Introduction
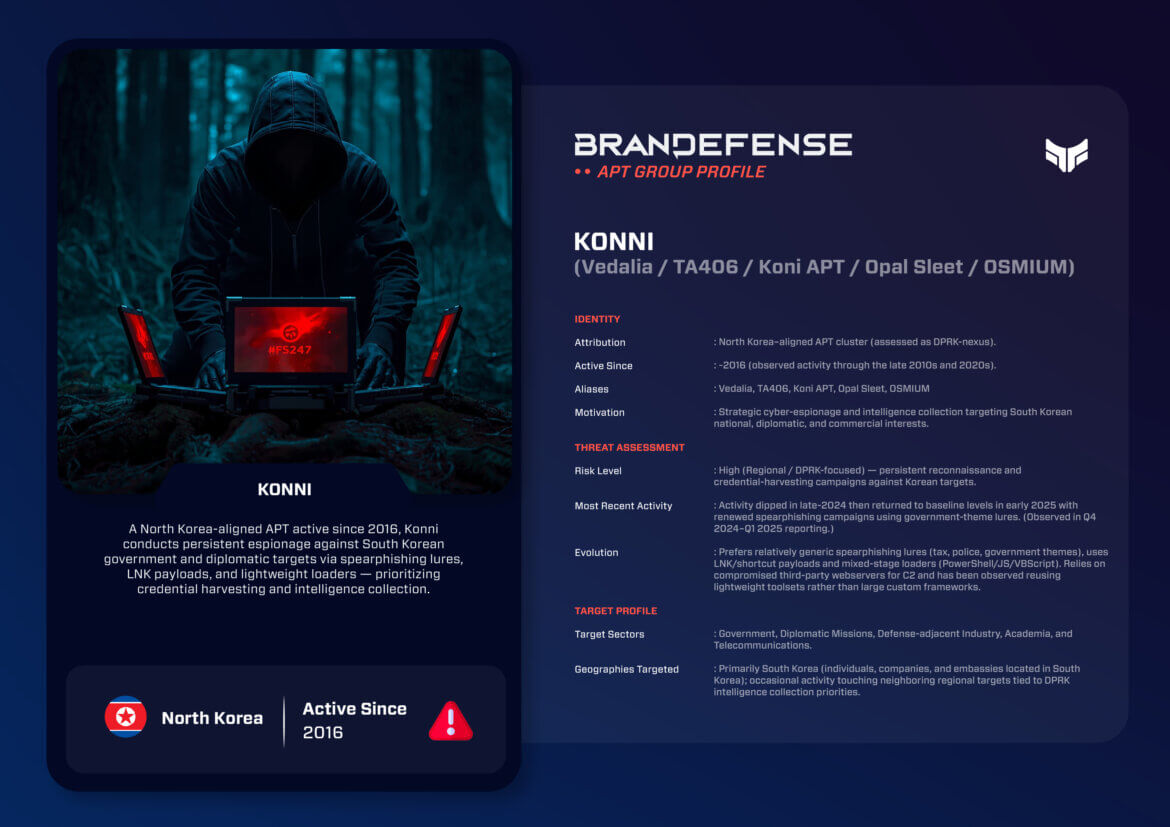
Konni, also referred to as Vedalia, TA406, Opal Sleet, and OSMIUM, is one of North Korea’s most consistent and systematic cyber-espionage groups. Active since at least 2016, the group has primarily focused on intelligence gathering against South Korean, Japanese, Russian, and broader targets in the international diplomatic space. Unlike other DPRK-linked groups which have a stronger financial motivation (e.g., Lazarus or Andariel), Konni is focused on discrete intelligence collection over the long-term, which advances one of Pyongyang’s geopolitical objectives.
The operational pattern of Konni aligns very closely with the mission profile of North Korea’s Reconnaissance General Bureau (RGB) – the state’s leading intelligence service responsible for carrying out many of North Korea’s global cyber-operations. Across almost a decade, Konni has maintained a steady tempo and has iterated its techniques in order to achieve balance in operational deception and persistence to acquire useful political, military and policy-related intelligence.
Identity and Motivation
Konni’s primary mission is to conduct strategic intelligence. It collects sensitive intelligence regarding inter-Korean relations, defense policy, and diplomatic issues to advance North Korea’s national interests. The group conducts activity patterns alongside geopolitical events, like sanctions deals or joint military exercises by South Korea and the United States.
Its motivations consist of:
1. Political and Diplomatic Intelligence: Obtaining intelligence on embassies, ministries, and think tanks involved with Korean Peninsula policy.
2. Military and Security Awareness: Obtaining defense communications and research data for military-related information.
3. Strategic Counterintelligence: Monitoring activities of [organizations] monitoring for DPRK sanctions or nuclear developments.
This focus represents how Pyongyang enacts its wider strategy – to use cyber capabilities in order to counteract ability to collect traditional HUMINT, while still gaining influence in the region.
Tactics, Techniques, and Procedures (TTPs)
Konni demonstrates a reasonable level of technical sophistication that is effective. Their success is heavily attributable to well-executed social engineering and stealthy malware designed to evade detection at the same time remaining persistent.
1. Initial Access
Spearphishing, or targeted phishing, is a key initial access vector for Konni. The group sends emails representing South Korean or international governmental, defense, or journalistic organizations. The attachments consist mostly of weaponized Microsoft Office or RTF files that rely upon embedded macros or scripts. Recently, the Konni group increasingly utilized LNK (shortcut) files and manipulation of archiving to bypass email filtering mechanisms.
2. Execution and Persistence
Once initial access has been achieved, Konni will utilize lightweight loaders developed in PowerShell, VBScript or JavaScript. These loaders then retrieve additional payloads, which are typically a variation of KONNI RAT or CARROTBAT malware. To maintain persistence, KONNI malware utilizes scheduled tasks, registry changes, and abuse of legitimate Windows utilities.
3. Command and Control (C2)
Konni’s infrastructure is straightforward yet resilient. They commonly rely on legitimate hosting services and compromised web servers for C2 traffic. Communication typically occurs using HTTP/S or FTP and blends in with normal traffic. The use of cloud infrastructure has also increasingly appeared in campaigns since 2023.
4. Malware Arsenal
Konni has a small but stable malware ecosystem:
– KONNI RAT: The signature malware of the group, it allows command executions, captures screenshots, and exfiltrates files.
– CARROTBAT-ered: Used to deliver secondary payloads and establish persistence.
– BabyShark: A modular backdoor designed for espionage and reconnaissance.
– Poweshell-based loaders: Lightweight scripts, used for stealthy delivery and lateral movement.
The tools that Konni uses are not overly sophisticated but exhibit careful design to avoid detection and allow long-term infiltration.
5. Exfiltration and Data Handling
The group exfiltrates sensitive data (user credentials, internal documents, and system data) over encrypted HTTP/S channels. Analysts believe that the exfiltrated intelligence is being used to assist diplomatic negotiations and strategic planning for North Korea.

Notable Operations
Konni’s campaigns highlight its tenacity and adaptability as part of cyber-espionage in the DPRK.
- 2017 – KONNI RAT Campaign: In its early campaigns, Konni targeted South Korean government personnel and used spearphishing campaigns with fake diplomatic correspondence to deliver KONNI RAT malware.
- 2020 – BabyShark Variant Deployment: Weaponized and updated malware was used to carry out a campaign targeting policy institutes and defense research centers in Seoul.
- 2022 – Credential Harvesting Operation: Beginning in February 2022, the attackers initiated a wave of phishing attacks that included malicious LNK files that referenced talks for future international cooperation between North and South Korea to capture user credentials.
- 2024 – Opal Sleet Overlaps: Indicators or artifact overlap suggest some degree of interoperability with other DPRK groups or actors such as Kimsuky targeting South Korean defense contractors.
- 2025 – Diplomatic Espionage Campaign: Renewed phishing campaigns distributing fake South Korean ministry documents, heavily improved and weaponized PowerShell loaders, new modular RATs, indicate continued refinement.
The campaigns illustrate Konni’s patience in execution as well as its ability to continue relevance in the changing threat environment in the region.
Evolution and Group Dynamics
Konni has transitioned from a relatively isolated espionage cell to something deeper in North Korea’s wider cyber ecosystem. Analysts note that the group’s TTPs have an increasing overlap with Kimsuky (Velvet Chollima) and Andariel (Silent Chollima), suggesting shared resources or a centralized direction from the RGB.
Trends seen in the evolution of Konni include:
– Infrastructure Rotation: Regularly changing C2 domains and hosting servers to reduce attribution.
– Lightweight Malware Design: Smaller payload and multi-stage loading processes, to maintain stealth.
– Coordination: Possible collusion with other DPRK threat groups to share information and specialization of tasks.
– Attention to Geopolitical Timing: Operations often occur in relation to key summits, sanctions, or international reports that impact North Korea.
Konni’s restrained and espionage-based approach is a clear break from financially motivated groups such as Lazarus. Rather, it demonstrates North Korea’s intelligence-driven cyber methodology quiet, systematic, and persistent.
Strategic Impact
Konni’s activity reaffirms North Korea’s long-standing commitment to using cyber espionage as a core intelligence-gathering method. The group aids in Pyongyang’s understanding of its regional political and military environment to facilitate informed strategic planning and diplomatic posturing.
Viewing Konni from a wider lens, it exemplifies the increased professionalism of the DPRK cyber units. By focusing on South Korean policy and defense, the work Konni is doing meets North Korea’s need to anticipate actions in response to its nuclear and missile activity. It is likely that the intelligence provides both guidance for political negotiations and propaganda for domestic consumption and guidance for regime decisions.
While the technical methods used by the group are not complicated, the ability of the group to consistently operate for nearly a decade demonstrates the requisite operational discipline to achieve objectives. It also illustrates, like other DPRK cyber operations, the group’s ability to exist in the public eye yet remain relevant.
Defensive Takeaways
Proactive steps are needed to mitigate the risk of KONNI attacks through phishing awareness, network monitoring, and behavioral detection:
1. Email Security: Utilize advanced filtering and sandboxing attachments for detection of malicious documents and LNK payloads.
2. Integrate threat intelligence: Monitor IOCs relevant to the KONNI RAT, CARROTBAT, and connected domains.
3. Behavioral Detection: Focus on detection of abnormal PowerShell or scripts, rather than relying solely on signature isolation.
4. Credentials: Implement MFA and monitor for abnormal login attempts.
5. Joint Responsibility: Encourage intelligence sharing amongst South Korean, Japanese, and allied computer incident response teams to monitor DPRK activity.
Conclusion
Konni exemplifies the persistent, disciplined component of North Korea’s cyber espionage apparatus. While it lacks the financial motivations of Lazarus Group or destructive potential of Andariel, Konni’s persistent, low-profile tack has provided an important operational contribution to the greater benefit of Pyongyang’s worldwide intelligence goals. Its spearphishing campaigns and modular Remote Access Trojans (RATs) continue to provide collections in support of the DPRK’s political and military objectives.
In 2025, Konni is still active, responsive, and strategically aligned to the state’s long-term priorities. Its sustained utilization showcases a matured, North Korean cyber operation prioritizing information dominance and operational continuity rather than theatrics. For the defenders, remaining vigilant to this insidious but persistent threat is critical to supporting regional resiliency to a possible cybersecurity incident.
You can download and review the sheet for all the details!