Introduction
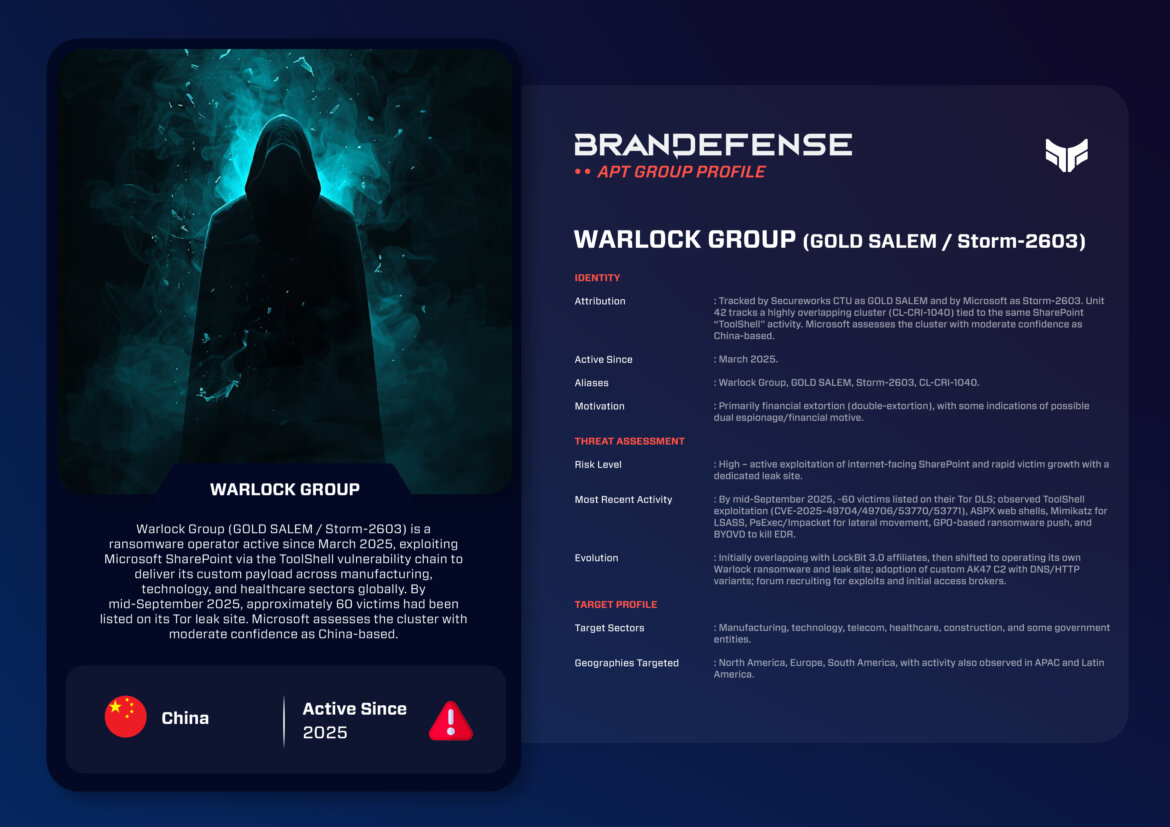
By 2025, the ecosystem of ransomware had become as fragmented, competitive, and dangerous as it’s ever been. Among the many emerging groups that year was Warlock Group, aka GOLD SALEM and tracked by Microsoft as Storm-2603, which gained notoriety quickly. In just a few months of operations, Warlock was exploiting zero-day vulnerabilities in Microsoft SharePoint; it had implemented custom Command-and-Control (C2) frameworks; and it had developed a leak site featuring dozens of global victims.
The rise of Warlock Group exemplifies two more substantial trends in today’s cyber threat landscape: (1) the mixing of tradecraft originating from nation-state groups with that of financially-motivated ransomware, and (2) the rapid weaponization of vulnerabilities in enterprise software.
Identity & Motivation
Warlock Group is tracked under these multiple, related aliases:
- GOLD SALEM
- Storm-2603
- CL-CRI-1040
Attribution remains contested. Microsoft assesses the cluster with moderate confidence to be based in China due to its clustered operational overlap with clusters associated previously with Chinese-based threat activity, while other vendors shy away from any attribution, citing competition, opportunism, etc. stressing that the group’s financial motivation – profit through ransomware extortion – could well mitigate any state sponsorship angle.
Regardless of its origins, the group’s objectives are straightforward: profit from intrusions utilizing double extortion tactics. They will encrypt victim’s environments while stealing sensitive data, which they will publish on their leak site if the ransom is not paid.
Tactics, Techniques, and Procedures (TTPs)
Initial Access: SharePoint “ToolShell” Exploitation
In March 2025, Warlock Group made headlines when it exploited a series of critical Microsoft SharePoint vulnerabilities collectively known as “ToolShell” (CVE-2025-49704, CVE-2025-49706, CVE-2025-53770, CVE-2025-53771).
- These vulnerabilities enabled adversaries to achieve remote code execution capabilities on exploited SharePoint servers.
- Once the adversary was in the environment, they established persistence and a mechanism for lateral movement, deploying ASPX web shells (for example, spinstall0.aspx).
This uncritical exploitation exemplifies an increased trend of adversaries rushing to weaponize recently disclosed vulnerabilities with widely deployed enterprise software.
Persistence & Command-and-Control
Warlock was utilizing custom and off-the-shelf tools:
- AK47 C2 Framework: A custom tool that operates over both the HTTP and DNS protocols, allowing for stealthy and covert command and control of compromised systems.
- Velociraptor & VS Code tunnels: These legitimate tools were abused for persistence and remote access.
The combination of custom tools and commoditized tools reveals the group’s adaptability and desire to make detection more complex.
Lateral Movement & Privilege Escalation
After establishing a foothold, Warlock used:
- Mimikatz to extract credentials from LSASS memory.
- PsExec and Impacket to move laterally across victim networks.
- BYOVD (Bring Your Own Vulnerable Driver) techniques to turn off endpoint detection and response (EDR) tools.
- Group Policy Objects (GPOs) to facilitate large-scale deployment of ransomware payloads.
This toolkit mirrors operations of established ransomware, demonstrating Warlock’s robust maturity.
Impact: Double Extortion Ransomware
Warlock’s operations end in the execution of its ransomware that encrypts victim systems and exfiltrates sensitive data at the same time. Victims are then publicly identified on the group’s dark web leak site, previously known as Data Leak 101, and pressure campaigns escalate if the ransom is not paid.

Target Profile
The Warlock group has exhibited broad target patterns that do not narrow in on a single sector. As of mid-September 2025, the group claimed just under 60 victims across diverse target sectors, to include:
- Manufacturing
- Telecommunications
- Technology
- Healthcare
- Construction
- Government agencies
Geographically, Warlock has not limited its operations to any of North America, Europe, and South America, but has also exhibited activity in the Asia-Pacific (APAC) and Latin American regions.
This targeting pattern is consistent with organized crime, financially motivated ransomware groups that are less concerned with target sector alignment and more concerned with opportunity.
Notable Operations
- March 2025 – Initial Emergence
Warlock was first detected exploiting SharePoint ToolShell vulnerabilities, rapidly establishing itself as an emerging threat actor with capability. - April–May 2025 – Leak Site Launch
Warlock established its own dedicated leak site on the dark web, following trends established by other ransomware groups, shortly after launching attacks. Its early victims were largely organizations in North America and Europe. - August 2025 – SharePoint Zero-Day Exploits
While leveraging a new set of SharePoint zero-days, Warlock deployed ransomware during other high-profile breaches. This demonstrated agility by taking advantage of newly available exploits. - September 2025 – Expanding Operations
The group confirmed by September that it had multiplied its victim count to roughly 60 victims worldwide, evidence of Warlock’s establishment as one of the more active emerging ransomware groups.
Evolution & Outlook
The evolution of Warlock Group is characterized by speed:
- Initially, the Warlock group began alongside LockBit 3.0 affiliates, but has more recently established itself as an independent operator.
- Recruitment efforts have been observed on underground forums where Warlock is seeking initial access brokers (IABs) and exploit developers to increase its operation.
- Warlock uses custom C2 (AK47) and it employs advanced post-exploitation techniques, which shows Warlock’s appearance of operational maturity which is not often evident of groups so new.
Looking ahead, a number of developments are anticipated:
- Continued Exploitation of Enterprise Software: Based on recent success within SharePoint, Warlock is expected to pivot relatively quickly to target other software vulnerabilities that carry a high value.
- Victim Expansion: It is probable that the group will expand to the critical infrastructure area which may help enhance ransom leverage as operational disruptions take hold.
- Possible State Nexus Debate: Due to operational similarities to other Chinese clusters debate will persist on whether or not Warlock is a State-nexus hybrid actor, or a financially motivated group.
Conclusion
The emergence of Warlock Group (GOLD SALEM / Storm-2603) in 2025 highlights how quickly new players in the ransomware economy can emerge and disrupt the cyber threat landscape. Through rapid weaponization of SharePoint vulnerabilities, using custom tooling like AK47 C2, and adopting aggressive double-extortion methodologies, Warlock has quickly established themselves as a high-risk potential actor with a global reach.
For defenders, key takeaways include:
- Prioritize patching of all Internet-facing applications, including SharePoint.
- Hardening Active Directory – especially against possible GPO and legitimate credential abuse.
- Reduce persistence indicators – especially unique ASPX files or DNS-based C2 activity.
- Plan for your double-extortion strategy so that you not only have backups in place, but also a strategy to respond when data is leaked.
The trajectory Warlock takes as they ramp their operations will challenge enterprises’ resilience against a new wave of ransomware groups; a group that mixes a state-like common tradecraft with relentless financial pressure to meet their own goals.
You can download and review the sheet for all the details!