Why this matters?
A new ransomware group tracked as “Reynolds” emerged in February 2026 and is reported to use Bring Your Own Vulnerable Driver (BYOVD) technique to disable security controls before encryption, thereby significantly increasing its chances of success even in well-equipped environments.
What to expect if this hits you?
- Security tooling disruption (EDR/AV termination) prior to encryption via a vulnerable Kernel driver.
- Encryption + pressure tactics (leak-site negotiation), with a clear victim communication path via Tox/onion
- Operational impact: reduced visibility at the worst possible time (pre-encryption window).
What we know about Reynolds?
Observed targeting:
- There is currently one known victim of the Reynolds Ransomware Group.
- Victim: falconmgt.com
- Victim’s Sector: Business Services
- Discovered on 2026-02-11
- Estimated attack date of 2025-11-13
- The Reynolds Ransomware Group publishes its victims via a Tor onion address.
Known highlighted tactics:
- BYOVD (Build Your Own Vulnerable Driver) uses the NSecKrnl driver to terminate security products/evade detection.
- Our findings attribute this to CVE-2025-68947 in the NSecKrnl driver.
- Encrypted files with the “.locked” extension have been observed.
- Observed techniques include the use of the GotoHTTP remote access tool.
Technical Summary
Execution Chain:
- Privilege & driver load: activity consistent with enabling/loading a Kernel driver (requires SeLoadDriverPrivilege).
- Driver-based tampering (BYOVD): vulnerable driver used to terminate/neutralize security processes.
- Encryption + artifacts: files renamed with an added extension and ransom note dropped.
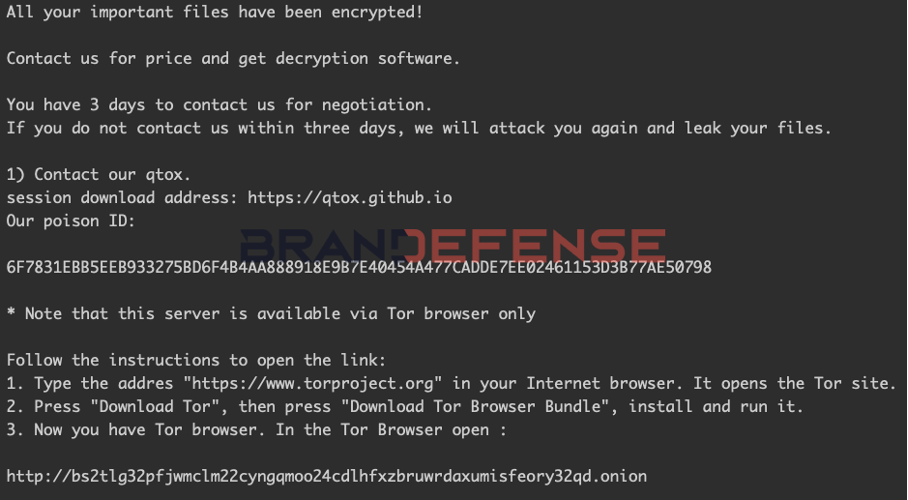
- Victim communications: ransom note points to a Tor onion site and a Tox ID.
IR Priorities (what to do first?)
- Containment: isolate affected hosts quickly (driver-based EDR tampering may reduce telemetry).
- Driver abuse hunting: look for new/unknown driver installs, service creation and suspicious “
ImagePath” pointing into user-writable locations: - Validate backups & recovery: expect “fast-impact” behavior once security is degraded.
What CISOs should ask their teams?
- Are we enforcing driver block controls (e.g., WDAC / vulnerable driver block lists / HVCI where feasible) ?
- Are we receiving alerts regarding service creation for drivers and registry changes under
SYSTEM\ControlSet\Services\* ? - If EDER fails, do we have “emergency” visibility (off-band logging, network telemetry, immutable backups) ?

Technical Indicators (Hashes/IOCs/Detection References)
Sample Hashes
Primary Sample:
| MD5 | f7d7377b17fc4cdcbb783cc090d6e983 |
| SHA1 | 03fe81be332f81a0fc590961109e7e2e8c9ad4fa |
| SHA256 | 5100e19d229de04b5028cc0c00bfa9f5904b0a5f0e1ae49828580d0973548ac5 |
Dropped Ransom Note:
| File Path Observed | C:\Recovery\WindowsRE\___RestoreYourFiles___.txt |
| MD5 | d04b68674d2cebb154a0fca7013260a1 |
| SHA256 | f7a4cfdd1c855a9f399661cfae39ca0c9cf23ae66a97e14a2063f61a2c3a0806 |
File / Registry IOCs
Driver-related
- Driver file path observed in registry:
\??\C:\ProgramData\402.sys Service key: \REGISTRY\MACHINE\SYSTEM\CONTROLSET001\SERVICES\NSecKrnl\ImagePath→\??\C:\ProgramData\402.sys
Ransom note filename:
___RestoreYourFiles___.txt
Processes
C:\Users\Admin\AppData\Local\Temp\6bd8a0291b268d32422139387864f15924e1db05dbef8cc75a6677f8263fa11d.exe PID:3348
“C:\Users\Admin\AppData\Local\Temp\6bd8a0291b268d32422139387864f15924e1db05dbef8cc75a6677f8263fa11d.exe”
| Sets service image path in registry |
| Drops startup file |
| Suspicious behavior: EnumeratesProcesses |
| Suspicious behavior: LoadsDriver |
| Suspicious use of AdjustPrivilegeToken |
————
C:\Windows\system32\svchost.exe PID:3612
C:\Windows\system32\svchost.exe -k UnistackSvcGroup -s CDPUserSvc
C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe PID:2592
“C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe” -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca
———-
Downloads
C:\Recovery\WindowsRE\___RestoreYourFiles___.txt
| Filesize | 812B |
| MD5 | 554da156863a1e3eb6c4d511e6bb8844 |
| SHA1 | 1f25bc43a002700b2183b7cf06d3ea8f4f710193 |
| SHA256 | c3bca7c9e5b0d3d9dadcae78ca79ee687c8f93d3e59500e86f03685d9ee4db70 |
| SHA512 | 952011d94feb09d3ae5c7bd876acc50f93d23090c4e6a2c982872a5e95c7d83 |
C:\Users\Admin\AppData\Local\Packages\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\TempState\StartUnifiedTileModelCache.dat
| Filesize | 15KB |
| MD5 | ca9815189bc1630cd67d7d825bb4011c |
| SHA1 | 53f46cd7c4f0520b0a816406a5e1bd8208e08501 |
| SHA256 | fe841fe36933b3fc54c75a7ee1065af796a927f97e30c5c343203432cd4bf953 |
| SHA512 | 76616328285fc1c26d4a744dcbf9b3b020792442112d7cebfe7560ca59cc517dc91d2ff5fda8bed70207f94b7eb4bd319ce72f7dba05f77394a6e3dd2295c3d7 |
Ransom Note
Yara Rule
/*
Brandefense
Reynolds (Feb 2026) - Ransom note + ransomware/BYOVD
*/
import "pe"
rule RANSOM_Reynolds_RansomNote___RestoreYourFiles___Feb2026
{
meta:
author = "Brandefense"
description = "Detects Reynolds ransom note (___RestoreYourFiles___.txt) with qTox poison ID and onion portal"
date = "2026-02-18"
strings:
$s1 = "All your important files have been encrypted!" ascii nocase
$s2 = "You have 3 days to contact us for negotiation." ascii nocase
$s3 = "Contact our qtox." ascii nocase
$s4 = "Our poison ID:" ascii nocase
$s5 = "Note that this server is available via Tor browser only" ascii nocase
$tox = "6F7831EBB5EEB933275BD6F4B4AA888918E9B7E40454A477CADDE7EE02461153D3B77AE50798" ascii
$onion = "bs2tlg32pfjwmclm22cyngqmoo24cdlhfxzbruwrdaxumisfeory32qd.onion" ascii
$fname = "___RestoreYourFiles___" ascii
condition:
filesize < 50KB and
$tox and $onion and
2 of ($s1,$s2,$s3,$s4,$s5,$fname)
}
rule Reynolds_Ransomware_BYOVD_NSecKrnl_Feb2026
{
meta:
author = "Brandefense"
description = "Detection Rule for Reynolds ransomware family with bundled BYOVD/NSecKrnl activity and ransom-note artifacts"
date = "2026-02-18"
strings:
/* BYOVD / driver-load related artifacts (observed behavior) */
$reg_service = "\\REGISTRY\\MACHINE\\SYSTEM\\ControlSet001\\Services\\NSecKrnl\\ImagePath" ascii wide
$svc_name = "NSecKrnl" ascii wide
$driver_path = "\\??\\C:\\ProgramData\\402.sys" ascii wide
$priv = "SeLoadDriverPrivilege" ascii wide
/* Ransom-note payload artifacts (often embedded for drop) */
$note_name = "___RestoreYourFiles___" ascii wide
$note_line = "All your important files have been encrypted!" ascii nocase
$tox = "6F7831EBB5EEB933275BD6F4B4AA888918E9B7E40454A477CADDE7EE02461153D3B77AE50798" ascii
$onion = "bs2tlg32pfjwmclm22cyngqmoo24cdlhfxzbruwrdaxumisfeory32qd.onion" ascii
condition:
uint16(0) == 0x5A4D and pe.is_pe and pe.is_64bit() and
(
/* strong BYOVD signal */
2 of ($reg_service,$svc_name,$driver_path,$priv)
) and
(
/* tie-back to Reynolds note/portal */
$note_name or $note_line or ($tox and $onion)
)
}