Executive Summary
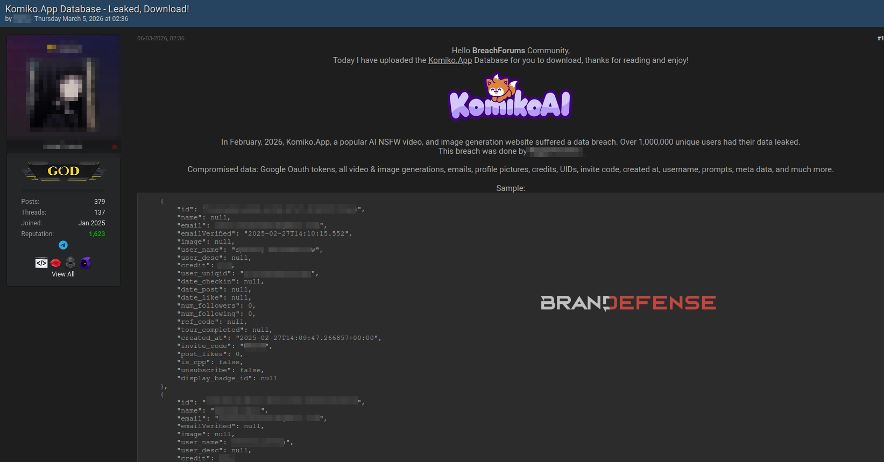
In February 2026, Brandefense threat analysts identified a high-severity post on an underground forum in which an unidentified threat actor claimed to have exfiltrated the complete database of a popular AI-powered application. The actor alleged that the breach affected more than 1,000,000 registered users and offered the full dataset for free download, with a credit requirement attached — a distribution model commonly used to build reputation within threat actor communities.
The leaked data, examined by our team, includes Google OAuth tokens, active session tokens, user-generated content, personal identifiers, subscription records, and account credentials. The exposure of OAuth tokens in particular presents a severe escalation risk, as these tokens can be used to access third-party services linked to the compromised accounts — extending the blast radius far beyond the breached platform itself.
| ⚠ CRITICAL: Active Google OAuth and session tokens were found in the dataset. If valid, these tokens allow attackers to authenticate as victims without needing a password. |
What Was in the Leaked Database?
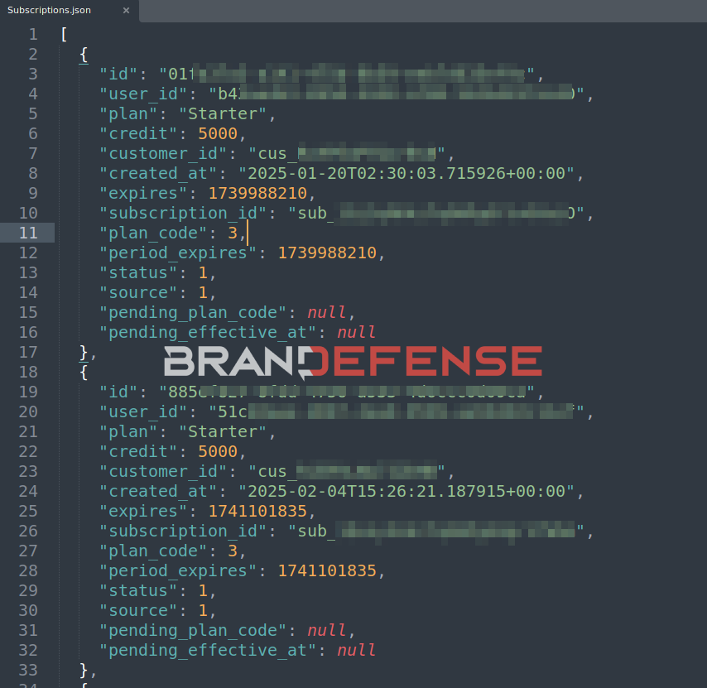
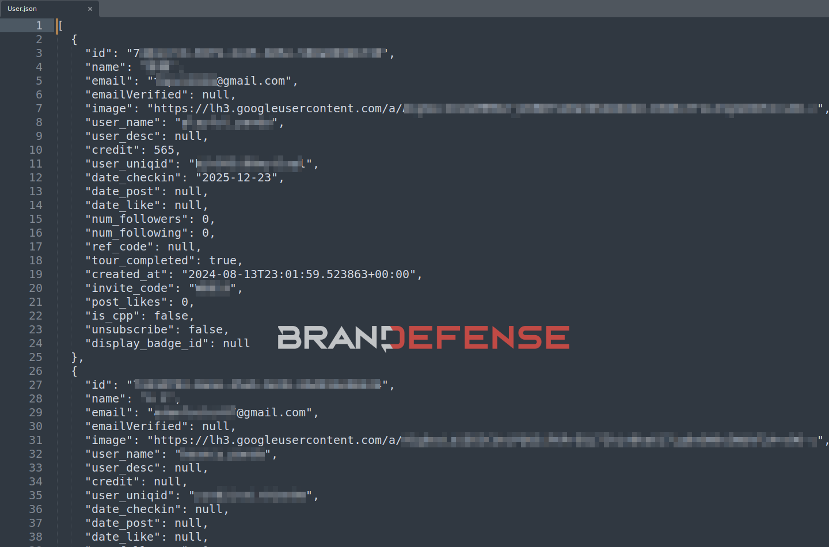
Our analysts reviewed a sample of the alleged dataset. The breach appears to encompass multiple database tables exported in JSON format — a structure consistent with a direct database dump rather than a scraping or API abuse incident. Below is a breakdown of each exposed data category:
| Data Category | Fields Exposed | Risk Level |
| Account / OAuth Records | Google OAuth tokens, refresh tokens, access tokens, provider account IDs, token expiry timestamps | CRITICAL |
| Session Records | Session tokens, user IDs, expiry timestamps | CRITICAL |
| User Records | Full name, email address, username, profile picture URL (Google CDN), credit balance, invite codes, creation date, user unique IDs | HIGH |
| Subscription Records | Stripe customer IDs, subscription IDs, plan names, plan codes, credit allocations, expiry dates, billing source | HIGH |
| Verification Tokens | Email verification tokens, associated email addresses, expiry timestamps | HIGH |
| Messages / Content Records | User-generated content IDs, content type, host content references, aggregate IDs, creation timestamps | MEDIUM |
| User Badges | Badge assignments, user identifiers | MEDIUM |
| User Blocks / Shares | Block relationships, shared content records | LOW |
| Push Tokens | Device push notification tokens, user linkage | MEDIUM |

Technical Analysis: How the Breach Appears to Have Occurred
While the root cause has not been officially confirmed, the structure and completeness of the leaked dataset provides meaningful forensic clues. Based on our analysis:
Database Dump Indicators
The exported files follow a consistent, relational database structure. Each table is exported as a standalone JSON array — a pattern that aligns with direct database access via an ORM (Object Relational Mapper) export, a compromised backup file, or unauthorized administrative access. The breadth of coverage across all major tables rules out a targeted API abuse scenario.
OAuth Token Exposure
The Account.json file contains what appear to be live Google OAuth access tokens and refresh tokens. OAuth tokens are temporary credentials that allow applications to act on behalf of a user. A refresh token, if not revoked, can be used indefinitely to generate new access tokens — meaning attackers may retain persistent access to linked Google accounts even after the compromised platform rotates its own credentials.
⚠ IMPORTANT: Refresh tokens do not expire unless explicitly revoked by the user or Google. Any user who authenticated via Google OAuth on this platform should immediately revoke third-party access at myaccount.google.com/permissions.
Session Token Risk
Session.json contains active session tokens with future expiry timestamps (some extending to early 2026). Active session tokens can be used directly to hijack authenticated sessions without requiring any credentials — a technique known as session hijacking or cookie theft.
Stripe Customer ID Exposure
The Subscriptions.json file exposes Stripe customer IDs. While Stripe customer IDs alone do not grant access to payment card data, they can be used in combination with a compromised Stripe secret key to retrieve billing information or manipulate subscription states. Organizations using Stripe should rotate API keys immediately if this data is confirmed.
Impact Assessment
Organizational Impact
The alleged compromise represents a significant reputational and regulatory risk for the affected platform. Under GDPR, CCPA, and other applicable data protection frameworks, the exposure of personal data — including email addresses, profile pictures, and unique identifiers — triggers mandatory breach notification obligations. Failure to comply with notification timelines can result in substantial regulatory fines.
The exposure of user-generated content, including AI prompts and generated media, raises additional privacy concerns. These records may reveal sensitive personal interests, business use cases, or private creative work, each carrying its own reputational risk for users if publicly disclosed.
End-User Impact
- Account Takeover: Active session tokens and OAuth refresh tokens can be used to gain immediate, authenticated access to victim accounts.
- Credential Stuffing: Exposed email addresses will be incorporated into credential stuffing lists and tested against other platforms where victims may reuse passwords.
- Phishing & Spear Phishing: Full name, email, and profile data enable highly personalized phishing campaigns with elevated success rates.
- Identity Theft: Combination of email, name, profile image, and account history provides sufficient data for synthetic identity fraud.
- Financial Risk: Exposure of Stripe customer IDs, credit balances, and subscription details may enable subscription fraud or targeted billing manipulation.
- Cross-Platform Risk: Google OAuth tokens may expose other services connected to the same Google account — including Google Drive, Gmail, Google Workspace, and third-party SaaS tools.
| Attack Vector | Likelihood | Potential Impact |
| OAuth Token Abuse / Account Takeover | Critical | Immediate account compromise across linked services |
| Session Hijacking | High | Direct access to active authenticated sessions |
| Targeted Phishing Campaign | Critical | Elevated open & click rates due to PII richness |
| Credential Stuffing Against Other Platforms | High | Password reuse exploitation across unrelated services |
What Has Komiko Confirmed in Its Official Statement?
- They acknowledged receiving a credible threat that an external attacker had accessed their database.
- They confirmed that user IDs, email addresses, and potentially user content had been compromised.
- They announced that they do not store passwords or payment card data.
- They stated that they worked with security experts and reported the incident to law enforcement.
Areas they said they are still investigating include:
- The full scope of the accessed data,
- How the attacker gained access,
- Whether user-generated AI content (AI creations) was included.
Recommended Mitigations
For Affected Users — Immediate Actions
| If you have an account on the affected platform, take the following steps immediately: |
- Revoke Google OAuth access: Visit myaccount.google.com/permissions and remove the application’s access to your Google account.
- Change your password on the affected platform and on any other service where you use the same password.
- Enable Multi-Factor Authentication (MFA) on your Google account and any linked services immediately.
- Review your Google account’s recent activity (myaccount.google.com/security) for any unauthorized sign-ins.
- Be vigilant for phishing emails targeting your registered email address — attackers now have your name and account history.
- Monitor your linked payment methods for suspicious charges, particularly if you had an active subscription.
- Check if your email appears in additional breaches.
For the Affected Organization — Response Checklist
- Immediately rotate all Google OAuth client secrets and force-revoke all existing OAuth tokens.
- Invalidate all active session tokens and require all users to re-authenticate.
- Rotate Stripe API keys and audit all recent API calls for suspicious activity.
- Engage a forensic response team to determine the root cause, timeline, and full scope of the compromise.
- Conduct an emergency security audit of database access controls, backup storage, and administrative account privileges.
- Implement IP allowlisting and privileged access management (PAM) for all database and cloud infrastructure access.
Strategic Recommendations
- Implement encryption at rest for all OAuth tokens, session tokens, and sensitive credentials stored in the database.
- Adopt a token rotation policy: short-lived access tokens (1 hour) with server-side refresh token validation.
- Deploy a Web Application Firewall (WAF) and database activity monitoring (DAM) to detect anomalous bulk export patterns.
- Conduct regular penetration testing and red team exercises targeting authentication and data access flows.
- Implement Data Loss Prevention (DLP) controls to alert on bulk data exfiltration events.
How Brandefense Detected This Threat
This breach was identified through Brandefense’s continuous dark web and underground forum monitoring infrastructure. Our platform maintains 24/7 automated surveillance across thousands of threat actor forums, leak sites, Telegram channels, and private marketplaces — enabling our analysts to surface high-severity incidents within hours of initial posting.
Upon detection, our Threat Intelligence team validated the claims by analyzing the provided sample data, cross-referencing the exposed fields against known database structures, and assessing the technical credibility of the actor’s claims.
| Detection Capability | Value Delivered |
| Underground Forum Monitoring | Breach post identified within hours of initial publication |
| Dark Web Data Validation | Sample analysis confirmed data authenticity and scope |
| Actor Profiling | Distribution model (free share + credit requirement) mapped to known reputation-building behavior |
| Impact Scoring | High-severity classification triggered based on OAuth token exposure and user volume |