APT19 is an advanced persistent threat (APT) group that has engaged in sustained cyber espionage operations for over a decade. It has also operated many large-scale credential harvesting campaigns. This group occupies a unique place within the Chinese-nexus cyber threat landscape, using traditional state-assisted intelligence gathering methods as well as cybercrime-type methods, such as the mass harvesting of credentials and access brokers.
APT19 operates under multiple aliases; this proliferation of names reflects its wide operational scope and overlaps in activity clusters among groups. Its aliases include, but are not limited to the following: BRONZE FIRESTONE, Black Vine, Checkered Typhoon, Codoso, DEEP PANDA (also known as G0009), G0073, Group 13, KungFu Kittens, PinkPanther, Pupa, Shell Crew, Sunshop Group, TEMP.Avengers, and WebMasters. However, regardless of the diversity of names associated with APT19, the consistent patterns of infrastructure, malware, and/or victimology demonstrate that this is the same entity acting in a coherent operational manner.
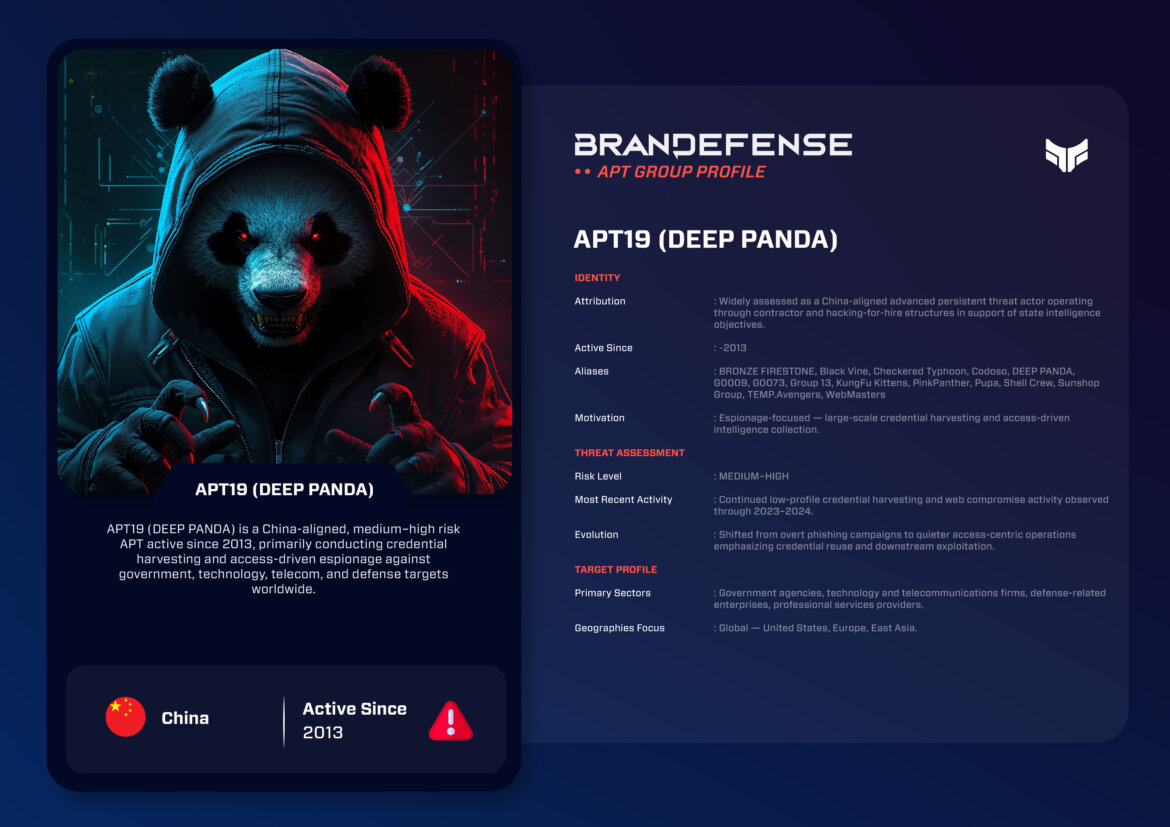
Identity and Attribution
The APT19 threat group is understood to have been established to support the nation’s intelligence efforts in China. Many of their members are reportedly Chinese citizens with hacking-for-profit skills who are acting like contractors or businesses; in addition to being involved with espionage totally aligned with Chinese government needs, many report on their work to one or more of the associated contractors, thus creating a dual-use capability (i.e., a means in addition to collecting intelligence).
Our understanding of APT19 as a hybrid structure is critical in understanding why APT19 has been so willing to execute wide-ranging and often opportunistic campaigns that generate the credentials necessary for the acquisition of the significant amounts of credentials, which could be subsequently filtered for intelligence value.
Strategic Motivation
Strategically, APT19’s primary motive can be characterized as meaning that it is primarily interested in acquiring information of all types involving political, economic, or technological significance. In contrast to traditional state-sponsored espionage, APT19 has shown a clear interest in acquiring large quantities of credentials. These large numbers of credentials allow APT19 to gain access to various corporate, cloud, and personal accounts, allowing APT19 access and intelligence long after initial compromise.
APT19 will choose its targets based on the perceived intelligence value, but will also compromise serviceman or managed services in order to access multiple lower-tier victims. This access-oriented targeting methodology aligns with central tasks of Chinese intelligence prioritization in accordance with their needs for situational awareness and access over a long-term view.
Tactics, Techniques, and Procedures (TTPs)
APT19 has combined phishing, website compromise, and credential harvesting with disciplined operational persistence as their tradecraft.
Initial Access
Typically, APT19 will obtain initial access via spear-phishing campaigns containing malicious attachments or links. Spear-phishing emails may appear as valid business communications, conference invitations or as security alerts. In addition, initial access has also been obtained via compromised web servers and content management systems (CMS) through the deployment of web shells, allowing APT19 to maintain access to the compromised hosting environment.
Execution and Persistence
After gaining initial access, APT19 obtains and deploys lightweight backdoors and web shells to establish and maintain persistence. Persistence mechanisms include registry changes and scheduled tasks on endpoint systems, while web shells implemented on compromised servers provide long-term access without detection and are resilient to partial remediation efforts.
Credential Harvesting
APT19’s operations represent a pattern for the theft of credentials from its victims. The group utilizes:
– Keyloggers – Browser credential dumping
– Phishing websites using compromised infrastructure
APT19 often reuses credentials stolen from one platform on multiple application platforms which allows for lateral movement into email, VPN and other cloud-based services.
Command and Control
APT19 uses HTTP/HTTPS-based C2 channels for its operations. Command and control infrastructure is frequently reset and domain names are designed to appear legitimate, often disguising as established or legitimate businesses and/or technology service providers. The use of compromised servers as relay nodes for both inbound and outbound command-and-control communications has made determining attribution extremely difficult.
Malware and Tooling
APT19 is a threat group that employs many tools and malware families with an emphasis on credential theft and maintaining access, as opposed to sophisticated exploitation. Among these are custom backdoors, web shells and credential harvesting utilities. The APT19 group develops its own tools as well as tailoring public tools to remain undetected and integrate seamlessly into their operational workflow.
Instead of focusing on zero-day exploits, APT19 prefers to use tried-and-true methods that are deployable across a variety of environments repeatedly.
Target Profile
APT19’s targets reflect both strategic intelligence objectives and opportunistic access to obtain intelligence information.
Primary Targets
– Government Agencies/Public Sector
– Companies in Technology/Telecommunications
– Companies in the Defense Industry
– Consultants/Professional Services
Geographic Focus
APT19 has targeted organizations in globes, with significant activity in:
– United States
– Europe
– East Asia
APT19 has extended their reach into multiple geographies/industries by compromising service providers.

Notable Operations
Significant operations have connected APT19 with many important initiatives.
- The first instance was between 2013 and 2016 when they conducted numerous cyberattack attempts to acquire users credentials through phishing emails and using web shells.
- Later in 2016-2017 there was significant compromise of many managed service providers and the cloud, allowing access to a number of organizations and victims.
- In 2018 members of APT19 were publicly indicted for being involved with hacking for hire.
- In 2019 until the present (2023) there have been continued smaller-scale operations being run in the same pattern (the same type as previous).
These campaign activities show that APT19 is still continuing its activity regardless of government oversight of the group.
Evolution and Current Activity
Since the public indictments by the United States and the press, the group has continued to conduct its cyber operations; however, they have changed the visibility and tempo of their operations to be more discreet.
Analysts stated that while the group appears to have significantly decreased their overt operations based on historical observations of their own operations, they do continue to conduct campaigns that are easily traced to APT19s tradecraft suggesting they have reorganized rather than ceased operations.
APTs tactics, techniques, and procedures, primarily in relation to acquiring user credentials and selling access to users, has had the effect of causing many non-state actors and state-sponsored actors to utilize APT19’s TTPs thereby creating a gray area or no distinction at all between the two types of actor in the threat landscape.
Threat Assessment
The APT19 cyber espionage group is recognized as posing a medium-to-high risk against entities worldwide. Although not recognized as the most technically challenged group, APT19 engages in a methodical access-based (as opposed to technical novelty based) approach to conducting its espionage which renders them a particularly dangerous adversary. Long-term access and second-level exploitation via compromised credentials also lead to a greater level of risk for those organizations targeted by APT19.
Organizations affected by APT19 activities may also experience a cascading effect due toward stolen credentials being reused or resold, which leads to an extended impact beyond the initial intrusion.
Defensive Considerations
To effectively defend against APT19 organizations must concentrate their defenses upon identity and access protections:
– Implement strong phishing detection mechanisms and ensure that all users are well trained in recognizing phishing attempts.
– Use MFA for all external services.
– Monitor for anomalous credential usage.
– Conduct regular audits of web servers and hosting environments.
By maintaining proper credential hygiene organizations can reduce the principle operational advantage that enables APT19 (and similar threat actors) to be successful in conducting espionage.
Conclusion
APT19 demonstrates a hybrid model of espionage that integrates Government-directed intelligence objectives with large-scale credential theft. By focusing on access and continued access over technical ingenuity, APT19 remains relevant despite continually changing/advancing defenses.
As such, as identity-based attacks continue to evolve at an increasing rate, the lessons learned from APT19 (e.g., APT19’s techniques may provide insight into how malicious actors may leverage stolen/compromised credentials to attain a strategic advantage at the global level).
You can download and review the sheet for all the details!







