Introduction
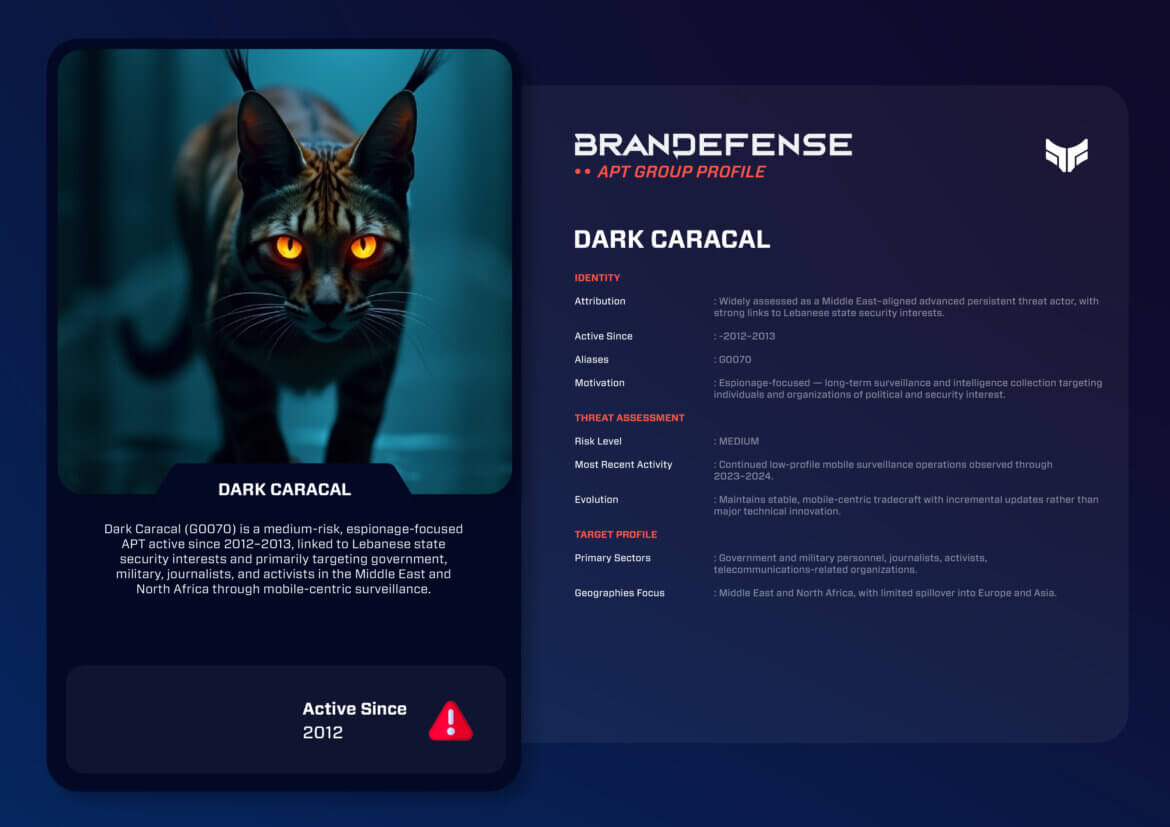
The Dark Caracal group is a unique advanced persistent threat organisation that focuses primarily on collecting long-term intelligence via mobile surveillance, unlike many other APT’s which target entire networks or organisations. Most of Dark Caracal’s operational success relies upon access to devices, most notably Android mobile phones, in order to monitor individuals rather than companies. As such, Dark Caracal is very relevant to discussions regarding digital privacy, targeted surveillance and the overall security of the mobile ecosystem. The Dark Caracal group is also known by the G0070 identifier and has been identified by various sources as being a regional espionage entity with activity that has combined both traditional cyber espionage and mass digital surveillance campaign activities.
Identity and Attribution
Dark Caracal is currently characterized as a nation-state aligned cyber threat from the Middle Eastern region based on the team’s mission of espionage targeting an array of individuals including but not limited to government officials and military members. Dark Caracal has established its identity through open-source investigation work as well as Trends Internationa l2020 analysis to associate Dark Caracal’s infrastructure and operational methodology with entities affiliated with the Lebanese government security services. As such, Dark Caracal is one of only a handful of publicly known APTs associated with that geographic area.
In contrast to most APTs in relation to established cyberpower status, Dark Caracal operates at a very small scale. To counteract this relative lack of technical expertise, Dark Caracal employs persistence-based offensive tactics that utilize relatively simple social engineering techniques to gain access to targeted systems versus relying on advanced malware or zero-day exploits to achieve access. The continued success of Dark Caracal’s operations has been accomplished through the consistent use of targeted surveillance operations as opposed to attacking their targets through advanced methods of sophistication.
Strategic Motivation
Dark Caracal is primarily motivated for the purpose of executing espionage missions. Dark Caracal specifically targets the collection of classified or sensitive forms of personal, political and organizational data from its Intended Targets; often these Intended Targets are made up of either government officials, military officials, journalists, activists and members working in high risk professional environments.
Dark Caracal generally conducts highly targeted operations aimed at achieving specified objectives within the limitations of their resources. In addition, Dark Caracal’s information collection approach means that they are likely responding to specific domestic and operationally oriented intelligence collection directives as part of its respective mission. Examples of these intelligence collection directives include collecting intelligence to monitor political movements and opposition figures, monitoring domestic and international events through the collection of publicly available information, and obtaining situational awareness of a specified geographic area within the Near East.
Tactics, Techniques, and Procedures (TTPs)
The operation of Dark Caracal is based on the use of Mobile Malware and Social Engineering rather than Achieving their Objectives Using Complex Exploitation Chains.
Initial Access
Dark Caracal usually gains their initial access by using Social Engineering Campaigns that trick Victims into Downloading Malicious Applications. These Malicious Applications may be Disguised as:
- Messaging/Chat Applications
- VPN/Security Software
- News/Media Applications
- Productivity/Utility Software.
Distribution of these Malicious Applications comes from either Phishing Emails; Phishing SMS; or Direct Messages On Social Networking Sites. In Many Cases, Dark Caracal Has Also Compromised Legitimate Websites to Serve as the Payloads of Downloadable Malicious Applications.
Execution and Persistence
Once the Installation of the Malicious Application has been Completed, Dark Caracal Malware Will Execute Under the Permissions Granted at the Time of Installation, So There Is No Need for Privilege Escalation Exp. to Run.
Today, Dark Caracal Combines the Persistence of Icons Remaining After Applications Uninstall and Background Processes That Will Recreate After Restart, Making Their Malware appear as Legitimate Applications on a ‘Desktop Computer.’ (if any), Dark Caracal Uses a Simple ‘TROJAN’ and a Simple Remote Access Tool, Which Reflects Dark Caracal’s Preference for Symplicity and Reliability.
Command and Control
Command-and-control (C2) communication typically uses standard internet protocols, such as HTTP and HTTPS; hence servers are often hosted on compromised infrastructure (e.g., Cloud hosting providers) and commercial hosting providers. This group does not have the infrastructure management capabilities of some of the more advanced groups, but it compensates for this weakness by regularly rotating and providing redundancy for its servers.
Collection and Surveillance
The group’s greatest strength is its ability to collect data. The spyware that Dark Caracal has created for mobile devices can collect the following information:
– Call and SMS logs
– Contact book
– GPS location data
– Audio recordings made by the microphone
– Photographs, documents and application data
The ability to collect this type of information from mobile devices provides Dark Caracal with the ability to conduct near real-time surveillance of persons whom they desire to monitor, creating a continuous track record of personal surveillance that goes beyond traditional cyber espionage activities.

Malware and Tooling
The Android spyware framework developed by a hacker collective known as “Dark Caracal” is considered their top signature. The frameworks of Dark Caracal are very modular, allowing the operator to activate / deactivate surveillance functions or features based on the operator’s needs when using them.
Dark Caracal has a secondary method for espionage through its Windows-based malware arsenal; however, Dark Caracal’s Windows malware is typically less sophisticated than its Android equivalent, generally involving credential theft and the exfiltration of data from victims’ systems. Much of Dark Caracal’s tooling is custom-utilizing common open-source components or well-known frameworks.
Target Profile
Dark Caracal focuses on individuals and organizations of intelligence interest on a regional basis. In general, the following is a list of Dark Caracal’s primary targeting categories:
Primary Targets
– Government officials, public servants
– Military personnel and security personnel
– Journalists and media persons
– Civil society members and activists
– Employees of telecommunication and defence-related companies
Geographic Focus
Dark Caracal’s primary targeting areas are:
– Middle East
– North Africa
– Europe and Asia (only those targeting areas that focus on the Middle East)
Victims are selected based on location/relation (not organisational solely).
Notable Operations
Dark Caracal is associated with multiple long-term surveillance projects. From 2014 to 2016, they carried out early mobile espionage with the use of trojanized Android applications, which were mostly distributed through phishing and fake websites. Between 2017 and 2018, Dark Caracal was publicly exposed as having a significant amount of infrastructure and surveillance tools, which had been used to spy on individuals and were linked to buildings of the Lebanese government. From 2019 to 2021, they continued to engage in mobile surveillance (now with even more malicious variants of malware) and still used mobile malware to target journalists and activists. While they continue to conduct their operations in a low-profile way (not drawing attention to themselves), they are still doing so with incremental updates to their technical capabilities.
These long-term surveillance efforts demonstrate a pattern of consistent operations, rather than significantly escalating operations.
Evolution and Current Activity
Following their public exposure, Dark Caracal’s group continued with its operational activities; however, they have changed some of their infrastructure and have made some small improvements in their operational security practices. Many of the original operational practices used by Dark Caracal have not changed. In addition, the primary infection vector for the group continues to remain social engineering and user interaction.
The continued successful use of these methods by such a prominent and publically known threat actor illustrates the fact that even well-known threat actors can be effective if they are able to continue to exploit the trust of humans along with the weakness of user security practices on mobile devices.
Threat Assessment
The threat posed by Dark Caracal is of medium risk but is a severe invasion of personal privacy due to the impact that they can have on the victim’s life. Dark Caracal is not as advanced as major nation states; however, its impact on the victims can last for a long time and include significant invasions of privacy, sharing of confidential information, and threats to personal safety.
Any type of organisation, business or individual operating in or related to the Middle East should be aware of Dark Caracal and its ability to conduct surveillance, especially if the individual has a high level of political or social visibility.
Defensive Considerations
The way to defend against Dark Caracal is to focus strongly on user education about potential risks to mobile devices due to lack of user knowledge:
– Restricting installing apps from unknown sources
– Implement mobile device management (MDM) and mobile threat defense (MTD) technology
– Educating users about phishing and social engineering
– Monitoring network traffic for suspicious patterns associated with mobile exfiltration of data.
Using only technical controls will not suffice without having human based security measures in place as well.
Conclusion
Dark Caracal shows just how much can be done with targeted surveillance of mobile devices without cyber hardware. The group has been able to effectively conduct espionage over extended periods by targeting specific individuals, exploiting trust, and maintaining a high degree of persistence.
Since mobile devices are becoming increasingly essential for day-to-day activities, the risk associated with Dark Caracal and other similar actors will continue to grow. Gaining knowledge about their tactics will provide insight into the evolution of cyber espionage as the line between digital intrusion and personal security continues to blur.
You can download and review the sheet for all the details!