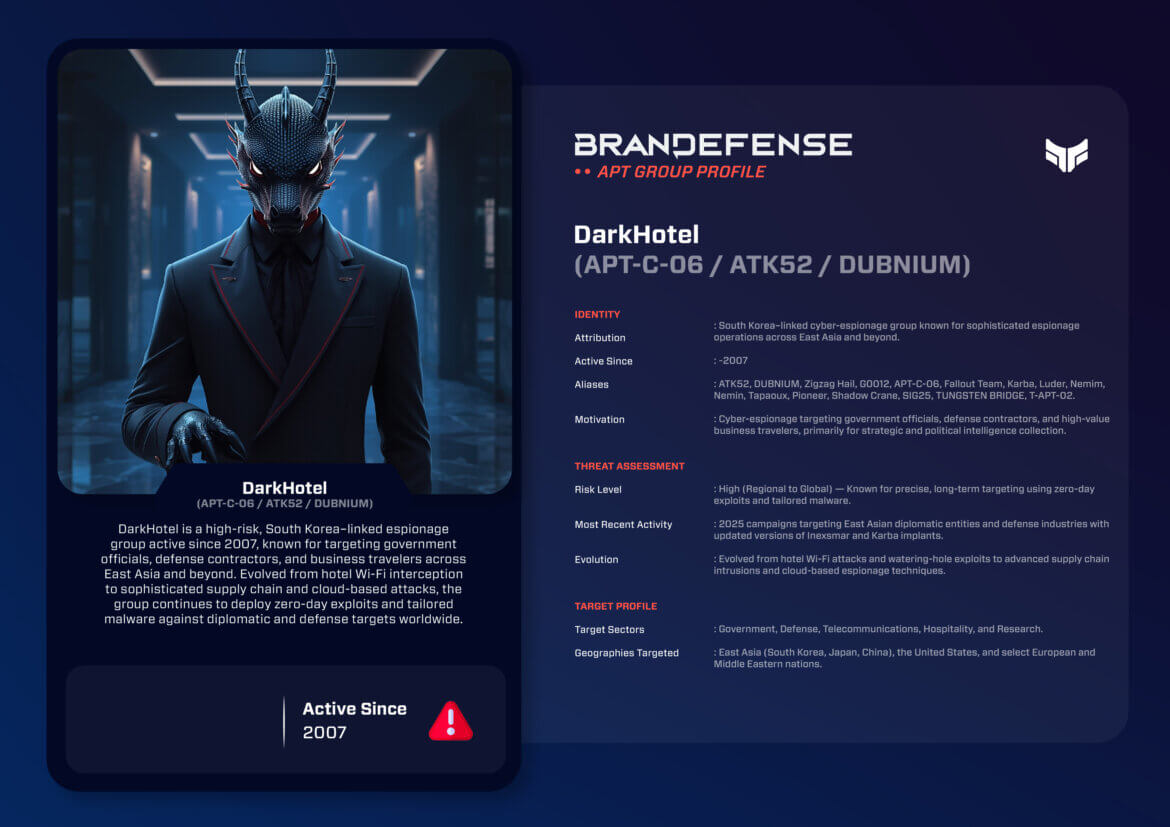
DarkHotel also known as APT-C-06, ATK52 and DUBNIUM, is one of the longest-standing and technically able cyber-espionage actors in the Asia-Pacific region and is believed to be associated with South Korea, and it possibly has been involved in intelligence operations dating back to at least 2007, focusing on espionage campaigns that target officials, diplomats, defense contractors, and business executives. Over time, DarkHotel’s tradecraft has transitioned from conducting Wi-Fi–based attacks in hotels to using more sophisticated supply chain compromises and cloud-based espionage operations.
DarkHotel gets its name from the initial modus operandi – compromising hotel networks in order to infect the devices of traveling executives and government officials who were connected to them. It should be stressed that its area of operation extends well beyond hotels, using zero-day exploits, credential theft, and high-quality custom phishing campaigns in order to infect targets worldwide. DarkHotel represents a new class of stealthy espionage actors, blending tasked-based social engineering with the current latest cyber intrusion techniques.
Identity and Motivation
Attribution assessments point to an actor based in or affiliated with South Korea, with strong indications of state sponsorship. The stated targeting priorities of DarkHotel suggest strategic motivations focused on regional security, defense cooperation, and economic policy.
Primary Motivations:
- Strategic Intelligence Gathering:Collection of data on defense initiatives, international diplomacy, and technology development.
- Corporate Espionage: Targeting global companies for intellectual property and R&D information.
- Regional Monitoring: Collection of intelligence based on communications related to East Asian geopolitics, to include information on Japan, China, and the Korean Peninsula.
DarkHotel’s sophistication of operations, selectivity in targets, and persistence demonstrate state intelligence capabilities rather than cyber criminals. Often, the victims of DarkHotel are intentionally selected based on position, influence, or access to sensitive information.
Tactics, Techniques, and Procedures (TTPs)
DarkHotel has proven consistent operational sophistication and flexibility. The group combines traditional phishing and credential theft tactics with advanced malware engineering and infrastructure management.
1. Initial Access
Early operations involved exploiting hotel Wi-Fi networks, utilized by traveling executives. Guests would receive legitimate looking software updates with DarkHotel’s implant. With increased defenses, this group transitioned to spearphishing, watering-hole attacks against policy and technology websites, and supply chain attacks. They also utilize publicly facing system vulnerabilities including VPNs and email servers.
2. Persistence and Privilege Escalation
Persistence mechanisms include DLL hijacking, scheduled tasks, and editing the registry. DarkHotel utilizes valid digital certificates to sign malware, providing legitimacy to try to evade detection by antivirus. In cases more recently, persistence has even moved to the cloud through compromised administrative credentials and OAuth tokens.
3. Command and Control (C2)
The group will utilize encrypted HTTPS C2 channels, proxy relays, and domain shadowing to inhibit detection of their communications. They will utilize the compromised servers and frequently rotate domain names to provide resiliency. Analysts have observed the group shifting towards a cloud-based command infrastructure in 2023.
4. Malware Arsenal
The malware family of DarkHotel can be characterized as modular and flexible:
– Inexsmar: A backdoor that can be used for espionage and lateral movement.
– Karba: A stealthy implant that can be used for data exfiltration and reconnaissance.
– Tapaoux: A downloader responsible for payload delivery to support attacks.
– Nemim/Nemin: Used for credential harvesting and persistence.
– Pioneer & Luder: Espionage tools to steal documents or log keystrokes.
These malware families are often deployed in customized builds that are configured specifically for the targets they are going after, demonstrating the invested effort DarkHotel has for precision operations.
5. Exfiltration and Evasion
Threat actors exfiltrate data over HTTPS or through encrypted archives of stolen information, and they often spread information in legitimate traffic. They also engage in steganography (hiding data in image files), code obfuscation, and use multi-stage loaders to evade analysis.Identity and Motivation
Attribution assessments point to an actor based in or affiliated with South Korea, with strong indications of state sponsorship. The stated targeting priorities of DarkHotel suggest strategic motivations focused on regional security, defense cooperation, and economic policy.
Primary Motivations:
- Strategic Intelligence Gathering:Collection of data on defense initiatives, international diplomacy, and technology development.
- Corporate Espionage: Targeting global companies for intellectual property and R&D information.
- Regional Monitoring: Collection of intelligence based on communications related to East Asian geopolitics, to include information on Japan, China, and the Korean Peninsula.
DarkHotel’s sophistication of operations, selectivity in targets, and persistence demonstrate state intelligence capabilities rather than cyber criminals. Often, the victims of DarkHotel are intentionally selected based on position, influence, or access to sensitive information.
Tactics, Techniques, and Procedures (TTPs)
DarkHotel has proven consistent operational sophistication and flexibility. The group combines traditional phishing and credential theft tactics with advanced malware engineering and infrastructure management.
1. Initial Access
Early operations involved exploiting hotel Wi-Fi networks, utilized by traveling executives. Guests would receive legitimate looking software updates with DarkHotel’s implant. With increased defenses, this group transitioned to spearphishing, watering-hole attacks against policy and technology websites, and supply chain attacks. They also utilize publicly facing system vulnerabilities including VPNs and email servers.
2. Persistence and Privilege Escalation
Persistence mechanisms include DLL hijacking, scheduled tasks, and editing the registry. DarkHotel utilizes valid digital certificates to sign malware, providing legitimacy to try to evade detection by antivirus. In cases more recently, persistence has even moved to the cloud through compromised administrative credentials and OAuth tokens.
3. Command and Control (C2)
The group will utilize encrypted HTTPS C2 channels, proxy relays, and domain shadowing to inhibit detection of their communications. They will utilize the compromised servers and frequently rotate domain names to provide resiliency. Analysts have observed the group shifting towards a cloud-based command infrastructure in 2023.
4. Malware Arsenal
The malware family of DarkHotel can be characterized as modular and flexible:
– Inexsmar: A backdoor that can be used for espionage and lateral movement.
– Karba: A stealthy implant that can be used for data exfiltration and reconnaissance.
– Tapaoux: A downloader responsible for payload delivery to support attacks.
– Nemim/Nemin: Used for credential harvesting and persistence.
– Pioneer & Luder: Espionage tools to steal documents or log keystrokes.
These malware families are often deployed in customized builds that are configured specifically for the targets they are going after, demonstrating the invested effort DarkHotel has for precision operations.
5. Exfiltration and Evasion
Threat actors exfiltrate data over HTTPS or through encrypted archives of stolen information, and they often spread information in legitimate traffic. They also engage in steganography (hiding data in image files), code obfuscation, and use multi-stage loaders to evade analysis.

Notable Operations
DarkHotel’s operations have been documented over approximately 20 years and exhibit incremental sophistication and alignment to strategy.
- 2014 – Hotel Wi-Fi Campaign: It became known as a threat actor after compromising hotel networks in Asia. Executives and civil servants were infected with malware as they connected to hotel Wi-Fi and downloaded a compromised download of the software. This operation demonstrated DarkHotel’s ability to weaponize legitimate infrastructure.
- 2017 – Defense Industry Intrusions: Performed spearphishing and water-hole attacks against Japanese and South Korean defense contractors using zero-day exploits and Inexsmar implants.
- 2020 – Diplomatic Espionage: Targeted ministries of Foreign Affairs and ministries of trade though East Asia delivering Karba malware through phishing campaigns disguised as policy briefs.
- 2023 – Supply Chain Compromise: Infiltrated a regional IT service provider inserting malware into software updates that were to be distributed to defense industry clients.
- 2025 – Cloud Exploitation Campaign: Deployed additional variants of Inexsmar and Karba malware to compromise Microsoft 365 environments, targeting diplomatic communications and research & development documentation.
These operations characterize an entity that evolved from opportunistic attacks in corporate environments to coordinated and intelligence driven espionage attacks.
Evolution and Tradecraft
DarkHotel has displayed exceptional longevity, consistently adapting in response to global defensive adaptations. Its previous reliance on hotel networks has transitioned into multi-vector intrusions that incorporate targeting of supply chains, identity compromise, and cloud exploitation.
Key Evolutionary Trends:
- From Physical to Cloud Intrusions: ransitioning from physical capabilities exploiting hotel networks to virtually compromising cloud identities.
- Adoption of Zero-Days: Actively employs previously unknown vulnerabilities in the Internet Explorer and Microsoft Office applications as part of their capabiliy set.
- Operational Segmentation: Segmentation of operations that differentiate by geographic area and operational objective from separate infrastructure to lower attribution risk.
- Custom Tooling: Uses custom tailored malware samples for each new victim, with built-in obfuscation for improved stealth and detection evasion.
These are features of an experienced, financially-supported espionage system with defined objectives.
Strategic Impact and Defensive Takeaways
DarkHotel’s activities underline the shifting nature of cyber-espionage in the Indo-Pacific region, and its activities offer insight into how mid-sized states employ cyber capabilities for strategic influence and intelligence gathering.
Strategic Implications:
- Intelligence Leverage: Gaining access to diplomatic and defense data provides information that supports national strategic planning.
- Regional Power Projection: Demonstrates the cyber capabilities of, for example, South Korea or entities aligned with South Korea within the region.
- Threat to Global Business Travelers: There remains an ongoing threat of the targeting of executives (and potentially others) acting as diplomats of business or of the government in East Asia.
Defensive Recommendations:
- Secure Remote Access: Implement appropriate VPN configurations, require two-factor authentication and monitior for identification anomalies.
- Patch Management: Maintain patches for browsers, Office applications and VPN gateways prioritizing these.
- Threat Hunting: Search for indicitive markers of Inexsmar, Karba or Tapaoux malware variants.
- Network Segmentation: Should also limit maximized privileges to a small group and segregate sensitive systems from public access.
- User Awareness: Should train travel and members of executive team of phishing and wifi system risks.
Conclusion
The DarkHotel campaign illustrates the adaptability and survivability of cyber-espionage in the modern world. Its development from compromising hotel-based Wi-Fi networks to running global campaigns in cloud-based environments illustrates a continual evolution of tactics, infrastructure and strategic intent. The group’s selective targeting and sophisticated operations enhance the threat it poses to the Indo-Pacific region of the cyber threat environment.
As of 2025, DarkHotel operates quietly but with considerable power, combining decades of experience and evolving technical capabilities to source intelligence around political, military and economic issues. Its continued existence highlights how advanced espionage groups will evolve in order to conduct their activities merging human intelligence concerns with technical rigor and stay ahead of defenders in the global cyber environment.
You can download and review the sheet for all the details!