Critical RCE Alarm in Sophos Firewall Solutions
A critical 0-day security vulnerability that affects Sophos Firewall solutions has been identified and is known to be actively exploited by threat actors.
The RCE vulnerability, tracked as CVE-2022-3236, exists due to incorrect login validation in the User Portal and WebAdmin interfaces of Sophos Firewall solutions. As a result, an unauthenticated, remote threat actor can execute arbitrary code on the target system via a specially crafted request.
The vulnerability affects all versions of Sophos Firewall 17.0.0 (inclusive) to 19.0.1. Sophos has released updates that fix the vulnerability. To avoid being affected by attacks that can be carried out using the vulnerability, it is recommended that users minimize the internet exposure of the User Portal and Webadmin interface and apply the published updates immediately.
Tarfile: The 15 Years Old Critical Python Vulnerability Affects More Than 350,000 Projects
A critical security vulnerability has been identified in Python that has not been updated for 15 years, leaving more than 350,000 open source projects vulnerable to attacks.
The vulnerability tracked as CVE-2007-4559 exists in the “Tarfile” module of Python, which is widely used in frameworks created by Netflix, AWS, Intel, Facebook, Google, and applications used for machine learning, automation, and docker containerization available via file. The tarfile module makes it possible to read and write tar archives, including gzip, bz2 and lzma compressed files. A successful exploit allows threat actors to execute arbitrary code on the vulnerable system or take control of a target system.
There is no update or mitigation suggestion to fix the said vulnerability. Therefore, thousands of Python projects are still vulnerable to vulnerability. In this context, it is recommended that the updates that are likely to be published regarding the vulnerability should be followed regularly and implemented immediately if published.
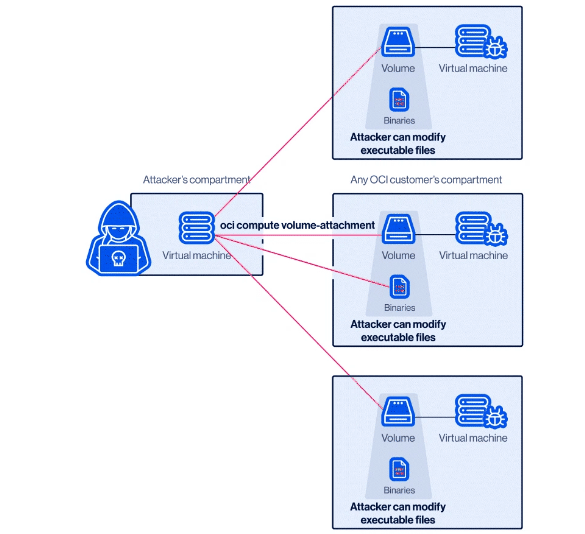
AffectMe: The Critical Vulnerability in Oracle Cloud Infrastructure
A critical security vulnerability has been identified in the Oracle Cloud infrastructure,called AttachMe, that threat actors can exploit to access the virtual disks of Oracle customers.
The vulnerability, AttachMe, compromises the security of cloud isolation by allowing threat actors to access other users’ OCI storage volumes without permission, capture and modify sensitive data stored on the volume, and execute code on affected systems. Successfully exploiting the vulnerability requires threat actors to capture the Oracle Cloud Identifier provided to an Oracle Cloud Infrastructure user and insert it into their Oracle Cloud virtual machine. Oracle Cloud infrastructure does not have a security mechanism that checks who owns this identifier. Therefore, threat actors can easily add the identifier to their virtual machines and gain access to the storage units of the Cloud customer that owns the identifier.