Your password policy is strong. You enforce complexity requirements, rotation intervals, and lockout thresholds. Your users have been told (repeatedly) not to reuse passwords. None of this matters if someone is already selling your employees’ credentials on a dark web forum for $2 a pair.
Credential stuffing is not a hacking technique. It is a logistics operation. Attackers do not attempt to guess or crack passwords they purchase lists of real username-and-password combinations harvested from previous breaches, then automate the process of testing those combinations across hundreds of target services simultaneously. The only technical skill required is the ability to run a script. The only investment required is a dark web marketplace account.
In 2025, compromised credentials are the single most common initial access vector in confirmed data breaches responsible for 22% of all incidents globally. Credential theft surged 160% in the first half of the year alone. And in June 2025, researchers discovered a single aggregated dataset containing 16 billion login credentials, freely accessible online, compiled primarily from infostealer malware logs. Not 16 million. 16 billion.
This blog explains what credential stuffing is and how it works, where the credentials come from, what the attack looks like technically, what happened to real organizations in 2025, and how to detect and stop it before the damage is done.
| 22% of all confirmed 2025 breaches started with stolen credentials (Verizon DBIR) | 160% surge in credential theft volume in the first half of 2025 (Check Point) | 16B login credentials in a single 2025 aggregated dark web dataset | 19% of all authentication attempts on major platforms are credential stuffing (Verizon) |
What Is Credential Stuffing?
Credential stuffing is an automated cyberattack in which threat actors take large collections of stolen username-and-password pairs (called combolists) and systematically test them against online services, applications, and enterprise portals. The attack is built on a single behavioral fact: most users reuse passwords across multiple services.
According to the Verizon 2025 DBIR report, which we contributed to as Brandefense, in an average scenario, only 49% of a user’s passwords across different services are unique. This means that for any given user, the probability of stolen credentials from one platform also unlocking their account on a completely different platform is approximately 50%. In a password database containing hundreds of millions of pairs, even a 0.5% success rate would result in hundreds of thousands of compromised accounts.
How Is Credential Stuffing Different from Brute Force?
| Brute Force | Credential Stuffing | |
| What is tested | Generated password guesses | Real stolen username + password pairs |
| Skill required | Moderate, wordlist generation, hashcat | Low, run a script, buy a list |
| Detection signal | High many failed attempts per account | Low, one attempt per account, per service |
| MFA stops it? | Usually yes | Partially, depends on MFA type |
| Attack scale | Single target, high volume | Thousands of targets, one attempt each |
| Cost to attacker | Time + compute | $2-$20 for a combolist on dark web |
| Success driver | Weak passwords | Password reuse |
Where Do the Credentials Come From? The Supply Chain Behind Every Attack
Credential stuffing attacks do not begin with the attack itself. They begin with the supply chain that produces the credential lists a multi-tier criminal ecosystem that has become as structured and commercialized as any legitimate software industry.
Tier 1: Infostealer Malware — The Primary Harvest Engine
The dominant source of fresh credentials in 2025 is infostealer malware. Families such as LummaC2, RedLine, Vidar, and Raccoon are deployed on victim devices (typically via phishing emails, malicious downloads, or trojanized software) and silently extract every saved credential from the browser’s local storage, along with session cookies, autofill data, and cryptocurrency wallet information.
The extracted data is packaged into structured log files and transmitted to attacker-controlled infrastructure within minutes of infection. These logs contain not just passwords, but the exact URLs where each credential was used; making it trivial to sort the harvest by service type and sell credentials at premium prices to buyers who want access to a specific platform.
In 2025, infostealer malware stole an estimated 1.8 billion credentials globally. The scale is not accidental, infostealer operations are offered as Malware-as-a-Service (MaaS), with subscription-based access available on dark web forums for as little as a few hundred dollars per month, enabling operators with no malware development skills to run large-scale credential harvesting campaigns.
Tier 2: Historical Breach Databases – The Long Tail of Past Incidents
Every major data breach that has ever exposed usernames and passwords eventually makes its way into aggregated credential databases distributed across dark web forums. These databases are compiled, deduplicated, and sorted — then sold, traded, and shared across the criminal ecosystem for years after the original breach occurred.
In April 2025, researchers at Synthient documented an aggregated database containing 2 billion unique email-and-password pairs compiled from countless prior breaches, circulating actively in credential stuffing communities. In June 2025, a separate compilation of approximately 30 different datasets was discovered openly accessible online, containing 16 billion login credentials. The dataset included passwords for accounts at Google, Apple, major social platforms, and government services — and was immediately recognized as providing a definitive blueprint for industrial-scale credential stuffing.
| ⚠️ The Dormant Credential Problem Not all credential-based breaches happen immediately after theft. In March 2025, 270,000 customer support tickets from a major electronics manufacturer’s German operations were leaked by a threat actor — traced back to a credential compromise from 2021. The credential had sat dormant for four years before being used. Organizations that assume past breaches are resolved are operating with a false sense of security. |
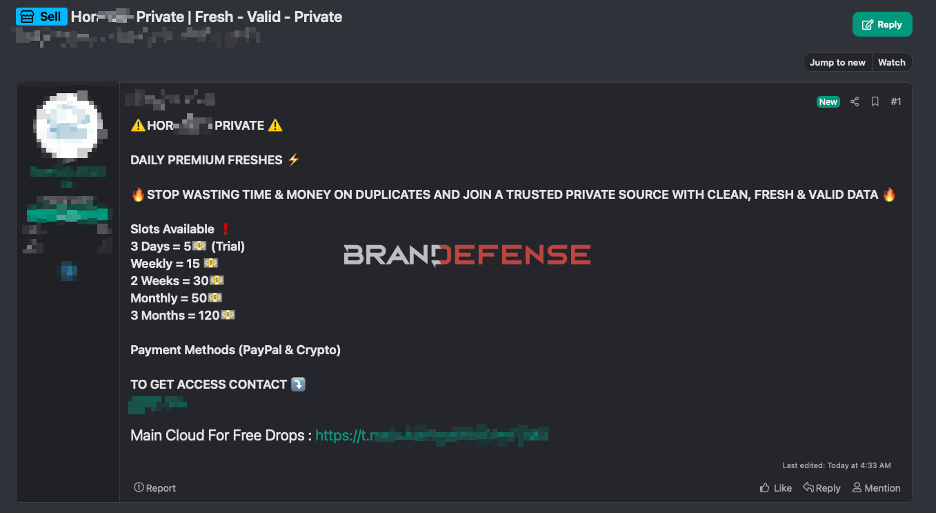
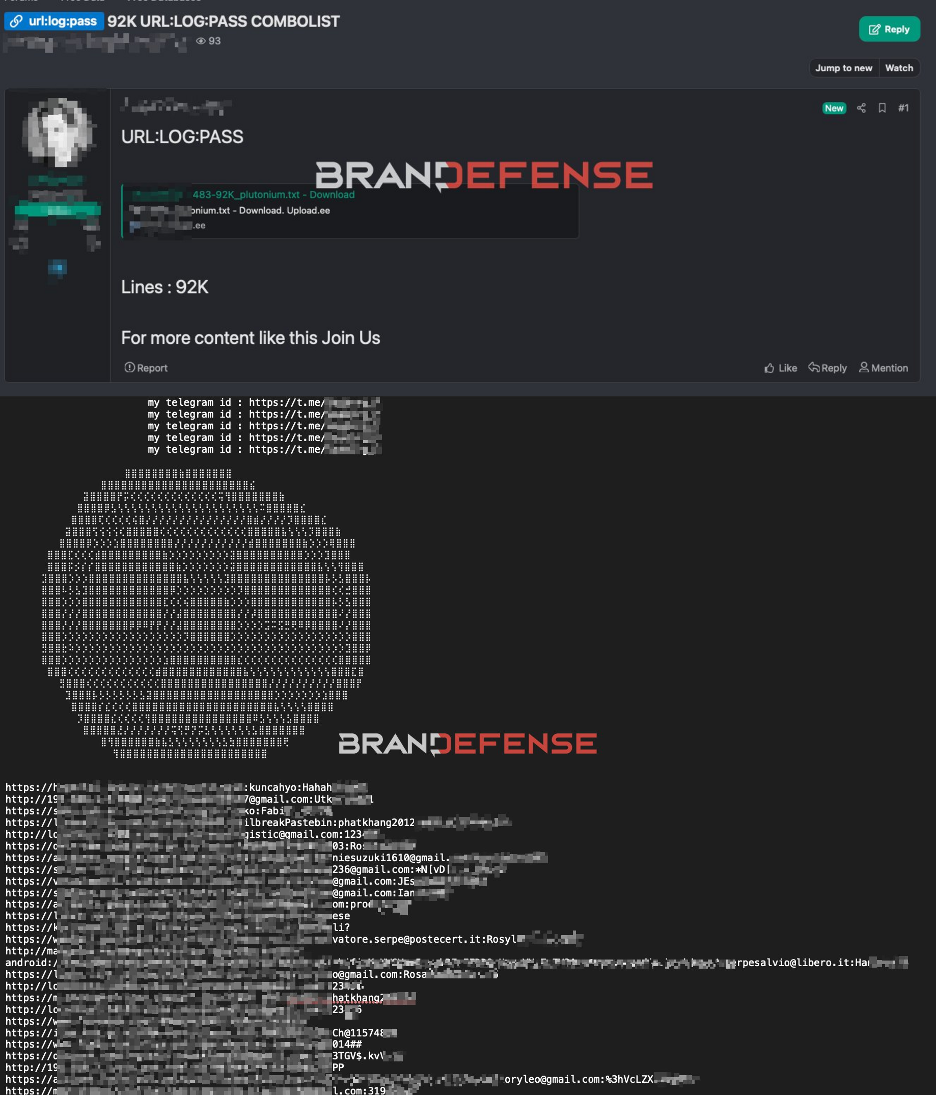
Tier 3: Combolist Marketplaces – Where Credentials Become Commodities
Between infostealer operators and the attackers who run credential stuffing campaigns sits a structured marketplace layer. Combolists (files containing email:password pairs sorted by service type, geography, or account value) are actively bought and sold on dark web forums and Telegram channels. Pricing follows a clear economic logic: freshness and validity rate determine price.
Fresh lists built from recent infostealer logs — where the credentials have not yet been rotated — command significantly higher prices because they have higher validity rates. Aged database dumps from historical breaches are cheaper, but still economically viable given the volume available and the low cost of running automated testing tools. A combolist of 10 million credentials for a specific streaming platform or e-commerce site might sell for as little as $20.
How Does a Credential Stuffing Attack Work? The Technical Anatomy
From the attacker’s perspective, a credential stuffing campaign is a data pipeline problem: how do you test millions of credential pairs against a target service as fast as possible, while evading the detection mechanisms designed to stop you?
Step 1: List Acquisition and Preprocessing
The attacker acquires a combolist relevant to their target, either by purchasing it from a dark web marketplace, extracting it from a fresh infostealer log, or assembling it from multiple public breach databases. The list is then preprocessed: duplicate pairs are removed, the format is normalized to the tool’s requirements (typically email:password or username:password), and optionally filtered by domain to target users of a specific service.
Step 2: Tool Configuration and Proxy Setup
The attacker configures an automated credential testing tool, commercial tools designed for penetration testing are frequently repurposed, while the criminal ecosystem also offers dedicated credential stuffing tools optimized for specific platforms. The most critical configuration element is the proxy network: residential or datacenter proxies are used to distribute login attempts across thousands of different IP addresses, preventing rate-limiting and IP-based blocking from interrupting the attack.
Modern credential stuffing tools are engineered to mimic legitimate browser behavior: they rotate user-agent strings, simulate mouse movement patterns, and handle CAPTCHA challenges through integration with CAPTCHA-solving services (human-powered or AI-based) that are also sold as commercial services in the same criminal ecosystem.
Step 3: Execution – One Attempt Per Account, Across Thousands of Services
The attack executes at scale: each credential pair is tested once against the target service. This deliberate throttling (one attempt per account) is the key detection evasion technique. Traditional brute-force detection looks for many failed login attempts against a single account. Credential stuffing distributes the attempts: each account sees only one failed attempt, from a different IP address, with a legitimate-looking browser signature.
The Verizon 2025 DBIR found that credential stuffing accounts for a median of 19% of all daily authentication attempts on major platforms. That means roughly one in five login attempts on a typical enterprise SSO or consumer platform is not a real user, it is an automated test of a stolen credential. Most of these attempts fail and leave no meaningful alert.
Step 4: Hit Validation and Account Monetization
When a credential pair successfully authenticates, the tool logs the ‘hit’ and the attacker begins the monetization phase. Valid credentials are sorted by account type and value: financial accounts, corporate SSO sessions, and e-commerce accounts with stored payment methods command the highest prices and are acted on most rapidly. The window between a successful credential stuffing hit and the account being accessed for fraud or resale is often measured in hours.
| 💡 Why Detection Is So Difficult A credential stuffing attack, from the target platform’s perspective, looks like a large number of failed login attempts but each failure comes from a different IP address, uses a different user-agent, and targets a different user account. No individual account triggers lockout. No individual IP exceeds rate limits. The attack is statistically invisible unless you are analyzing authentication patterns at the platform level rather than the account level. |
2025 Case Studies: What Credential Stuffing Actually Costs
CASE STUDY 1 — March 2025 // Financial Sector // Coordinated Multi-Target Attack
Australian Superannuation Funds: AUD 500,000 Stolen in a Single Weekend
On March 29-30, 2025, attackers launched coordinated credential stuffing attacks against five major Australian retirement fund platforms simultaneously: AustralianSuper, Rest Super, Hostplus, Australian Retirement Trust, and Insignia Financial. The coordination was deliberate attacking multiple targets in parallel limits each platform’s ability to share threat intelligence in time to prevent the others from being affected.
The attackers used combolists assembled from prior, unrelated breaches credentials that had nothing to do with the targeted retirement funds. They worked because the fund members had reused passwords from other services. AustralianSuper had MFA available but did not enforce it as a mandatory login requirement a gap that regulators subsequently identified as the primary enabling factor in the attack.
Four AustralianSuper members lost a combined AUD 500,000. Approximately 8,000 Rest Super members had personal data accessed. The attack required no technical sophistication beyond the ability to run a credential stuffing tool against the target platforms. The entry cost (a combolist of Australian financial service credentials) would have been a fraction of the stolen amount.
| 5 Superannuation funds targeted simultaneously in a single 48-hour window | AUD 500K stolen from confirmed compromised accounts in the initial attack | 8,000 Rest Super members with personal data accessed |
💡 Key Lesson — Unforced MFA Is Not Protection MFA that users can opt out of, or that is not enforced at login, provides no protection against credential stuffing. Attackers know which platforms enforce MFA at login and which make it optional. Optional MFA translates directly to a larger pool of attackable accounts in every combolist that covers that platform.
CASE STUDY 2 — April 2025 // Retail Sector // Repeat Targeting
The North Face / VF Corporation: Fourth Credential Stuffing Incident Since 2020
On April 23, 2025, VF Corporation notified customers of a new credential stuffing attack against The North Face online store. The attackers used previously leaked credentials (not credentials stolen directly from VF Corporation) to access customer accounts and expose personal data including names, email addresses, shipping addresses, phone numbers, purchase history, and dates of birth.
This was the fourth credential stuffing incident affecting VF Corporation brands since 2020. The pattern illustrates a structural problem in credential security: organizations that do not enforce mandatory MFA and do not continuously monitor for their customers’ credentials appearing in combolists will face repeat attacks. Each successful campaign against a consumer brand validates the combolist and drives further attacks against the same target.
| 🔴 The Repeat Attack Problem When a credential stuffing attack succeeds against a specific brand, that success is noted in criminal forums. The combolist gets updated with confirmed hits, the tool config for that platform gets refined and shared, and the attack is repeated often by different actors who purchase the validated subset of the combolist. Organizations that do not structurally address the root causes after a first incident should expect a second, third, and fourth attack. |
How to Detect Credential Stuffing in Progress
Because credential stuffing is engineered to evade per-account detection mechanisms, detecting it requires shifting the analysis from the account level to the platform or network level. The signals are there they are simply distributed across authentication logs in ways that are invisible to standard alerting rules.
Authentication Log Anomalies
The most reliable in-platform signal for credential stuffing is a statistical anomaly in authentication failure patterns. Normal authentication failure rates for a consumer platform are typically in the 1-3% range. A credential stuffing attack that accounts for 19% of daily authentication attempts (as observed by Verizon) will push the platform-wide failure rate significantly above baseline. This signal requires aggregated authentication analytics, not per-account alerting.
Geographic and ASN Velocity Anomalies
Even with proxy rotation, credential stuffing campaigns leave fingerprints in the distribution of authentication source IP addresses. An attack using a datacenter proxy network will show authentication attempts from data center ASNs at volumes disproportionate to legitimate user traffic from those locations. Residential proxy networks are harder to distinguish, but still produce geographic velocity patterns that diverge from the platform’s normal user distribution.
Dark Web Credential Monitoring – The Proactive Layer
The most operationally actionable detection approach is monitoring for your organization’s credentials appearing in combolists and stealer logs before they are used in an attack. When a combolist targeting your platform is assembled and distributed on dark web forums, there is typically a window of hours to days before the attacking campaign runs. Organizations with continuous dark web monitoring can detect the appearance of their users’ credentials, initiate forced password resets, and enforce MFA before the stuffing campaign executes.
| 🔍 The 94-Day Remediation Gap Check Point research found that when credentials are leaked through GitHub repositories, organizations take an average of 94 days to remediate revoking or rotating the exposed credentials. For dark web combolist exposure, the equivalent gap is often even longer because most organizations have no visibility into their credentials’ appearance in criminal markets. Brandefense closes this gap with continuous monitoring and real-time alerting. |
How to Defend Against Credential Stuffing – A Practical Checklist
No single control eliminates credential stuffing the attack’s success depends on a combination of password reuse behavior, platform authentication design, and the absence of credential exposure visibility. Effective defense addresses all three layers.
| PLATFORM AUTHENTICATION CONTROLS | |
| ✓ | Enforce MFA at login, not as an optional feature. Optional MFA is equivalent to no MFA from a credential stuffing perspective. FIDO2/hardware keys are the most resistant; SMS-based OTP remains vulnerable to real-time interception. |
| ✓ | Implement bot detection and behavioral analytics on your authentication endpoint analyze authentication velocity, ASN distribution, user-agent patterns, and failure rates at the platform level rather than the account level. |
| ✓ | Deploy CAPTCHA on login flows while not impenetrable, it raises the cost of automated credential testing and filters out lower-sophistication stuffing tools that do not integrate CAPTCHA-solving services. |
| ✓ | Implement breached password detection check submitted credentials against known breach databases at login and force reset when a match is found. Microsoft and Google provide this natively; third-party services exist for custom implementations. |
| CREDENTIAL INTELLIGENCE AND MONITORING | |
| ✓ | Monitor dark web combolist marketplaces and stealer log distributions continuously for your organization’s domain credentials like employee accounts, service accounts, and customer credentials that include your platform’s domain. |
| ✓ | Establish credential rotation workflows triggered by dark web exposure alerts when your credentials appear in a combolist, forced resets should be initiated within hours, not weeks. |
| ✓ | Monitor infostealer log feeds for device infections within your organization a device running an infostealer will exfiltrate every saved credential in the browser, including corporate SSO, email, and cloud platform logins. |
| ✓ | Track combolist mentions of your brand or platform on criminal forums when a new config file for your platform is posted or a targeted combolist appears, you want to know before the campaign runs. |
| USER BEHAVIOR AND IDENTITY HYGIENE | |
| ✓ | Enforce unique password requirements 49% of user passwords are not distinct across services. Password managers reduce the friction of unique passwords to near zero; mandate their use for corporate accounts. |
| ✓ | Conduct regular credential hygiene awareness the technical controls are defeated by password reuse. Users who understand that their old breach exposure is actively being tested against their current accounts change behavior more reliably than users who receive abstract security training. |
| ✓ | Implement privileged account separation corporate administrator and service account credentials should never share passwords with any external service. These accounts are the highest-value targets in any combolist that includes your domain. |
How Brandefense Detects Credential Stuffing Threats Before the Attack Runs
Credential stuffing attacks are preceded by a supply chain that is entirely visible on the dark web if you know where to look. Brandefense’s Threat Intelligence platform monitors the sources, marketplaces, and distribution channels that supply attackers with the credentials they need, providing early warning at each stage of the attack pipeline.
| Brandefense Capability | What It Detects |
| Stealer Log Monitoring | Continuous scanning of infostealer log distributions for your organization’s domain credentials like employee accounts, partner credentials, and service account logins appearing in fresh stealer output |
| Combolist Marketplace Surveillance | Monitoring of dark web forums, Telegram channels, and credential marketplaces for combolists targeting your domain or platform detecting supply-side preparation before the campaign executes |
| Credential Exposure Alerting | Real-time alerts when your employees’ or customers’ credentials appear in newly discovered breach databases, combolists, or stealer log aggregations triggering forced reset workflows before attackers test the credentials |
| Dark Web Forum Intelligence | Tracking of forum threads where credential stuffing tool configs for your platform are shared or discussed providing early warning when attackers are specifically preparing to target your service |
| Breach Database Correlation | Continuous correlation of your organization’s email domains against newly discovered breach databases identifying historical exposure that may not yet have been rotated |
| 24/7 Analyst Coverage | All detections are supported by continuous analyst review, with escalation for high-severity exposure events requiring immediate credential rotation or platform response |
Credential stuffing will not stop. The supply chain that produces combolists (infostealer malware, breach database aggregation, and dark web distribution) is industrialized, automated, and growing. In 2025, 16 billion credentials were in a single accessible dataset. The organizations that avoid becoming case studies are not those with the strongest password policies. They are those with the earliest warning.