gaming, and online banking
– Utilizing browser extensions for long-term access
– Utilizing profiles and messages developed by AI to enhance social engineering success rates
– Increased use of cross-platform malware, suggesting more varied systems of victims
– Use of better decentralized C2 techniques similar to APT-level operational security
Such flexibility in behavior is similar to the greater trend across cybercrime where criminals move quick to enhance their infrastructure to exploit the next digital ecosystem.
Conclusion: Strategic Impact and Defensive Takeaways
Crazy Evil exemplifies how actors focusing on financial gain compete with traditional APTs with operational tempo, persistence and cross global reach. Crazy Evil’s target focus on high-value Web3-usage combined with wide-ranging, easily deployed malware and compelling social engineering makes this financially motivated actor a serious concern.
Key Defensive Recommendations
– Require hardware wallets for all high-value digital assets
– Educate teams on recruitment use cases targeting crypto and tech jobs
– Monitor for infostealer logs for exposed credentials and logins
– Utilize phishing-resistant MFA using FIDO2
– Audit browser extensions
– Aware for new NFT-drainer kits and wallet-draining scripts
As we begin to navigate 2025, Crazy Evil serves to showcase how quickly cyber crime can proliferate, when leveraging excitement and volatility over the digital asset space. All organizations and individuals working within the digital asset environment will have to find ways to employ proactive defense strategies to address this adaptive adversary.
You can download and review the sheet for all the details!