FortiOS Vulnerability Allows Hackers to Take Down Firewall Devices
FortiOS Vulnerability Exploited by Hackers in Targeted Attacks Against Governments and Large Organizations
Hackers exploit a severe vulnerability, CVE-2022-41328, in FortiOS – an operating system widely used by governments and large organizations. This flaw enables them to execute arbitrary code and has already caused data loss and system corruption in targeted organizations. The vulnerability affects various versions of FortiOS, but the fix is available in the latest updates. Fortinet, the vendor, is closely monitoring the situation.
Understanding the seriousness of this FortiOS vulnerability is critical!
Hackers have already used it to breach government and large organizations’ systems. A recent report from Fortinet revealed that threat actors had hacked and taken down multiple FortiGate firewall devices belonging to one of its clients using CVE-2022-41328 exploits, even though the flaw’s advisory did not explicitly state that the vulnerability had been exploited before patches were available.
According to Bleepingcomputer, threat actors are using a critical FortiOS vulnerability to launch attacks against government agencies and large-scale organizations. These attacks are causing data loss, operating systems, and file corruption in the targeted organizations’ inventory.
“Don’t fall prey to cybercrime! The FortiOS vulnerability is no joke – hackers have already exploited it to breach top government and corporate systems. Stay informed and stay secure!”
It is crucial for organizations to update their FortiOS installations to the latest version as soon as possible to avoid falling victim to this vulnerability. Additionally, organizations should review their security policies and ensure that proper security measures, such as firewalls, intrusion detection and prevention systems, and network segmentation, are in place to mitigate the risk of cyber attacks.
Regular security assessments and vulnerability scans can help organizations identify and address potential security issues before malicious actors exploit them. In addition, organizations can consider engaging with third-party security experts to conduct penetration testing and other security assessments to identify any vulnerabilities in their systems. By taking these proactive steps, organizations can better protect themselves against the increasing threat of cyber-attacks and safeguard their sensitive data and systems from unauthorized access and data breaches.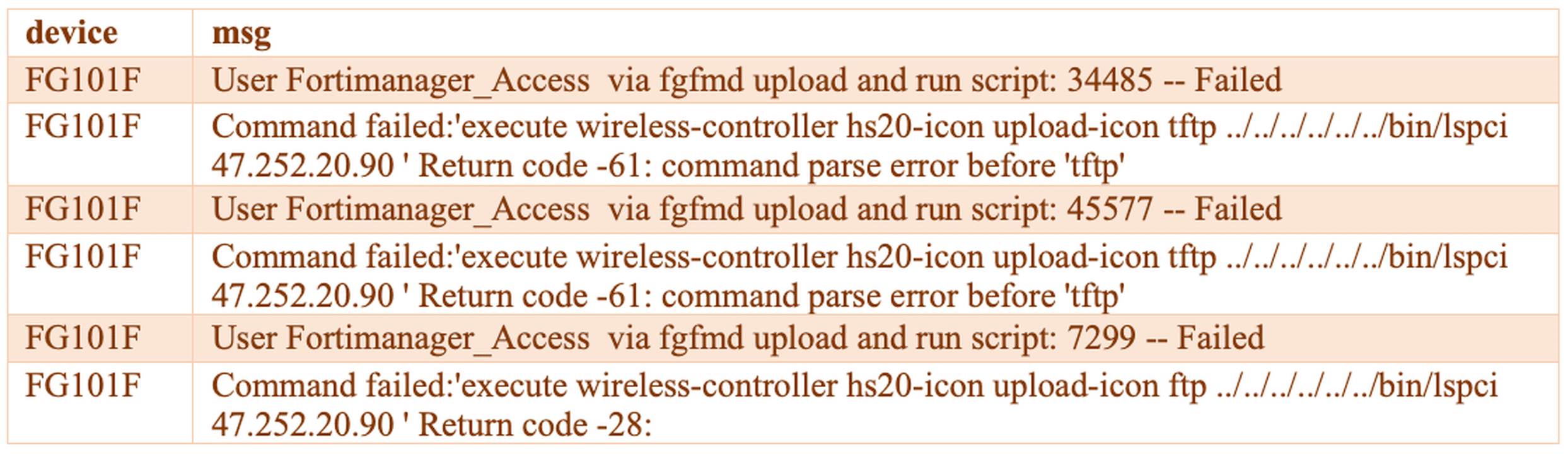
The vulnerability can lead to arbitrary code execution in vulnerable systems
CVE-2022-41328, is a path traversal vulnerability that vulnerability arises from an authentication error while processing a specific CLI command and affects the following FortiOS versions;
- 6.0,
- 6.2,
- 6.4.0 – 6.4.11,
- 7.0.0 – 7.0.9,
- 7.2.0 – 7.2.3
The updates that address the vulnerability are available in versions;
- 6.4.12
- 7.0.10
- 7.2.4
Threat Actors Manipulating Firmware to Gain Control of FortiGate Devices
The attacks targeting the organization’s inventory were initially detected when a customer’s multiple FortiGate devices suddenly stopped working and encountered a boot error.
They found that the devices had stopped with the following error message: “System enters error mode due to FIPS error: Firmware Integrity self-test failed.” FIPS-enabled devices verify the integrity of system components. If a breach of integrity is detected, the device shuts down and rejects the boot to protect network integrity.[pix_cta cta_style=”default” btn_text=”Click here” btn_target=”true” btn_size=”md” btn_effect=”” btn_hover_effect=”” btn_add_hover_effect=”” style=”” hover_effect=”” add_hover_effect=”” title=”Don’t Let Vulnerabilities Take Down Your Systems – Try Our Vulnerability Intelligence Solution Today!” btn_link=”https://brandefense.io/request-a-demo/?utm_source=Cvescannertool&utm_medium=secnews”][/pix_cta]FORTINET investigations revealed that threat actors changed the /sbin/init component in the device’s firmware image and added a new file named /bin/fgfm as the first stage of the attack chain. This change allows /bin/fgfm to run before normal startup actions, providing an attacker with continued access and control. Further stages of the attack involved executing malicious code on the targeted systems.
Fortinet is continuing to monitor the threat actors associated with this attack. In this context, to avoid falling victim to similar attacks targeting organizations’ inventories, ensuring that the internal inventory is always in the latest updated version, where vulnerabilities are fixed, is recommended. In addition, regularly monitoring network traffic and logs can also help to detect malicious activity quickly.
To prevent further damage, users of FortiOS must update their systems immediately. Regular network traffic and logs monitoring can help identify any suspicious activities early. Taking these precautions will help protect against future attacks and safeguard the integrity of your systems.
It is essential to be aware of this critical FortiOS vulnerability as it has been used in attacks targeting government institutions and large-scale organizations, resulting in data loss and corruption. Organizations using FortiOS should update their systems to the latest available versions immediately to mitigate the risk of being affected by this vulnerability. Regular network traffic and logs monitoring can also help quickly detect malicious activity. These steps can help prevent attacks on internal inventory and protect network integrity.