Turla stands out as one of the Russian-linked advanced persistent threat (APT) groups because of its advanced ability to persist and its longevity as an APT group. Turla is also known as: Snake, Uroburos, Waterbug, VENOMOUS Bear, and Secret Blizzard. Turla has been active since the early 2000s and has been tracking and collecting information on behalf of Russian intelligence services through cyber espionage. Turla’s distinguishing characteristic is the development and use of modular and stealthy malware families, including but not limited to, Snake, Carbon, Epic Turla, and Kazuar. The malware has mainly used in sustained campaigns targeting government, defense contractors, and foreign diplomatic missions.
As we enter 2025, Turla remains an advanced threat actor that persists with cryptic ability and alters toolsets and tactics to embed itself in sensitive networks across Europe, North America and beyond. This blog will provide an exploration into the identity of Turla, its associated tactics, attention-grabbing operations, and relevant configuration rotations.
Identity & Motivation
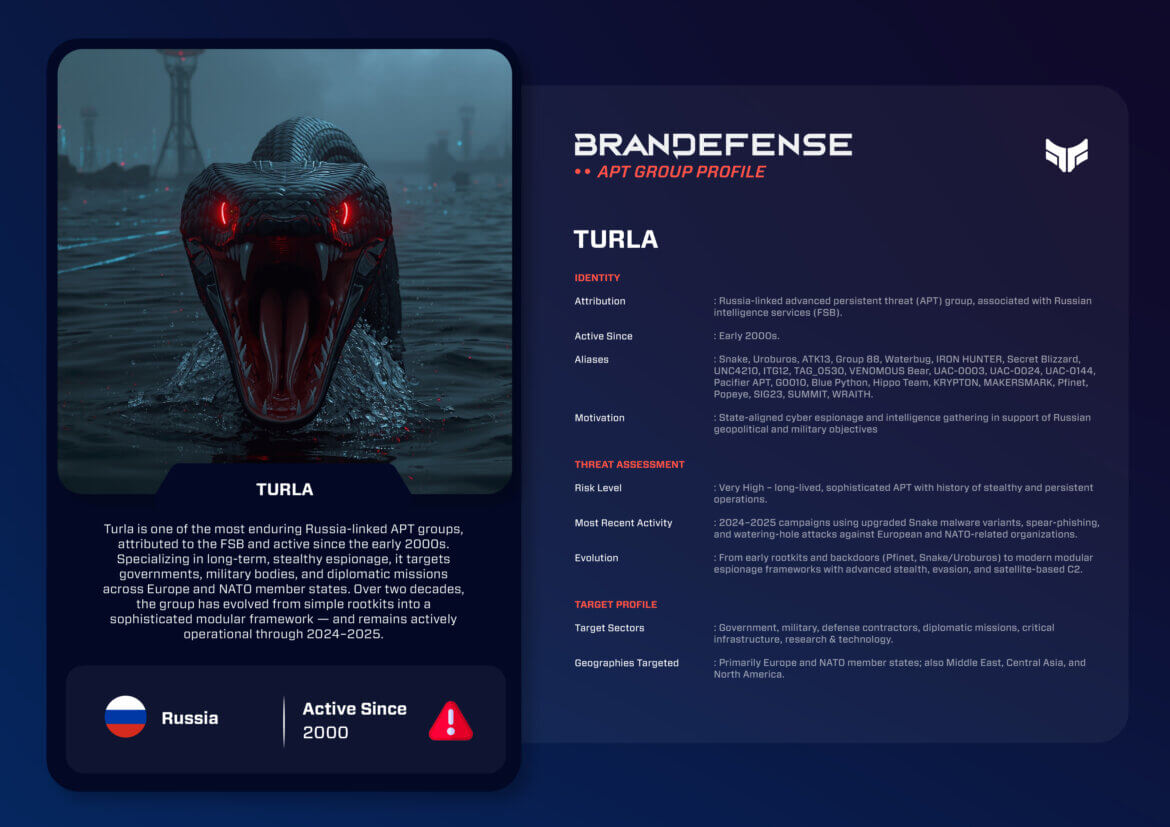
- Attribution: Russian state-affiliated, as widely attributed to the Federal Security Service (FSB).
- Active Since: Early 2000s.
- Aliases: Snake, Uroburos, ATK13, Group 88, Waterbug, IRON HUNTER, Secret Blizzard, UNC4210, ITG12, TAG_0530, VENOMOUS Bear, UAC-0003, UAC-0024, UAC-0144, Pacifier APT, G0010, Blue Python, Hippo Team, KRYPTON, MAKERSMARK, Pfinet, Popeye, SIG23, SUMMIT, WRAITH.
- Motivation: Long-term cyber espionage, in service of Russian geopolitical, military, and diplomatic objectives.
The mission for Turla does not have a financial motivation. Rather, the grouping aims to maintain to indefinite access to high-value targets, gather sensitive information, and degrade adversaries of Russia through covert and indefinite operations.
TTPs: Methods, Tools, and Persistence
Turla is known for its innovation and ability to conduct operations under the radar for long durations.
Initial Access:
– Spear-phishing using malicious attachments or links.
– Watering-hole attacks on highly-valued targets.
– Supply chain compromises.
– Exploiting vulnerabilities regarding VPNs and public-facing servers.
Persistence and Lateral Movement:
– The use of a Snake/Uroburos rootkit for holy-grail, long-term stealthy access.
– Scheduled tasks, registry manipulations, and trojanized software.
– Credential theft and privileged escalation to expand methods across networks.
C2 (Command & Control):
– Satellite-based C2 channels to obfuscate attribution and monitoring for detection.
– Multi-hop proxy chains and using compromised infrastructure.
– Encrypted HTTPS and domain fronting.
Malware/Tools:
– Snake/Uroburos: Modular rootkit/backdoor, flagship tool.
– Carbon: Modular espionage framework used for prolonged operations.
– Kazuar: Backdoor with .NET components linked to later activity related to SolarWinds. – Epic Turla: Reconnaissance toolkit for initial compromise.
– Pfinet/Gazer: Espionage implants.
Techniques:
– Living-off-the-land (LOLBins) execution.
– Long-term stealth and persistence through advanced rootkits.
– Credential harvesting, exfiltration of sensitive documents.
Target Profile
Turla regularly attacks high-value geopolitical sectors:
– Government ministries and agencies.
– Military and defense contractors
– Diplomatic missions and embassies.
– Providers of critical infrastructure.
– Research and technology organizations.
Geographies: Primary focus is on Europe and NATO countries, but operations also extend to the Middle East, Central Asia and North America.

Notable Operations
- 2008–2014: Deployment of the Snake / Uroburos rootkit against European governments, including C2 techniques based on satellite communications.
- 2015–2017: Turla and Carbon were used in espionage campaigns against European and Middle Eastern diplomatic missions.
- 2018–2020: Attacks in the Middle East and Central Asian governments and the use of the Kazuar backdoor associated with the SolarWinds supply chain compromise.
- 2021–2023: Increased targeting of NATO and European defense targets, utilizing advanced backdoors and leveraging multi-hop C2.
- 2024–2025: Renewed Snake activity targeting European ministries and associated with NATO, exploiting VPN vulnerabilities and designed around a proxy infrastructure.
Recent Activities (2024–2025)
Recent activity indicates Turla continues to enhance its operations:
- Updated Snake Malware: Analysts reported new variants of the Snake Malware that enhance stealth and modularity.
- VPN Exploitation: Turla continues to exploit VPN appliances as point of entry into government and defense networks.
- Enhanced Proxy Chains: Multi-layered proxy chains disguised their infrastructure; complicating attribution and response.
- Integration of Kazuar: Continued usage of Kazuar, which demonstrates linkage across Russian APT toolsets.
Strategic Impact
Turla’s employment of advanced cyber capabilities exemplifies Russia’s shift of focus from conventional military forces to a reliance on technological capabilities to use them as a geopolitical tool:
– Strategic Espionage: Turla’s sustained operation in NATO and European networks provides an understanding of its policy and military strategies over the long-term.
– Persistent Threat: Turla employs rootkits and its satellite command-and-control intent demonstrates an operational objective of remaining undetected for years.
– Global Risk: Turla’s operations span not only Europe but also the Middle East and North America. Such capabilities indicate its ambition is evolving beyond Europe.
Defensive Takeaways
Organizations can protect themselves from Turla by implementing layered defenses:
– Use phishing-resistant MFA and hardened access controls.
– Implement advanced EDR/XDR capable of rootkits or stealthy implants utilized for decades.
– Monitor for anomalous satellite or proxy C2 traffic.
– Threat hunt for Snake, Carbon, Kazuar, and Epic Turla IOCs.
– Enforce segmentation and least-privilege within sensitive networks.
Conclusion
Turla (Snake) is one of the most advanced and persistent Russian APT groups. Operating for over two decades, Turla has shown resilience, adaptability, and a unique capability to remain dormant within victim networks for sustained periods of time. Turla’s operational activities targeting European governments, NATO organizations, and critical infrastructure reveal Moscow’s long-term espionage priorities.
As of 2025, Turla’s upgraded Snake malware, along with enhanced C2 techniques and stealthy persistence, reinforce Turla’s strategic role as a cyber weapon for Russia. Defenders must treat Turla not as a temporary threat, but a long-term counter adversary that requires continuous monitoring, sharing of intelligence, and proactive defense.
You can download and review the sheet for all the details!







